Copy Microcontroller P87C51X2BBD Binary
Copy Microcontroller P87C51X2BBD Binary
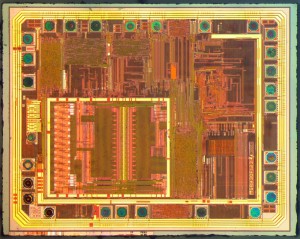
Copy Microcontroller P87C51X2BBD Binary from locked memory include flash and eeprom, remove the security fuse bit of MCU P87C51X2 by MCU Cracking technology and readout firmware from opened Microprocessor
Copy Microcontroller P87C51X2BBD Binary from locked memory include flash and eeprom, remove the security fuse bit of MCU P87C51X2 by MCU Cracking technology and readout firmware from opened Microprocessor;
FEATURES
· 80C51 Central Processing Unit
– 4 kbytes ROM/EPROM (P80/P87C51X2)
– 8 kbytes ROM/EPROM (P80/P87C52X2)
– 16 kbytes ROM/EPROM (P80/P87C54X2)
– 32 kbytes ROM/EPROM (P80/P87C58X2)
– 128 byte RAM (P80/P87C51X2 and P80C31X2)
– 256 byte RAM (P80/P87C52/54X2/58X2 and P80C32X2)
– Boolean processor
– Fully static operation
– Low voltage (2.7 V to 5.5 V at 16 MHz) operation
· 12-clock operation with selectable 6-clock operation (via software or via parallel programmer)
· Memory addressing capability
– Up to 64 kbytes ROM and 64 kbytes RAM
· Power control modes:
– Clock can be stopped and resumed
– Idle mode
– Power-down mode
· CMOS and TTL compatible
· Two speed ranges at VCC = 5 V
– 0 to 30 MHz with 6-clock operation
– 0 to 33 MHz with 12-clock operation
· PLCC, DIP, TSSOP or LQFP packages
· Extended temperature ranges
· Dual Data Pointers
· Security bits:
– ROM (2 bits)
– OTP (3 bits)
· Encryption array – 64 bytes
· Four interrupt priority levels
· Six interrupt sources
· Four 8-bit I/O ports
· Full-duplex enhanced UART
– Framing error detection
– Automatic address recognition
· Three 16-bit timers/counters T0, T1 (standard 80C51) and additional T2 (capture and compare)
· Programmable clock-out pin
· Asynchronous port reset
· Low EMI (inhibit ALE, slew rate controlled outputs, and 6-clock mode)
· Wake-up from Power Down by an external interrupt.
Circuit Engineering Company Limited continues to be recognized as the Southern China Leader in Services for IC Break, MCU recover, Chip Recover, Microcontroller Copy service. With the advancement of today’s modern circuit board technology, it is more important than ever to have specialists available to help you at a moment’s notice. Our engineering and commercial teams collectively have a vast amount of electronic experience covering field include Consumer Electronics, Industrial Automation Electronics, Wireless Communication Electronics., etc. For more information please contact us through email.
 Copy MCU ATmega32A Software
Copy MCU ATmega32A Software
Microcontrollers like the ATmega32A play a critical role in modern embedded systems across industries—from consumer electronics to industrial automation and automotive controls. The ATmega32A is a powerful 8-bit AVR MCU from Microchip, known for its performance, versatility, and reliability. It features built-in flash, EEPROM, and SRAM memory blocks, supporting a wide range of applications such as smart devices, control units, security systems, and robotics.
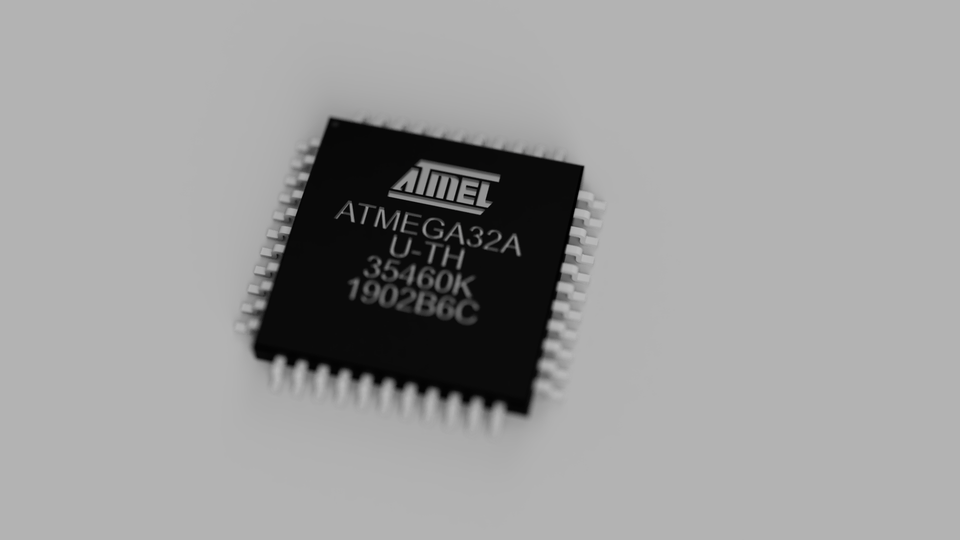
However, the same features that make the ATmega32A a preferred choice for manufacturers also make it challenging for users to access or modify its content. When an ATmega32A chip is protected, locked, or encrypted, extracting its firmware, binary, or heximal program can become nearly impossible without specialized knowledge and tools.
That’s where we come in.
At CIRCUIT ENGINEERING CO.,LTD, we provide professional services to copy MCU ATmega32A software and crack the protection mechanisms used to secure its internal data. Whether you’re dealing with read-protected flash, encrypted EEPROM, or secured configuration files, we use advanced techniques to restore, decode, decrypt, or even hack the device to give you access to the original source code or usable firmware images.

Our services include:
- Firmware Dumping: Extracting and decoding binary data from ATmega32A flash and EEPROM, even when protected.
- Protection Bypass: Using hardware-level and software-based tools to crack lock bits and unlock secured memory areas.
- Decompilation & Analysis: Translating raw firmware into readable source code (C or assembly) for analysis, modification, or replication.
- Program Cloning: Clone, duplicate, or archive ATmega32A firmware for backup, production, or reverse engineering purposes.
Whether you need to copy, open, or duplicate an existing system, or simply understand how a locked unit works, we offer reliable and confidential solutions tailored to your project requirements.
Copy MCU ATmega32A Software from master microcontroller ATmega32A program memory, and reprogramme the firmware into blank new Microprocessor ATmega32A for MCU cloning;

Our team has deep expertise in embedded hardware reverse engineering and secure firmware extraction. We use cutting-edge tools and non-destructive methods to ensure successful copying and restoration of protected programs without damaging your devices.
We also understand the sensitivity of working with proprietary or commercial IP, which is why every project is handled with the strictest confidentiality.
Features
· High-performance, Low-power AVR® 8-bit Microcontroller
· Advanced RISC Architecture
– 131 Powerful Instructions – Most Single-clock Cycle Execution
– 32 x 8 General Purpose Working Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
High Endurance Non-volatile Memory segments
– 32K Bytes of In-System Self-programmable Flash program memory after firmware MCU PIC16F84 extraction
– 1024 Bytes EEPROM
– 2K Byte Internal SRAM
– Write/Erase Cycles: 10,000 Flash/100,000 EEPROM
– Data retention: 20 years at 85°C/100 years at 25°C(1)
– Optional Boot Code Section with Independent Lock Bits
· In-System Programming by On-chip Boot Program
· True Read-While-Write Operation
– Programming Lock for Software Security
JTAG (IEEE std. 1149.1 Compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– One 16-bit Timer/Counter with Separate Prescaler, Compare Mode, and Capture Mode
– Real Time Counter with Separate Oscillator
– Four PWM Channels
– 8-channel, 10-bit ADC
· 8 Single-ended Channels
· 7 Differential Channels in TQFP Package Only
· 2 Differential Channels with Programmable Gain at 1x, 10x, or 200x
– Byte-oriented Two-wire Serial Interface
– Programmable Serial USART
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with Separate On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Six Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, Standby and Extended Standby
I/O and Packages
– 32 Programmable I/O Lines
– 40-pin PDIP, 44-lead TQFP, and 44-pad QFN/MLF
Operating Voltages
– 2.7 – 5.5V for ATmega32A
Speed Grades
– 0 – 16 MHz for ATmega32A
Power Consumption at 1 MHz, 3V, 25°C for ATmega32A
Summary
– Active: 0.6 mA
– Idle Mode: 0.2 mA
– Power-down Mode: < 1 µA
The ATmega32A microcontroller features 32KB of programmable flash memory, 2KB SRAM, and 1KB EEPROM, along with 32 general-purpose I/O lines, multiple timers, ADC channels, and UART/SPI interfaces. It is widely used in:
- Industrial automation and control panels
- Smart home devices
- Access control and security systems
- Mechatronics and robotics
- Custom embedded electronics
Because of its popularity, many legacy systems still rely on ATmega32A. In situations where firmware source code is lost, or a system integrator has gone out of business, the ability to restore or copy a locked firmware image is essential for maintenance, replication, or system upgrades.
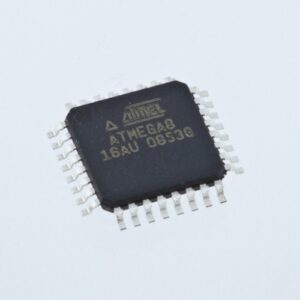
 Attack Chip ATmega8A Binary
Attack Chip ATmega8A Binary
Microcontrollers like the ATmega8A are widely used in industrial, automotive, and consumer electronics due to their reliability and performance. However, when these chips are locked, encrypted, or protected, accessing their internal firmware, EEPROM, or flash memory becomes a difficult task. Whether you’re trying to recover legacy data, analyze a secured program, or clone a binary for backup, such protection mechanisms can be a significant obstacle. That’s where our service comes in—we specialize in attacking chip ATmega8A binary to unlock, dump, and decode the embedded content safely and professionally.

