Recover Chip EPM7064AETC100-4N Software
Recover Chip EPM7064AETC100-4N Software
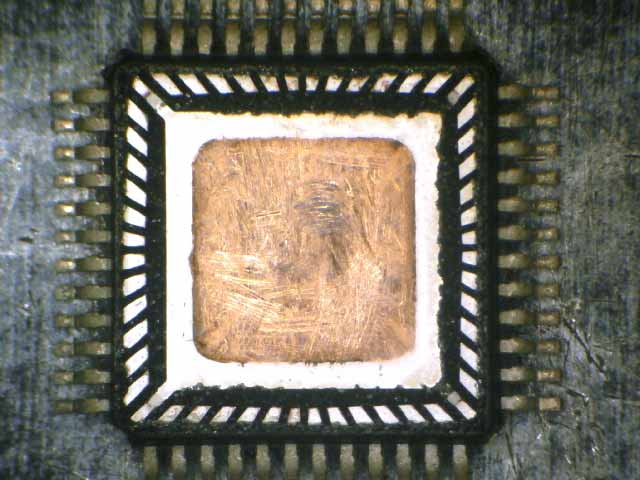
Recover Chip EPM7064AETC100-4N Software is a professional service designed to retrieve critical design data from Altera MAX 7000 series CPLDs used in a wide range of embedded and industrial systems. The EPM7064AETC100-4N is commonly found in industrial control panels, communication equipment, automotive electronics, test instruments, and legacy automation platforms. Its compact logic architecture, fast response, and stable embedded performance make it ideal for glue logic, protocol handling, and custom control logic where firmware, binary, and archived program files are central to system operation.
We can recover Chip EPM7064AETC100-4N software, please view below Chip EPM7064AETC100-4N features for your reference:
High-performance 3.3-V EEPROM-based programmable logic devices (PLDs) built on second-generation Multiple Array MatriX
3.3-V in-system programmability (ISP) through the built-in IEEE Std. 1149.1 Joint Test Action Group (JTAG) interface with advanced pin-locking capability
In many real-world cases, the original source code or configuration files are lost due to staff changes, discontinued suppliers, or aging storage media. Our service focuses on retrieving protected and locked design data from secured devices so that clients can restore functionality or duplicate existing hardware. Whether the goal is to recover a binary or heximal file, reconstruct embedded logic behavior, or extract archived program data for maintenance, we apply structured methods to decode and retrieve usable information while respecting device constraints. This enables safe cloning or controlled duplication without redesigning the entire system.
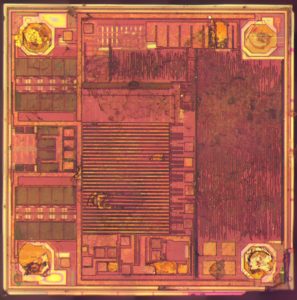
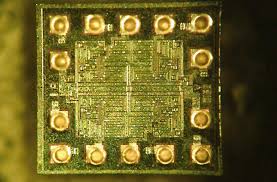
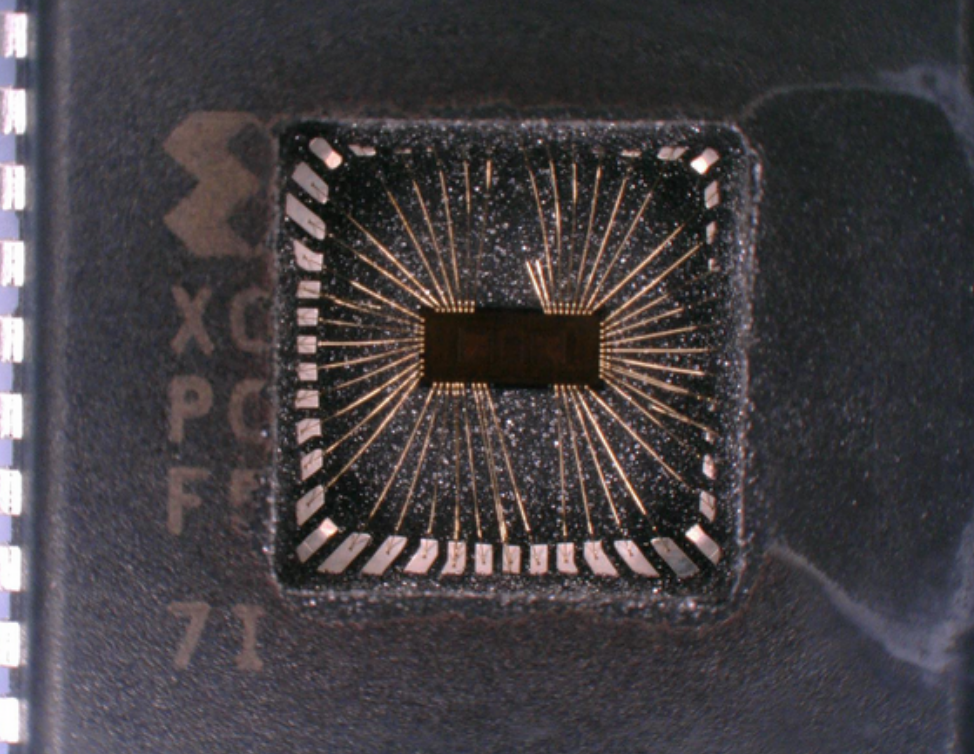
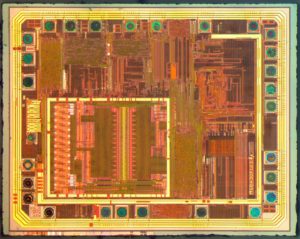
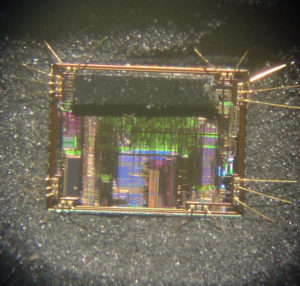