Microcontroladores como el ATmega8A son la base de innumerables sistemas embebidos, desde maquinaria industrial hasta dispositivos de consumo. Estos chips suelen almacenar lógica propietaria en forma de firmware, incrustada en la memoria flash y EEPROM interna. Para proteger la propiedad intelectual, los fabricantes habilitan funciones de seguridad que hacen ilegibles los archivos binarios internos. Pero ¿qué ocurre si el acceso es esencial, por ejemplo, para restaurar datos perdidos, copiar un programa heredado o clonar un dispositivo para mantenimiento? Ahí es donde entramos nosotros. En Circuit Engineering CO.,LTD, nos especializamos en técnicas avanzadas para atacar el binario del chip ATmega8A, lo que permite a los clientes decodificar, descifrar y extraer firmware bloqueado de microcontroladores protegidos.
Our Procedure to Attack the ATmega8A MCU
Our work involves several well-defined stages to effectively crack or clone the firmware archive locked inside a protected ATmega8A microcontroller:
1. Chip Identification and Analysis
We begin by confirming the target chip’s identity (ATmega8A) and examining its configuration. This includes analyzing fuse bits, lock bits, and memory layout to understand the level of security protection in place.
2. Non-Invasive Techniques First
Before turning to advanced methods, we test non-invasive approaches using ISP (In-System Programming) and HVPP (High-Voltage Parallel Programming). If basic access is blocked, we escalate to more complex methods.
3. Glitching and Side-Channel Attacks
In many cases, the ATmega8A uses fuse bits to disable further reading of the flash or EEPROM. We use power glitching and clock fault injection to temporarily bypass these security mechanisms. These methods target precise timing windows to trick the microcontroller into allowing memory access.
4. Dumping Embedded Memory
Once access is granted, we proceed to dump the protected EEPROM and flash memory. This includes the entire binary file, including heximal firmware and other program data stored within the chip.
5. Post-Extraction Analysis
After a successful extraction, we convert the raw dump into structured formats—such as C source code or binary files—depending on your needs. We can also help decrypt or decode proprietary formats and rebuild the firmware archive for testing or migration purposes.
6. Optional: Cloning or Duplicating
We offer a complete chip duplication service—allowing you to clone the ATmega8A firmware and write it to another identical MCU, even replicating the original protection settings if needed.
Attack Chip ATmega8A secured system, unlock microcontroller ATmega8A flash and eeprom memory, extract binary from both of the memories in the format of heximal which can be used for microcontroller copying
Attack Chip ATmega8A secured system, unlock microcontroller ATmega8A flash and eeprom memory, extract binary from both of the memories in the format of heximal which can be used for microcontroller copying;
Features
· High-performance, Low-power AVR® 8-bit Microcontroller
· Advanced RISC Architecture
– 130 Powerful Instructions – Most Single-clock Cycle Execution
– 32 x 8 General Purpose Working Registers when Chip PIC16F84A binary copying
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
High Endurance Non-volatile Memory segments
Mikrokontrolery takie jak ATmega8A są sercem niezliczonych systemów wbudowanych — od maszyn przemysłowych po urządzenia konsumenckie. Te układy często przechowują zastrzeżoną logikę w formie oprogramowania układowego, osadzonego w wewnętrznej pamięci flash i EEPROM. Aby chronić własność intelektualną, producenci włączają funkcje bezpieczeństwa, które sprawiają, że wewnętrzne pliki binarne są nieczytelne. Ale co, jeśli dostęp jest niezbędny — na przykład w celu przywrócenia utraconych danych, skopiowania starszego programu lub sklonowania urządzenia w celu konserwacji? Tutaj wkraczamy my.W Circuit Engineering CO.,LTD specjalizujemy się w zaawansowanych technikach atakowania binarnego układu ATmega8A, umożliwiając klientom dekodowanie, odszyfrowywanie i wyodrębnianie zablokowanego oprogramowania układowego z chronionych mikrokontrolerów.
– 8K Bytes of In-System Self-programmable Flash program memory
– 512 Bytes EEPROM
– 1K Byte Internal SRAM
– Write/Erase Cycles: 10,000 Flash/100,000 EEPROM
– Data retention: 20 years at 85°C/100 years at 25°C(1)
– Optional Boot Code Section with Independent Lock Bits
· In-System Programming by On-chip Boot Program
· True Read-While-Write Operation
8-bit with 8K Bytes In-System Programmable
– Programming Lock for Software Security
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescaler, one Compare Mode
– One 16-bit Timer/Counter with Separate Prescaler, Compare Mode, and Capture Mode
– Real Time Counter with Separate Oscillator after IC C8051F530 Firmware attacking
– Three PWM Channels
– 8-channel ADC in TQFP and QFN/MLF package
· Eight Channels 10-bit Accuracy
– 6-channel ADC in PDIP package
· Six Channels 10-bit Accuracy
– Byte-oriented Two-wire Serial Interface
– Programmable Serial USART
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with Separate On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Five Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, and Standby
I/O and Packages
– 23 Programmable I/O Lines
– 28-lead PDIP, 32-lead TQFP, and 32-pad QFN/MLF
Operating Voltages
– 2.7 – 5.5V for ATmega8A
Speed Grades
– 0 – 16 MHz for ATmega8A
Power Consumption at 4 Mhz, 3V, 25°C
Flash ATmega8A
– Active: 3.6 mA
– Idle Mode: 1.0 mA
– Power-down Mode: 0.5 µA
Why Choose Our Service?
-
Experience with Embedded Security: We’ve helped clients across industries restore lost firmware from secured embedded systems and open protected programs blocked by manufacturers.
-
Wide Range of Tools: From logic analyzers to electromagnetic glitchers, our lab is equipped to crack secured chips with minimal risk of damage.
-
Confidential & Compliant: We treat every project with strict confidentiality and compliance, especially when dealing with proprietary or legacy systems.
-
Custom Support: Need help with just the memory dump? Or a full firmware decoding and source reconstruction? We tailor our service to your requirements.
Conclusion
If you’re facing a locked or encrypted ATmega8A and need to extract, copy, or decrypt the embedded program, we provide a proven, professional solution. From glitching protected chips to duplicating complex firmware files, we help our clients regain access and control over their embedded systems.
ATmega8A जैसे माइक्रोकंट्रोलर अनगिनत एम्बेडेड सिस्टम के दिल में हैं – औद्योगिक मशीनरी से लेकर उपभोक्ता उपकरणों तक। ये चिप्स अक्सर फ़र्मवेयर के रूप में मालिकाना तर्क संग्रहीत करते हैं, जो आंतरिक फ़्लैश और EEPROM मेमोरी के भीतर एम्बेडेड होते हैं। बौद्धिक संपदा की सुरक्षा के लिए, निर्माता सुरक्षा सुविधाएँ सक्षम करते हैं जो आंतरिक बाइनरी फ़ाइलों को अपठनीय बनाती हैं। लेकिन क्या होगा यदि पहुँच आवश्यक है – शायद खोए हुए डेटा को पुनर्स्थापित करने, विरासत प्रोग्राम की प्रतिलिपि बनाने या रखरखाव के लिए डिवाइस को क्लोन करने के लिए? यहीं पर हम आते हैं। सर्किट इंजीनियरिंग CO.,LTD में, हम चिप ATmega8A बाइनरी पर हमला करने की उन्नत तकनीकों में विशेषज्ञ हैं, जो क्लाइंट को संरक्षित माइक्रोकंट्रोलर से लॉक किए गए फ़र्मवेयर को डिकोड, डिक्रिप्ट और निकालने में सक्षम बनाता है।
Contact us to learn how we can help you attack chip ATmega8A binary and recover what’s rightfully yours—securely, efficiently, and legally.
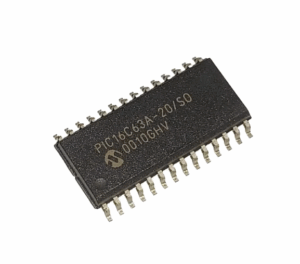
 Attack Microcontroller PIC16C63A Heximal
Attack Microcontroller PIC16C63A Heximal
In the realm of embedded systems, Microchip’s PIC16 series microcontrollers are widely used for their reliability, simplicity, and broad integration into industrial and commercial electronics. However, these microcontrollers often come with protective mechanisms that prevent unauthorized access to their embedded firmware, especially in legacy models like the PIC16C63A. At CIRCUIT ENGINEERING CO.,LTD, we offer advanced solutions to attack Microcontroller PIC16C63A heximal, allowing our clients to crack, decode, and restore valuable program data locked behind layers of secured flash memory.
oferecemos soluções avançadas para atacar o Microcontrolador PIC16C63A Heximal, permitindo que nossos clientes quebrem, decodifiquem e restaurem dados valiosos de programas bloqueados por camadas de memória flash segura. Quando a documentação original é perdida ou você precisa clonar um dispositivo legado para manutenção ou substituição, o acesso ao conteúdo binário original torna-se crítico. Infelizmente, segmentos de EEPROM e flash bloqueados ou criptografados frequentemente dificultam esses esforços. É aí que nosso serviço de ataque a microcontroladores se torna essencial. Utilizamos técnicas especializadas para descriptografar, copiar e extrair o arquivo de programa heximal de microcontroladores protegidos, oferecendo acesso total ao código-fonte original ou à sua forma mais próxima possível.
Why Attack a Protected PIC16C63A?
When original documentation is lost, or you need to clone a legacy device for maintenance or replacement, accessing the original binary content becomes critical. Unfortunately, locked or encrypted EEPROM and flash segments often hinder such efforts. That’s where our microcontroller attack service becomes essential. We use specialized techniques to decrypt, copy, and extract the heximal program file from secured microcontrollers, giving you full access to the original source code or its closest possible form.
Tailored Process for PIC16C63A Firmware Extraction
Here’s how we approach each project involving the PIC16C63A:
1. Device Preparation
We begin by identifying the exact chip configuration, including memory layout, protection fuses, and voltage thresholds. The PIC16C63A typically features code protection bits that prevent straightforward access, so our team uses non-invasive and semi-invasive hardware probing techniques to prepare the device for data access.
2. Protection Bypass
The core of the process involves unlocking the protected flash memory. Depending on the device’s revision, we may exploit known vulnerabilities or employ glitching and fault injection techniques to bypass the microcontroller’s security. This phase is where we essentially attack the microcontroller PIC16C63A heximal at the hardware level.
3. Memory Dump
Once the protection is bypassed, we directly interface with the chip’s memory and dump the firmware, EEPROM data, and other critical content. This archived binary is often saved as a .hex file, representing the raw machine code the device runs.
4. Reverse Engineering (Optional)
If required, we can take the extracted heximal firmware and decode it into more readable assembly language or even decompiled C source code, making it easier to analyze or repurpose for your application.
5. Validation and Cloning
The final phase involves testing the duplicated program file by reprogramming it into a compatible blank microcontroller, ensuring it operates identically to the original. This allows you to clone, backup, or modify the firmware for future development or troubleshooting.

हम मेमोरी लेआउट, सुरक्षा फ़्यूज़ और वोल्टेज थ्रेसहोल्ड सहित सटीक चिप कॉन्फ़िगरेशन की पहचान करके शुरू करते हैं। PIC16C63A में आमतौर पर कोड सुरक्षा बिट्स होते हैं जो सीधे एक्सेस को रोकते हैं, इसलिए हमारी टीम डिवाइस को डेटा एक्सेस के लिए तैयार करने के लिए गैर-आक्रामक और अर्ध-आक्रामक हार्डवेयर जांच तकनीकों का उपयोग करती है।, प्रक्रिया के मूल में संरक्षित फ्लैश मेमोरी को अनलॉक करना शामिल है। डिवाइस के संशोधन के आधार पर, हम ज्ञात कमजोरियों का फायदा उठा सकते हैं या माइक्रोकंट्रोलर की सुरक्षा को बायपास करने के लिए गड़बड़ और दोष इंजेक्शन तकनीकों को नियोजित कर सकते हैं। यह वह चरण है जहाँ हम अनिवार्य रूप से हार्डवेयर स्तर पर माइक्रोकंट्रोलर PIC16C63A हेक्सिमल पर हमला करते हैं।, एक बार सुरक्षा को बायपास कर देने के बाद, हम सीधे चिप की मेमोरी से जुड़ते हैं और फ़र्मवेयर, EEPROM डेटा और अन्य महत्वपूर्ण सामग्री को डंप करते हैं। यह संग्रहीत बाइनरी अक्सर .hex फ़ाइल के रूप में सहेजी जाती है, जो डिवाइस द्वारा चलाए जाने वाले कच्चे मशीन कोड का प्रतिनिधित्व करती है।
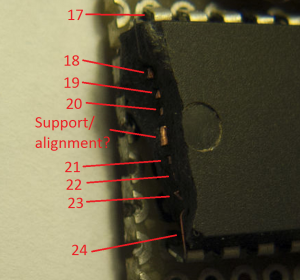
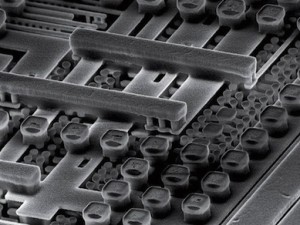
Attack Microcontroller PIC16C63A protective memory and readout heximal of MCU PIC16C63A flash memory, microprocessor PIC16C63A unlocking process will normally start from chip surface decapsulation;
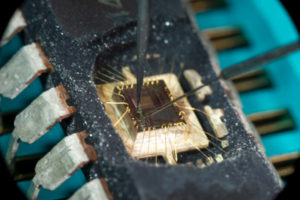
Attack Microcontroller PIC16C63A protective memory and readout heximal of MCU PIC16C63A flash memory, microprocessor PIC16C63A unlocking process will normally start from chip surface decapsulation
Devices included in this data sheet:
PIC16C7X Peripheral Features:
· Timer0: 8-bit timer/counter with 8-bit prescaler
· Timer1: 16-bit timer/counter with prescaler can be incremented during SLEEP via external
PIC16CXX Microcontroller Core Features:
· High performance RISC CPU
· Only 35 single word instructions to learn
· All single cycle instructions except for program branches which are two cycle
· Operating speed: DC – 20 MHz clock input
DC – 200 ns instruction cycle
· 4 K x 14 words of Program Memory,
192 x 8 bytes of Data Memory (RAM)
· Interrupt capability
· Eight-level deep hardware stack
· Direct, indirect and relative addressing modes
· Power-on Reset (POR)
· Power-up Timer (PWRT) and Oscillator Start-up Timer (OST)
· Watchdog Timer (WDT) with its own on-chip RC oscillator for reliable operation
· Programmable code protection
· Power-saving SLEEP mode crystal/clock
· Timer2: 8-bit timer/counter with 8-bit period register, prescaler and postscaler
· Capture, Compare, PWM modules
– Capture is 16-bit, max. resolution is 200 ns
– Compare is 16-bit, max. resolution is 200 ns
– PWM max. resolution is 10-bit
· 8-bit multichannel Analog-to-Digital converter
· Synchronous Serial Port (SSP) with SPITM and I2CTM
· Universal Synchronous Asynchronous Receiver Transmitter (USART/SCI)
· Parallel Slave Port (PSP), 8-bits wide with external RD, WR and CS controls when Attack Microcontroller
· Brown-out detection circuitry for Brown-out Reset (BOR) Pin Diagram: PDIP, Windowed CERDIP
· Selectable oscillator options
· Low power, high speed CMOS EPROM technology
· Wide operating voltage range: 2.5V to 5.5V
· High Sink/Source Current 25/25 mA
· Commercial, Industrial and Automotive temperature ranges
· Low power consumption:
– < 5 mA @ 5V, 4 MHz
– 23 mA typical @ 3V, 32 kHz
– < 1.2 mA typical standby current
Additional Device Support: PIC16CE625 and Beyond
In addition to the PIC16C63A, we also offer cracking and firmware duplication services for other secured MCUs like the PIC16CE625. These chips include embedded security features similar to the C63A and require precise techniques to unlock safely.
임베디드 시스템 분야에서 Microchip의 PIC16 시리즈 마이크로컨트롤러는 뛰어난 신뢰성, 단순성, 그리고 산업 및 상업용 전자 기기와의 폭넓은 통합성으로 널리 사용되고 있습니다. 하지만 이러한 마이크로컨트롤러는 특히 PIC16C63A와 같은 레거시 모델의 경우, 임베디드 펌웨어에 대한 무단 접근을 차단하는 보호 메커니즘을 갖추고 있는 경우가 많습니다. CIRCUIT ENGINEERING CO.,LTD는 마이크로컨트롤러 PIC16C63A Heximal을 공격하는 고급 솔루션을 제공하여 고객이 보안 플래시 메모리 계층에 잠긴 귀중한 프로그램 데이터를 해독, 디코딩 및 복원할 수 있도록 지원합니다. 보호된 PIC16C63A를 공격해야 하는 이유는 무엇일까요? 원본 문서가 분실되었거나 유지 관리 또는 교체를 위해 레거시 장치를 복제해야 하는 경우, 원본 바이너리 콘텐츠에 접근하는 것이 매우 중요합니다. 하지만 잠겨 있거나 암호화된 EEPROM 및 플래시 세그먼트는 이러한 접근을 어렵게 만드는 경우가 많습니다. 바로 이러한 경우, 당사의 마이크로컨트롤러 공격 서비스가 필수적입니다. 저희는 특수 기술을 사용하여 보안 마이크로컨트롤러에서 헥시멀 프로그램 파일을 복호화, 복사 및 추출하여 원본 소스 코드 또는 가장 유사한 형태에 대한 완전한 접근 권한을 제공합니다.
Conclusion
Whether you need to unlock, copy, or restore firmware from a protected PIC microcontroller, our team offers secure, legal, and confidential services tailored to your situation. By combining expert knowledge with cutting-edge tools, we make it possible to attack microcontroller PIC16C63A heximal and recover essential program files that others can’t reach.
Contact us today to find out how we can help you decrypt, clone, and recover your legacy or protected embedded system firmware.
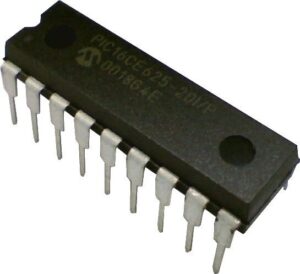
 Attack MCU PIC16CE625 Program
Attack MCU PIC16CE625 Program
How to Attack MCU PIC16CE625 Program and Dump Protected Firmware
Microchip’s PIC16CE625 is a popular 8-bit microcontroller frequently used in embedded applications due to its reliability and low power consumption. However, when its program memory is locked, encrypted, or protected, accessing the embedded firmware becomes a challenge—especially for engineers, analysts, or developers who need to clone, restore, or modify the system. At [Your Company Name], we specialize in attacking the MCU PIC16CE625 program to help clients unlock, decrypt, and extract its secured binary or heximal firmware.