From a technical standpoint, EPM7064AETC100-4N recovery can be challenging because CPLDs rely on internal non-volatile memory structures rather than conventional flash or EEPROM layouts. Devices are often encrypted or secured with protection bits, making standard readout impossible. Depending on the condition and protection level, engineers may need to attack protection mechanisms, break access controls, or decapsulate the package for deeper analysis. These steps require experience to avoid data corruption and to ensure the recovered firmware or memory image accurately reflects the original embedded logic and timing behavior.
– MAX 7000AE device in-system programmability (ISP) circuitry compliant with IEEE Std. 1532
– EPM7128A and EPM7256A device ISP circuitry compatible with IEEE Std. 1532
Built-in boundary-scan test (BST) circuitry compliant with IEEE Std. 1149.1
Supports JEDEC Jam Standard Test and Programming Language (STAPL) JESD-71
Enhanced ISP features
– Enhanced ISP algorithm for faster programming (excluding EPM7128A and EPM7256A devices)
– ISP_Done bit to ensure complete programming (excluding EPM7128A and EPM7256A devices)
– Pull-up resistor on I/O pins during in-system
– Pin-compatible with the popular
4.5-ns pin-to-pin logic delays with counter frequencies of up to 227.3 MHz
MultiVoltTM I/O interface enables device core to run at 3.3 V, while I/O pins are compatible with 5.0-V, 3.3-V, and 2.5-V logic levels Pin counts ranging from 44 to 256 in a variety of thin quad flat pack (TQFP), plastic quad flat pack (PQFP), ball-grid array (BGA), space-saving FineLine BGATM, and plastic J-lead chip carrier (PLCC) packages.

The purpose of recovering EPM7064AETC100-4N software is to deliver tangible value to end users. By retrieving critical data and program files, manufacturers can extend product life cycles, support installed equipment, migrate designs to newer platforms, or audit legacy logic for compliance and safety. Our service reduces downtime, minimizes redevelopment costs, and preserves intellectual investment locked inside protected chips. Even in complex scenarios involving encrypted or secured devices, our structured recovery workflow helps clients regain control of their embedded systems with confidence and long-term reliability.