Nuestro procedimiento para atacar la protección del MCU PIC16CE625 Análisis inicial: Comenzamos inspeccionando el chip objetivo con lupa y probando la instrumentación para identificar esquemas de protección y posibles puertas traseras. Conexión de la interfaz: Mediante técnicas de sondeo precisas, establecemos acceso físico a la memoria flash o EEPROM, a menudo mediante la interfaz directa de pines o el acceso a la traza de la PCB. Protección de bypass: Nuestro servicio se centra en explotar las vulnerabilidades conocidas en los mecanismos de protección de código del PIC16CE625. Dependiendo de la configuración, esto puede implicar fallos de alimentación, manipulación del reloj o microsondeo para desbloquear la memoria bloqueada. Volcado de firmware: Una vez evadida la protección, realizamos un volcado completo del archivo de firmware (incluyendo flash, EEPROM y bits de configuración) a un formato binario o hexadecimal legible.
Our Procedure to Attack PIC16CE625 MCU Protection
-
Initial Analysis: We begin by inspecting the target chip under magnification and test instrumentation to identify protection schemes and potential backdoors.
-
Interface Connection: Using precise probing techniques, we establish physical access to the flash or EEPROM memory, often through direct pin interfacing or PCB trace access.
-
Bypass Protection: The core of our service focuses on exploiting known vulnerabilities in the PIC16CE625’s code protection mechanisms. Depending on the configuration, this may involve power glitching, clock manipulation, or microprobing to crack the locked memory.
-
Firmware Dumping: Once protection is bypassed, we perform a full dump of the firmware archive—including flash, EEPROM, and configuration bits—into a readable binary or heximal format.
-
Reverse Engineering (Optional): We can optionally decode, decompile, or convert the dumped memory into C/C++ source code, enabling clients to review or reuse the logic for debugging, porting, or enhancement.
-
Verification & Delivery: The extracted program data is verified for integrity and then delivered to the client in the required format (e.g., binary file, Intel HEX, or disassembled source code).

Нашата процедура за атакуване на защитата на MCU PIC16CE625 Първоначален анализ: Започваме с проверка на целевия чип под увеличение и тестваме инструменти, за да идентифицираме схеми за защита и потенциални задни врати. Интерфейсна връзка: Използвайки прецизни техники за сондиране, ние установяваме физически достъп до флаш или EEPROM паметта, често чрез директно свързване на пинове или достъп до PCB трасиране. Защита от заобикаляне: Основата на нашата услуга е използването на известни уязвимости в механизмите за защита на кода на PIC16CE625. В зависимост от конфигурацията, това може да включва прекъсване на захранването, манипулиране на тактовата честота или микросондиране за разбиване на заключената памет. Дъмпинг на фърмуера: След като защитата бъде заобиколена, ние извършваме пълен дъмп на фърмуерния архив – включително флаш паметта, EEPROM и конфигурационните битове – в четлив двоичен или шестнадесетичен формат.
Services We Offer
We provide a complete solution to copy, clone, or duplicate the protected firmware of PIC16CE625 microcontrollers. Our techniques help clients overcome vendor lock-in, recover lost firmware, or analyze device behavior. All services are conducted with strict confidentiality and professionalism.
Whether you need to hack a legacy device, restore a lost firmware file, or unlock a secured embedded program, our experts can help you access the internal logic of the PIC16CE625 MCU.
Attack MCU PIC16CE625 locked memory and extract program from Microcontroller PIC16CE625 flash memory, disable the security fuse bit after crack Microprocessor PIC16CE625 so the microprobes will be able to get access to the internal memory
Attack MCU PIC16CE625 locked memory and extract program from Microcontroller PIC16CE625 flash memory, disable the security fuse bit after crack Microprocessor PIC16CE625 so the microprobes will be able to get access to the internal memory;
Interrupt capability 16 special function hardware registers
8-level deep hardware stack
Direct, Indirect and Relative addressing modes
Peripheral Features:
· 13 I/O pins with individual direction control
· High current sink/source for direct LED drive
· Analog comparator module with:
– Two analog comparators
– Programmable on-chip voltage reference (VREF) module
– Programmable input multiplexing from device inputs and internal voltage reference
– Comparator outputs can be output signals
· Timer0: 8-bit timer/counter with 8-bit programmable prescaler
Special Microcontroller Features:
· In-Circuit Serial Programming (ICSP™) (via two pins)
· Power-on Reset (POR)
· Power-up Timer (PWRT) and Oscillator Start-up Timer (OST)
· Brown-out Reset
· Watchdog Timer (WDT) with its own on-chip RC oscillator for reliable operation
PIC16CE625 MCU Korumasına Saldırma Prosedürümüz İlk Analiz: Hedef çipi büyütme altında inceleyerek ve koruma şemalarını ve olası arka kapıları belirlemek için enstrümantasyonu test ederek başlıyoruz. Arayüz Bağlantısı: Hassas sondaj teknikleri kullanarak, genellikle doğrudan pin arayüzü veya PCB iz erişimi yoluyla flaş veya EEPROM belleğine fiziksel erişim sağlıyoruz. Baypas Koruması: Hizmetimizin özü, PIC16CE625’in kod koruma mekanizmalarındaki bilinen güvenlik açıklarından yararlanmaya odaklanır. Yapılandırmaya bağlı olarak, bu, kilitli belleği kırmak için güç arızası, saat manipülasyonu veya mikro sondaj içerebilir. Ürün Yazılımı Dökümü: Koruma atlatıldıktan sonra, flaş, EEPROM ve yapılandırma bitleri dahil olmak üzere ürün yazılımı arşivinin tam bir dökümünü okunabilir bir ikili veya altıgen biçime dönüştürüyoruz. Tersine Mühendislik (İsteğe Bağlı): İsteğe bağlı olarak, dökülen belleği kod çözebilir, derleyebilir veya C/C++ kaynak koduna dönüştürebiliriz; böylece istemcilerin hata ayıklama, taşıma veya geliştirme için mantığı gözden geçirmesini veya yeniden kullanmasını sağlayabiliriz.
Special Microcontroller Features (cont’d)
· 1,000,000 erase/write cycle EEPROM data memory
· EEPROM data retention > 40 years
· Programmable code protection
· Power saving SLEEP mode
· Selectable oscillator options
· Four user programmable ID locations
CMOS Technology:
· Low-power, high-speed CMOS EPROM/EEPROM technology
· Fully static design
· Wide operating voltage range – 2.5V to 5.5V
· Commercial, industrial and extended temperature range
· Low power consumption
– < 2.0 mA @ 5.0V, 4.0 MHz
– 15 mA typical @ 3.0V, 32 kHz
– < 1.0 mA typical standby current @ 3.0V
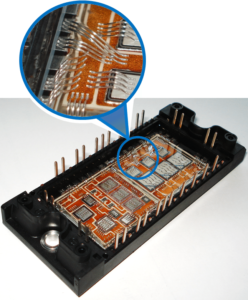
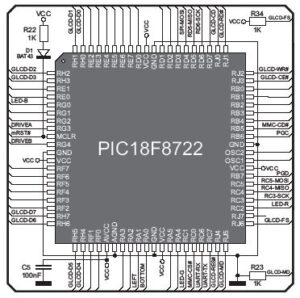
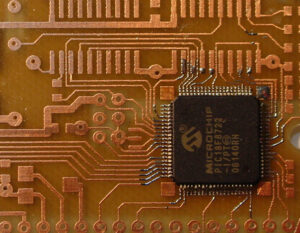
 Break Microcontroller PIC18F8722 Flash
Break Microcontroller PIC18F8722 Flash
The Microchip PIC18F8722 is a powerful 8-bit microcontroller widely used in industrial control, automotive systems, and commercial embedded products due to its rich peripheral set, 128 KB of flash memory, and built-in EEPROM. Its architecture supports enhanced features like 10-bit ADC, multiple communication modules (I2C, SPI, USART), and nanoWatt technology for power efficiency, making it a popular choice for complex, secured embedded applications.
However, when this microcontroller’s flash memory becomes protected, locked, or encrypted, accessing or modifying the internal program code, firmware, or data becomes nearly impossible without the proper tools and expertise. This is where our advanced microcontroller cracking service comes in — we help clients break Microcontroller PIC18F8722 Flash and gain access to the original binary, heximal, or even high-level source code.
Our Process: How We Crack the PIC18F8722
We follow a structured and professional procedure to ensure safe and accurate recovery or duplication of protected firmware:
Однако, когда флэш-память этого микроконтроллера становится защищенной, заблокированной или зашифрованной, доступ или изменение внутреннего программного кода, прошивки или данных становится практически невозможным без соответствующих инструментов и опыта. Вот тут-то и приходит на помощь наша передовая услуга по взлому микроконтроллеров — мы помогаем клиентам взломать флэш-память микроконтроллера PIC18F8722 и получить доступ к исходному двоичному, шестнадцатеричному или даже высокоуровневому исходному коду.
Initial Assessment: We begin by analyzing the target device to determine its security fuse configuration and possible memory protection mechanisms.
Hardware Setup: Using specialized programmers and decapping or voltage glitching methods (as required), we safely unlock the microcontroller’s flash and EEPROM areas.
Dump Extraction: We copy or clone the internal firmware, data, or program files from the secured memory, even if the content is encrypted or obfuscated.
Decode & Decrypt: If the firmware archive is encoded or compressed, we decode or decrypt it using custom-built reverse engineering tools to restore human-readable formats.
Analysis & Conversion: We can optionally disassemble or decompile the binary into assembly language or reconstruct it into C source code to aid in system restoration or replication.

Break Microcontroller PIC18F8722 Flash memory tamper resistance system off, and then extract IC PIC18F8722 code from flash memory, the content can be reprogrammed to new unit for Microcontroller PIC18F8722 cloning
Break Microcontroller PIC18F8722 Flash memory tamper resistance system off, and then extract IC PIC18F8722 code from flash memory, the content can be reprogrammed to new unit for Microcontroller PIC18F8722 cloning;
Power-Managed Modes:
Peripheral Highlights (Continued):
Run: CPU on, peripherals on
Idle: CPU off, peripherals on
Sleep: CPU off, peripherals off
Idle mode currents down to 15 µA typical
Sleep current down to 0.2 µA typical
Timer1 Oscillator: 1.8 µA, 32 kHz, 2V
Watchdog Timer: 2.1 µA
Two-Speed Oscillator Start-up
quando la memoria flash di questo microcontrollore diventa protetta, bloccata o crittografata, accedere o modificare il codice di programma interno, il firmware o i dati diventa quasi impossibile senza gli strumenti e le competenze adeguate. È qui che entra in gioco il nostro servizio avanzato di cracking dei microcontrollori: aiutiamo i clienti a rompere la memoria Flash del microcontrollore PIC18F8722 e ad accedere al codice sorgente originale binario, esadecimale o persino di alto livello.
· Three Enhanced Capture/Compare/PWM (ECCP) modules
– One, two or four PWM outputs
– Selectable polarity
– Programmable dead-time
– Auto-Shutdown and Auto-Restart
· Two Master Synchronous Serial Port (MSSP) modules supporting 2/3/4-wire SPI™ (all 4 modes) and I2C™ Master and Slave modes
Flexible Oscillator Structure:
· Four Crystal modes, up to 25 MHz
· 4X Phase Lock Loop (PLL) (available for crystal and internal oscillators)
· Two External RC modes, up to 4 MHz
· Two External Clock modes, up to 40 MHz
· Internal oscillator block:
– 8 user selectable frequencies, from 31 kHz to 8 MHz
– Provides a complete range of clock speeds from 31 kHz to 32 MHz when used with PLL
– User tunable to compensate for frequency drift
· Secondary oscillator using Timer1 @ 32 kHz
· Fail-Safe Clock Monitor:
– Allows for safe shutdown if peripheral clock stops External Memory Interface (PIC18F8627/8722 only):
· Address capability of up to 2 Mbytes
· 8-bit or 16-bit interface
Peripheral Highlights:
· Two Enhanced Addressable USART modules
– Supports RS-485, RS-232 and LIN 1.2
– RS-232 operation using internal oscillator block (no external crystal required)
– Auto-wake-up on Start bit
– Auto-baud detect
· 10-bit, up to 16-channel Analog-to-Digital Converter module (A/D)
– Auto-acquisition capability
– Conversion available during Sleep
· Dual analog comparators with input multiplexing
Special Microcontroller Features:
· C compiler optimized architecture:
– Optional extended instruction set designed to optimize re-entrant code
· 100,000 erase/write cycle Enhanced Flash program memory typical
· 1,000,000 erase/write cycle Data EEPROM memory typical
· Flash/Data EEPROM Retention: 100 years typical
· Self-programmable under software control
High current sink/source 25 mA/25 mA
Four programmable external interrupts
Four input change interrupts
Two Capture/Compare/PWM (CCP) modules
· Priority levels for interrupts
· 8 X 8 Single Cycle Hardware Multiplier
· Extended Watchdog Timer (WDT):
– Programmable period from 4 ms to 131s
· Single-supply In-Circuit Serial Programming™ (ICSP™) via two pins
· In-Circuit Debug (ICD) via two pins
· Wide operating voltage range: 2.0V to 5.5V
Applications and Use Cases
Our clients come from various sectors including automotive suppliers, industrial automation firms, and OEM electronics developers. They turn to us when they need to:
Restore lost firmware after damage or manufacturer discontinuation
Duplicate or clone a working device to preserve legacy systems
Hack into their own devices to analyze vulnerabilities or perform security audits
Unlock and open protected memory to perform custom modifications or enable additional features
Why Choose Us?
Deep expertise in firmware cracking, flash memory analysis, and secured embedded systems
Strict confidentiality and security protocols for all client data
Support for converting heximal dumps into usable source code
If you’re struggling with a locked PIC18F8722 or need to recover critical data from a protected microcontroller, we’re here to help. Contact us today to learn how we can break Microcontroller PIC18F8722 Flash and unlock the full potential of your embedded systems.
 Attack IC C8051F530 Firmware
Attack IC C8051F530 Firmware
The IC C8051F530 is a powerful 8-bit microcontroller from Silicon Labs, featuring an enhanced 8051 core, integrated analog and digital peripherals, and on-chip Flash memory and EEPROM. Commonly used in industrial control systems, commercial electronics, and IoT devices, the C8051F530 is designed for embedded applications that demand reliability, low power consumption, and compact design.
O processo para atacar e clonar o firmware do C8051F530 envolve várias etapas técnicas: Identificação do Dispositivo e Configuração da Interface Começamos analisando o encapsulamento e os protocolos de comunicação do microcontrolador. O C8051F530 suporta programação no sistema por meio de sua interface C2, que acessamos usando ferramentas de hardware personalizadas. Mapeamento de Memória e Bypass de Proteção Nosso próximo passo é avaliar as configurações de proteção da memória. Muitos sistemas protegidos habilitam a proteção contra leitura de código (CRP) para impedir a extração do firmware. Aplicamos métodos não invasivos e semi-invasivos para ignorar essas proteções, dependendo da configuração do sistema. Despejando Flash e EEPROM Uma vez obtido o acesso, procedemos à cópia ou duplicação do conteúdo da memória Flash, EEPROM e outros blocos de memória. Os dados binários ou hexagonais são então armazenados em arquivos para processamento posterior.
However, the firmware stored in the Flash memory of this IC is often locked, encrypted, or otherwise protected to prevent reverse engineering or unauthorized access. This can pose challenges for engineers, security researchers, and developers who need to restore, crack, or decode the firmware for legitimate reasons—such as recovery, debugging, or system integration. At CIRCUIT ENGINEERING CO.,LTD, we specialize in services to attack IC C8051F530 firmware, helping clients unlock and extract secured system data with precision and confidentiality.
Understanding the Attack Process
The process to attack and clone the C8051F530 firmware involves several technical steps:
-
Device Identification & Interface Setup
We begin by analyzing the microcontroller’s packaging and communication protocols. The C8051F530 supports in-system programming via its C2 interface, which we tap into using custom hardware tools. -
Memory Mapping & Protection Bypass
Our next step is to assess memory protection settings. Many protected systems enable code read protection (CRP) to prevent firmware extraction. We apply non-invasive and semi-invasive methods to bypass these protections, depending on the system configuration. -
Dumping Flash & EEPROM
Once access is gained, we proceed to copy or duplicate the contents of Flash memory, EEPROM, and other memory blocks. The binary or heximal data is then dumped into files for further processing. -
Decryption & Decompilation
If the firmware is encrypted, we use advanced techniques to decrypt the data. The resulting binary is then reverse-engineered to decode the logic and convert it into C/C++ source code or assembly, depending on client needs. -
Analysis & Reconstruction
The final step involves reconstructing the program logic, analyzing the extracted firmware archive, and optionally cloning it to a new chip for duplication or emulation purposes.
Процесс атаки и клонирования прошивки C8051F530 включает несколько технических шагов: Идентификация устройства и настройка интерфейса Мы начинаем с анализа упаковки и протоколов связи микроконтроллера. C8051F530 поддерживает внутрисистемное программирование через свой интерфейс C2, к которому мы подключаемся с помощью специальных аппаратных инструментов. Отображение памяти и обход защиты Наш следующий шаг — оценка настроек защиты памяти. Многие защищенные системы включают защиту от чтения кода (CRP) для предотвращения извлечения прошивки. Мы применяем неинвазивные и полуинвазивные методы для обхода этих защит в зависимости от конфигурации системы. Сброс Flash и EEPROM После получения доступа мы приступаем к копированию или дублированию содержимого Flash-памяти, EEPROM и других блоков памяти. Двоичные или шестнадцатеричные данные затем сбрасываются в файлы для дальнейшей обработки.
Why Clients Choose Us
-
Proven Track Record: Years of experience in firmware cracking, binary analysis, and hardware reverse engineering.
-
Tailored Services: We support a wide range of secured devices, including locked, embedded systems across multiple industries.
-
Confidentiality & Compliance: All projects are handled securely with full client confidentiality and compliance with applicable laws.
Whether you need to hack, clone, or open the source code of a C8051F530 system, our expert team is equipped to deliver efficient and ethical solutions. Contact us today to discuss how we can help you unlock your protected firmware and recover valuable program files and data archives.
Attack IC C8051F530 protective system and remove its security fuse bit, extract firmware out from MCU C8051F530 flash memory, copy heximal to blank Microcontroller C8051F530 which will provide the same functions
Attack IC C8051F530 protective system and remove its security fuse bit, extract firmware out from MCU C8051F530 flash memory, copy heximal to blank Microcontroller C8051F530 which will provide the same functions;
Analog Peripherals
– 12-Bit ADC
· ±1 LSB INL (C8051F52x/C8051F53x); no missing codes
· Programmable throughput up to 200 ksps
· Up to 6/16 external inputs
· Data dependent windowed interrupt generator
· Built-in temperature sensor
– Comparator
· Programmable hysteresis and response time
· Configurable as wake-up or reset source
· Low current
– POR/Brownout Detector
– Voltage Reference—1.5 to 2.2 V (programmable)
On-Chip Debug
– On-chip debug circuitry facilitates full-speed, non-intrusive in-system debug (No emulator required)
– Provides breakpoints, single stepping
– Inspect/modify memory and registers
– Complete development kit
Supply Voltage 2.7 to 5.25 V
– Built-in LDO regulator
High Speed 8051 µC Core
– Pipelined instruction architecture; executes 70% of instructions in 1 or 2 system clocks
– Up to 25 MIPS throughput with 25 MHz system clock
Il processo di attacco e clonazione del firmware C8051F530 prevede diverse fasi tecniche:Iniziamo analizzando il packaging e i protocolli di comunicazione del microcontrollore. Il C8051F530 supporta la programmazione in-system tramite la sua interfaccia C2, che utilizziamo utilizzando strumenti hardware personalizzati.Il nostro passo successivo consiste nel valutare le impostazioni di protezione della memoria. Molti sistemi protetti abilitano la protezione dalla lettura del codice (CRP) per impedire l’estrazione del firmware. Applichiamo metodi non invasivi e semi-invasivi per bypassare queste protezioni, a seconda della configurazione del sistema.Una volta ottenuto l’accesso, procediamo a copiare o duplicare il contenuto della memoria Flash, della EEPROM e di altri blocchi di memoria. I dati binari o esadecimali vengono quindi scaricati in file per un’ulteriore elaborazione.
Memory
– 8/4/2 kB Flash; In-system byte programmable in 512 byte sectors
– 256 bytes internal data RAM
Digital Peripherals
– 16/6 port I/O; push-pull or open-drain, 5 V tolerant
– Hardware SPI™, and UART serial port
– Hardware LIN (both master and slave, compatible with V1.3 and V2.0)
– Three general purpose 16-bit counter/timers
– Programmable 16-bit counter/timer array with three capture/compare modules, WDT
Clock Sources
– Internal oscillators: 24.5 MHz ±0.5% accuracy supports UART and LIN-Master operation
– External oscillator: Crystal, RC, C, or Clock (1 or 2 pin modes)
– Can switch between clock sources on-the-fly
Packages:
– 10-Pin QFN (3 x 3 mm)
– 20-pin QFN (4 x 4 mm)
– 20-pin TSSOP
Temperature Range: –40 to +125 °C
 Break Chip PIC16F917 Heximal
Break Chip PIC16F917 Heximal
The PIC16F917 is a powerful 8-bit microcontroller by Microchip, commonly used in embedded systems for industrial control, consumer electronics, and automation products. Featuring integrated EEPROM, Flash memory, analog-to-digital converters, and a built-in LCD module driver, it supports a wide range of commercial and industrial applications. Its protective architecture includes code protection bits to prevent unauthorized access or duplication of the firmware or program data. However, there are cases where legitimate needs arise to break chip PIC16F917 heximal content for restoration, analysis, or system migration purposes.

Nos especializamos en el desbloqueo, decodificación y descifrado seguro y ético de firmware heximal y binario seguro, cifrado o bloqueado de microcontroladores como el PIC16F917. Nuestra experiencia radica en eludir los mecanismos de seguridad para extraer, clonar o duplicar datos esenciales, preservando la integridad del sistema. Nuestro procedimiento comprobado para descifrar el chip PIC16F917 hexadecimal Identificación y preparación del dispositivo Comenzamos identificando el modelo del chip y leyendo su configuración. En el caso del PIC16F917, se presta especial atención al manejo de los bits de protección de código y el mapa de memoria. Configuración de la interfaz de hardware Utilizando hardware especializado ICSP (Programación en serie en circuito), establecemos comunicación con el chip de destino sin interrumpir su funcionamiento en el circuito (si es necesario).
we specialize in the secure and ethical unlocking, decoding, and decryption of secured, encrypted, or locked heximal and binary firmware from microcontrollers like the PIC16F917. Our expertise lies in bypassing security mechanisms to extract, clone, or duplicate essential data while preserving system integrity.
Our Proven Procedure to Break Chip PIC16F917 Heximal
Device Identification and Preparation
We begin by identifying the chip model and reading its configuration settings. For the PIC16F917, special care is taken to handle the code protection bits and memory map.
Hardware Interface Setup
Using specialized ICSP (In-Circuit Serial Programming) hardware, we establish communication with the target chip without disturbing its operation in the circuit (if required).
Data Access Strategy
With our custom-designed tools and methods, we crack through security layers to gain access to the flash, EEPROM, and configuration bits. Depending on the protection level, this may involve advanced techniques like glitching, fault injection, or voltage manipulation.
Firmware Dump and Analysis
Once data is accessed, we perform a complete heximal firmware dump and verify integrity. This file is then converted to readable source code through a combination of disassembly and decompilation processes.

हम PIC16F917 जैसे माइक्रोकंट्रोलर से सुरक्षित, एन्क्रिप्टेड या लॉक किए गए हेक्सिमल और बाइनरी फ़र्मवेयर के सुरक्षित और नैतिक अनलॉकिंग, डिकोडिंग और डिक्रिप्शन में विशेषज्ञ हैं। हमारी विशेषज्ञता सिस्टम अखंडता को संरक्षित करते हुए आवश्यक डेटा को निकालने, क्लोन करने या डुप्लिकेट करने के लिए सुरक्षा तंत्र को बायपास करने में निहित है। चिप PIC16F917 हेक्सिमल को तोड़ने की हमारी सिद्ध प्रक्रिया डिवाइस पहचान और तैयारी हम चिप मॉडल की पहचान करके और इसकी कॉन्फ़िगरेशन सेटिंग्स को पढ़कर शुरू करते हैं। PIC16F917 के लिए, कोड सुरक्षा बिट्स और मेमोरी मैप को संभालने के लिए विशेष ध्यान रखा जाता है। हार्डवेयर इंटरफ़ेस सेटअप विशेष ICSP (इन-सर्किट सीरियल प्रोग्रामिंग) हार्डवेयर का उपयोग करके, हम सर्किट में इसके संचालन को बाधित किए बिना लक्ष्य चिप के साथ संचार स्थापित करते हैं (यदि आवश्यक हो)। डेटा एक्सेस रणनीति हमारे कस्टम-डिज़ाइन किए गए टूल और विधियों के साथ, हम फ़्लैश, EEPROM और कॉन्फ़िगरेशन बिट्स तक पहुँच प्राप्त करने के लिए सुरक्षा परतों को तोड़ते हैं। सुरक्षा स्तर के आधार पर, इसमें गड़बड़, दोष इंजेक्शन या वोल्टेज हेरफेर जैसी उन्नत तकनीकें शामिल हो सकती हैं। फ़र्मवेयर डंप और विश्लेषण एक बार डेटा एक्सेस हो जाने के बाद, हम एक पूर्ण हेक्सिमल फ़र्मवेयर डंप करते हैं और अखंडता को सत्यापित करते हैं। इस फ़ाइल को फिर डिसएसेम्बली और डीकंपाइलेशन प्रक्रियाओं के संयोजन के माध्यम से पठनीय स्रोत कोड में परिवर्तित किया जाता है।
Restoration or Duplication
The final stage involves either restoring the firmware to another device, cloning it for migration, or delivering the decoded, decrypted archive in readable format (such as C/C++ or Assembly) for further development or auditing.
Applications and Use Cases
The PIC16F917 is widely used in products like smart meters, home appliances, automotive control panels, and programmable LCD interfaces. In many cases, original firmware files may be lost or no longer supported by the manufacturer. Our service helps clients recover, unlock, and reuse these embedded systems efficiently.
Whether you need to copy, clone, or open a protected firmware, or decode a legacy program file, we provide safe, confidential solutions tailored to your technical and legal needs.

Break Chip PIC16F917 tamper resistance system and readout MCU PIC16F917 heximal from flash memory and eeprom memory, the program and data will be exactly the same as master original PIC16F917 microprocessor
Break Chip PIC16F917 tamper resistance system and readout MCU PIC16F917 heximal from flash memory and eeprom memory, the program and data will be exactly the same as master original PIC16F917 microprocessor;
High-Performance RISC CPU:
· Only 35 instructions to learn:
– All single-cycle instructions except branches
· Operating speed:
– DC – 20 MHz oscillator/clock input
– DC – 200 ns instruction cycle
· Program Memory Read (PMR) capability
· Interrupt capability
· 8-level deep hardware stack
· Direct, Indirect and Relative Addressing modes
Special Microcontroller Features:
· Precision Internal Oscillator:
– Factory calibrated to ±1%
– Software selectable frequency range of 8 MHz to 32 kHz
– Software tunable
– Two-Speed Start-up mode
– Crystal fail detect for critical applications
– Clock mode switching during operation for power savings
· Power-saving Sleep mode
· Wide operating voltage range (2.0V-5.5V)
· Industrial and Extended temperature range
· Power-on Reset (POR)
· Power-up Timer (PWRT) and Oscillator Start-up Timer (OST)
· Brown-out Reset (BOR) with software control option
· Enhanced Low-Current Watchdog Timer (WDT) with on-chip oscillator (software selectable nominal 268 seconds with full prescaler) with software enable
· Multiplexed Master Clear with pull-up/input pin
· Programmable code protection
· High-Endurance Flash/EEPROM cell:
– 100,000 write Flash endurance
– 1,000,000 write EEPROM endurance
– Flash/Data EEPROM retention: > 40 years

PIC16F917 gibi mikrodenetleyicilerden güvenli, şifrelenmiş veya kilitli heximal ve ikili ürün yazılımlarının güvenli ve etik bir şekilde kilidini açma, kod çözme ve şifresini çözme konusunda uzmanlaştık. Uzmanlığımız, sistem bütünlüğünü korurken temel verileri çıkarmak, klonlamak veya kopyalamak için güvenlik mekanizmalarını atlatmaktır. Çip PIC16F917 Heximal’i Kırmak İçin Kanıtlanmış Prosedürümüz Aygıt Tanımlama ve Hazırlama Çip modelini tanımlayarak ve yapılandırma ayarlarını okuyarak başlıyoruz. PIC16F917 için, kod koruma bitlerini ve bellek haritasını işlemek için özel özen gösterilir. Donanım Arayüzü Kurulumu Özel ICSP (Devre İçi Seri Programlama) donanımı kullanarak, devredeki çalışmasını bozmadan (gerekirse) hedef çip ile iletişim kurarız.
Low-Power Features:
· Standby Current:
– <100 nA @ 2.0V, typical
· Operating Current:
– 8.5 ìA @ 32 kHz, 2.0V, typical
– 100 ìA @ 1 MHz, 2.0V, typical
· Watchdog Timer Current:
– 1 ìA @ 2.0V, typical
Peripheral Features:
· Liquid Crystal Display module:
– Up to 60 pixel drive capability on 28-pin devices
– Up to 96 pixel drive capability on 40-pin devices
– Four commons
· Up to 35 I/O pins and 1 input-only pin:
– High-current source/sink for direct LED drive
– Interrupt-on-pin change
– Individually programmable weak pull-ups
· In-Circuit Serial Programming™ (ICSP™) via two pins
· Analog comparator module with:
– Two analog comparators
– Programmable on-chip voltage reference (CVREF) module (% of VDD)
– Comparator inputs and outputs externally accessible
· A/D Converter:
– 10-bit resolution and up to 8 channels
· Timer0: 8-bit timer/counter with 8-bit programmable prescaler
· Enhanced Timer1:
– 16-bit timer/counter with prescaler
– External Gate Input mode
– Option to use OSC1 and OSC2 as Timer1 oscillator if INTOSCIO or LP mode is selected
· Timer2: 8-bit timer/counter with 8-bit period register, prescaler and postscaler
· Addressable Universal Synchronous
Asynchronous Receiver Transmitter (AUSART)
· Up to 2 Capture, Compare, PWM modules:
– 16-bit Capture, max. resolution 12.5 ns
– 16-bit Compare, max. resolution 200 ns
– 10-bit PWM, max. frequency 20 kHz
· Synchronous Serial Port (SSP) with I2C™
 Copy Chip PIC16F870 Program
Copy Chip PIC16F870 Program
The Microchip PIC16F870 microcontroller is widely used in industrial, commercial, and consumer products due to its reliability, compact size, and rich feature set. Equipped with flash memory, EEPROM, and a range of peripheral interfaces, the PIC16F870 is a popular choice for applications such as automation systems, smart appliances, motor control, and remote sensors.

No entanto, quando o firmware armazenado em sua flash ou EEPROM está protegido, bloqueado ou criptografado, acessar, modificar ou restaurar o programa original torna-se uma tarefa complexa. É aí que a Circuit Engineering CO.,LTD entra em cena. Somos especializados em serviços que copiam, clonam, duplicam, desbloqueiam, crackeiam, hackeiam, decodificam, descriptografam, restauram e abrem o conteúdo de microcontroladores protegidos como o PIC16F870.
However, when the firmware stored inside its flash or EEPROM is protected, locked, or encrypted, accessing, modifying, or restoring the original program becomes a complex task. That’s where Circuit Engineering CO.,LTD steps in. We specialize in services that copy, clone, duplicate, unlock, crack, hack, decode, decrypt, restore, and open the contents of secured microcontrollers like the PIC16F870.
Unique Features of the PIC16F870
The PIC16F870 features 2K words of Flash program memory, 128 bytes of EEPROM, and a full complement of peripherals including A/D converters, USART communication, and a versatile I/O configuration. Its popularity in critical embedded systems makes it essential to have the ability to recover or duplicate the internal binary, heximal, or source code when original files are lost or when reverse engineering is required.

Ancak, flash veya EEPROM’unda depolanan aygıt yazılımı korunduğunda, kilitlendiğinde veya şifrelendiğinde, orijinal programa erişmek, onu değiştirmek veya geri yüklemek karmaşık bir görev haline gelir. Circuit Engineering CO.,LTD tam da burada devreye girer. PIC16F870 gibi güvenli mikrodenetleyicilerin içeriklerini kopyalayan, klonlayan, çoğaltan, kilidini açan, kıran, hackleyen, kodunu çözen, şifresini çözen, geri yükleyen ve açan hizmetlerde uzmanlaşıyoruz.
Our Procedure to Copy Chip PIC16F870 Program
-
Chip Analysis
First, we assess the specific security level applied to the PIC16F870. We determine if the flash, eeprom, or both have protective measures like read protection or encryption. -
Unlocking the Protection
Using advanced hardware and software tools, we safely crack, hack, or decrypt the microcontroller’s security layers without damaging the memory. -
Data Extraction
Once unlocked, we proceed to copy the entire program memory, eeprom data, and any configuration bits. This firmware is extracted as a complete binary or heximal file. -
Decoding and Verification
The extracted archive is decoded and carefully verified against the microcontroller’s operation to ensure data integrity. -
Restoration or Duplication
Depending on the client’s needs, we can restore the original program onto a blank PIC16F870, clone multiple units, or convert the extracted firmware into human-readable source code for further modification.

Jednak gdy oprogramowanie układowe przechowywane w pamięci flash lub EEPROM jest chronione, zablokowane lub zaszyfrowane, dostęp, modyfikacja lub przywrócenie oryginalnego programu staje się złożonym zadaniem. W tym miejscu wkracza Circuit Engineering CO.,LTD. Specjalizujemy się w usługach kopiowania, klonowania, duplikowania, odblokowywania, łamania, hakowania, dekodowania, odszyfrowywania, przywracania i otwierania zawartości zabezpieczonych mikrokontrolerów, takich jak PIC16F870.
Copy Chip PIC16F870 Program and data out from microcontroller PIC16F870 flash memory and eeprom memory, reset the status of MCU PIC16F870 from locked to unlocked one after disable its security fuse bit by MCU crack technique
Copy Chip PIC16F870 Program and data out from microcontroller PIC16F870 flash memory and eeprom memory, reset the status of MCU PIC16F870 from locked to unlocked one after disable its security fuse bit by MCU crack technique;
Microcontroller Core Features:
· High performance RISC CPU
· Only 35 single word instructions to learn
· All single cycle instructions except for program branches which are two-cycle
· Operating speed: DC – 20 MHz clock input DC – 200 ns instruction cycle
· 2K x 14 words of FLASH Program Memory
128 x 8 bytes of Data Memory (RAM) 64 x 8 bytes of EEPROM Data Memory
· Pinout compatible to the PIC16CXXX 28 and 40-pin devices
· Interrupt capability (up to 11 sources)
· Eight level deep hardware stack
· Direct, Indirect and Relative Addressing modes;
· Power-on Reset (POR)
· Power-up Timer (PWRT) and
Oscillator Start-up Timer (OST)
· Watchdog Timer (WDT) with its own on-chip RC oscillator for reliable operation when MCU STM32F107RCT6 code recovery
· Programmable code protection
· Power saving SLEEP mode
· Selectable oscillator options
· Low power, high speed CMOS FLASH/EEPROM technology
· Fully static design
· In-Circuit Serial Programmingä (ICSPä) via two pins
· Single 5V In-Circuit Serial Programming capability
· In-Circuit Debugging via two pins
· Processor read/write access to program memory
· Wide operating voltage range: 2.0V to 5.5V
· High Sink/Source Current: 25 mA
· Commercial and Industrial temperature ranges
· Low power consumption:
– < 1.6 mA typical @ 5V, 4 MHz
– 20 mA typical @ 3V, 32 kHz
– < 1 mA typical standby current
Peripheral Features:
· Timer0: 8-bit timer/counter with 8-bit prescaler
· Timer1: 16-bit timer/counter with prescaler, can be incremented during SLEEP via external crystal/clock
· Timer2: 8-bit timer/counter with 8-bit period register, prescaler and postscaler
· One Capture, Compare, PWM module
– Capture is 16-bit, max. resolution is 12.5 ns
– Compare is 16-bit, max. resolution is 200 ns
– PWM max. resolution is 10-bit
· 10-bit multi-channel Analog-to-Digital converter only
· Universal Synchronous Asynchronous Receiver
Transmitter (USART/SCI) with 9-bit address detection
· Parallel Slave Port (PSP) 8-bits wide, with external RD, WR and CS controls (40/44-pin only)
· Brown-out detection circuitry for Brown-out Reset (BOR)
 Copy IC PIC16F84A Binary
Copy IC PIC16F84A Binary
The PIC16F84A microcontroller, developed by Microchip Technology, is one of the most popular and widely used chips in embedded applications, known for its flash memory, EEPROM storage, and ease of programming. However, many PIC16F84A chips are delivered with protected firmware, making it difficult to access or modify the internal binary. At Circuit Engineering Co., LTD, we specialize in Copy IC PIC16F84A Binary services, helping clients readout, decrypt, and restore locked microcontrollers by using advanced techniques tailored to this specific IC.
माइक्रोचिप टेक्नोलॉजी द्वारा विकसित PIC16F84A माइक्रोकंट्रोलर, एम्बेडेड अनुप्रयोगों में सबसे लोकप्रिय और व्यापक रूप से उपयोग किए जाने वाले चिप्स में से एक है, जो अपनी फ्लैश मेमोरी, EEPROM स्टोरेज और प्रोग्रामिंग में आसानी के लिए जाना जाता है। हालाँकि, कई PIC16F84A चिप्स को सुरक्षित फ़र्मवेयर के साथ डिलीवर किया जाता है, जिससे आंतरिक बाइनरी तक पहुँचना या उसे संशोधित करना मुश्किल हो जाता है। सर्किट इंजीनियरिंग कंपनी, लिमिटेड में, हम कॉपी आईसी PIC16F84A बाइनरी सेवाओं में विशेषज्ञ हैं, जो ग्राहकों को इस विशिष्ट आईसी के अनुरूप उन्नत तकनीकों का उपयोग करके लॉक किए गए माइक्रोकंट्रोलर को रीडआउट, डिक्रिप्ट और पुनर्स्थापित करने में मदद करते हैं।
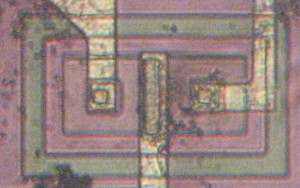
Unlike older OTP (One-Time Programmable) chips like the PIC16C554, the PIC16F84A features flash-based memory, which allows the program to be rewritten multiple times. This flash memory, however, is often encrypted, secured, or protected by code-protection bits to prevent easy access. Standard reverse engineering methods used for other microcontrollers are often ineffective. That’s why specialized approaches like decapsulation (physical chip opening), memory charge analysis, or optical imaging are necessary to break and decode the firmware stored inside.

PIC16C554와 같은 구형 OTP(One-Time Programmable) 칩과 달리 PIC16F84A는 플래시 기반 메모리를 사용하여 프로그램을 여러 번 다시 작성할 수 있습니다. 하지만 이 플래시 메모리는 쉽게 접근할 수 없도록 암호화, 보안 또는 코드 보호 비트로 보호되는 경우가 많습니다. 다른 마이크로컨트롤러에 사용되는 표준 리버스 엔지니어링 방법은 종종 효과가 없습니다. 따라서 내부에 저장된 펌웨어를 해독하고 디코딩하기 위해 디캡슐레이션(물리적 칩 개방), 메모리 전하 분석, 광학 이미징과 같은 특수한 접근 방식이 필요합니다.
Our proven process to copy IC PIC16F84A binary includes several stages:
-
Chip Readout & Flash Memory Access – We employ precise tools to open, readout, and decrypt the locked flash and EEPROM data, even if protective fuses are set.
-
Binary Extraction and Program Restoration – After extraction, we restore the original binary or heximal file, ensuring data integrity for duplication.
-
Firmware Analysis and Source Code Recovery – Once the program file is retrieved, our team can decode and replicate it into readable source code, allowing further modifications or migrations.
-
Firmware Duplication and Replication – Finally, the binary archive can be cloned or duplicated onto a new PIC16F84A or compatible microcontroller, helping clients expand their embedded systems without dependency on the original locked units.
The PIC16F84A stands apart due to its reprogrammable flash design, making it highly versatile but also more challenging to hack or replicate when security is enabled. Unlike other microcontrollers with simple security models, breaking into a secured PIC16F84A memory often requires non-invasive and invasive techniques combined.

Duplication et réplication du micrologiciel : enfin, l’archive binaire peut être clonée ou dupliquée sur un nouveau PIC16F84A ou un microcontrôleur compatible, permettant ainsi aux clients d’étendre leurs systèmes embarqués sans dépendre des unités verrouillées d’origine. Le PIC16F84A se distingue par sa conception Flash reprogrammable, ce qui le rend très polyvalent, mais aussi plus difficile à pirater ou à dupliquer lorsque la sécurité est activée. Contrairement à d’autres microcontrôleurs dotés de modèles de sécurité simples, l’intrusion dans une mémoire PIC16F84A sécurisée nécessite souvent une combinaison de techniques non invasives et invasives.
If you need to copy, clone, or replicate your protected firmware stored in a PIC16F84A, or if you have lost access to your original program files, Circuit Engineering Co., LTD offers a reliable and secure path to unlock and restore your critical embedded data. Contact us today to learn more about how we can help you decapsulate, decode, and open your secured microcontroller archives.
Copy IC PIC16F84A Binary out from microcontroller PIC16F84A flash memory, and reprogramme the firmware into blank MCU PIC16F84A which will provide the same functions as original version
Copy IC PIC16F84A Binary out from microcontroller PIC16F84A flash memory, and reprogramme the firmware into blank MCU PIC16F84A which will provide the same functions as original version, the status of master original MICROPROCESSOR PIC16F84A can be unlocked;
The PIC16F8X is a group in the PIC16CXX family of low-cost, high-performance, CMOS, fully-static, 8-bit microcontrollers. This group contains the following devices:
· PIC16F83
· PIC16F84
Table 1-1 lists the features of the PIC16F8X. A simplified block diagram of the PIC16F8X is shown in Figure 3-1.
The PIC16F8X fits perfectly in applications ranging from high speed automotive and appliance motor control to low-power remote sensors, electronic locks, security devices and smart cards. The Flash/EEPROM technology makes customization of application after Copy microcontroller programs (transmitter codes, motor speeds, receiver frequencies, security codes, etc.) extremely fast and All PICmicro™ microcontrollers employ an advanced RISC architecture. PIC16F8X devices have enhanced core features, eight-level deep stack, and multiple internal and external interrupt sources.
The separate instruction and data buses of the Harvard architecture allow a 14-bit wide instruction word with a separate 8-bit wide data bus. The two stage instruction pipeline allows all instructions to execute in a single cycle, except for program branches (which require two cycles). A total of 35 instructions (reduced instruction set) are available. Additionally, a large register set is used to achieve a very high performance level.
PIC16F8X microcontrollers typically achieve a 2:1 code compression and up to a 4:1 speed improvement (at 20 MHz) over other 8-bit microcontrollers in their class. The small footprint packages make this microcontroller series perfect for all applications with space limitations. Low-cost, low-power, high performance, ease-of-use and I/O flexibility of making the PIC16F8X very versatile even in areas where no microcontroller use has been considered (e.g., timer functions; serial communication; capture, compare and PWM functions; and co-processor applications).
The serial in-system programming feature (via two pins) offers flexibility of customizing the product after complete assembly and testing. This feature can be used to serialize a product, store calibration data, or program the device with the current firmware before shipping after IC program can be restored.
The PIC16F8X has up to 68 bytes of RAM, 64 bytes of Data EEPROM memory, and 13 I/O pins. A timer/ Family and Upward Compatibility counter is also available.
The PIC16CXX family has special features to reduce external components, thus reducing cost, enhancing system reliability and reducing power consumption.
There are four oscillator options, of which the single pin RC oscillator provides a low-cost solution, the LP Those users familiar with the PIC16C5X family of microcontrollers will realize that this is an enhanced version of the PIC16C5X architecture. Please refer to Appendix A for a detailed list of enhancements. Code written for PIC16C5X devices can be easily ported to PIC16F8X devices (Appendix B). oscillator minimizes power consumption, XT is a standard crystal, and the HS is for High Speed crystals.
Development Support
The SLEEP (power-down) mode offers power saving.
The user can wake the chip from sleep through several external and internal interrupts and resets.
A highly reliable Watchdog Timer with its own on-chip RC oscillator provides protection against software lock-up.
The devices with Flash program memory allow the same device package to be used for prototyping and production. In-circuit reprogrammability allows the code to be updated without the device being removed from the end application.
This is useful in the development of many applications where the device may not be easily accessible, but the prototypes may require code updates. This is also useful for remote applications where the code may need to be updated (such as rate information)
The PIC16CXX family is supported by a full-featured macro assembler, a software simulator, an in-circuit emulator, a low-cost development programmer and a full-featured programmer. A “C” compiler and fuzzy logic support tools are also available.