Supports hot-socketing in MAX 7000AE devices
Programmable interconnect array (PIA) continuous routing structure for fast, predictable performance
PCI-compatible
Bus-friendly architecture, including programmable slew-rate control
Open-drain output option
Programmable macrocell registers with individual clear, preset, clock, and clock enable controls
Programmable power-up states for macrocell registers in MAX 7000AE devices
Programmable power-saving mode for 50% or greater power reduction in each macrocell
Configurable expander product-term distribution, allowing up to 32 product terms per macrocell
Programmable security bit for protection of proprietary designs 6 to 10 pin- or logic-driven output enable signals

Two global clock signals with optional inversion
Enhanced interconnect resources for improved routability
Fast input setup times provided by a dedicated path from I/O pin to macrocell registers
Programmable output slew-rate control
Programmable ground pins
Software design support and automatic place-and-route provided by Altera’s development systems for Windows-based PCs and Sun SPARCstation, and HP 9000 Series 700/800 workstations Additional design entry and simulation support provided by EDIF 2 0 0 and 3 0 0 netlist files, library of parameterized modules (LPM), Verilog HDL, VHDL, and other interfaces to popular EDA tools from manufacturers such as Cadence, Exemplar Logic, Mentor Graphics, OrCAD, Synopsys, Synplicity, and VeriBest
Programming support with Altera’s Master Programming Unit (MPU), MasterBlasterTM serial/universal serial bus (USB) communications cable, ByteBlasterMVTM parallel port download cable, and BitBlasterTM serial download cable, as well as programming hardware from third-party manufacturers and any JamTM STAPL File (.jam), Jam Byte-Code File (.jbc), or Serial Vector Format File- (.svf) capable in-circuit tester.
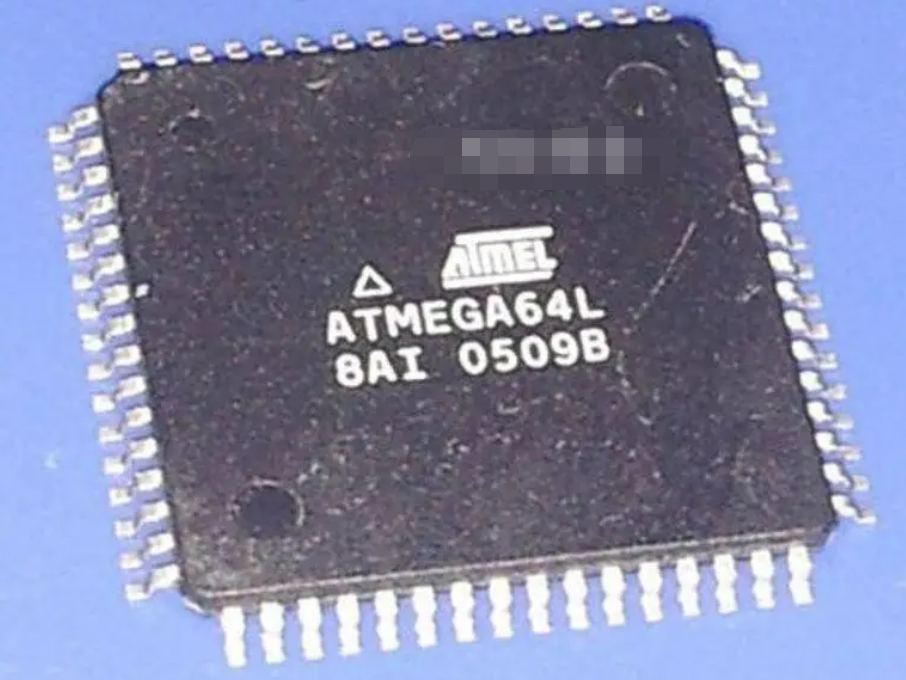
 Recover IC ATmega64L Binary
Recover IC ATmega64L Binary
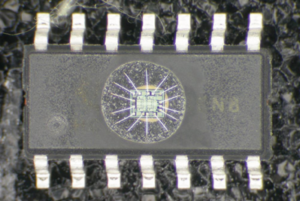
Recover IC ATmega64L Binary is a specialized engineering service focused on retrieving critical firmware and binary assets from embedded systems built around the ATmega64L microcontroller. This chip is widely used in industrial automation, smart meters, medical devices, access control, and legacy consumer electronics due to its low-power design, robust flash and EEPROM architecture, and stable embedded performance. When original source code or program files are lost, damaged, or unavailable, recovery of binary, heximal, and archived data becomes essential for product continuity, compliance, and long-term maintenance of protected systems.
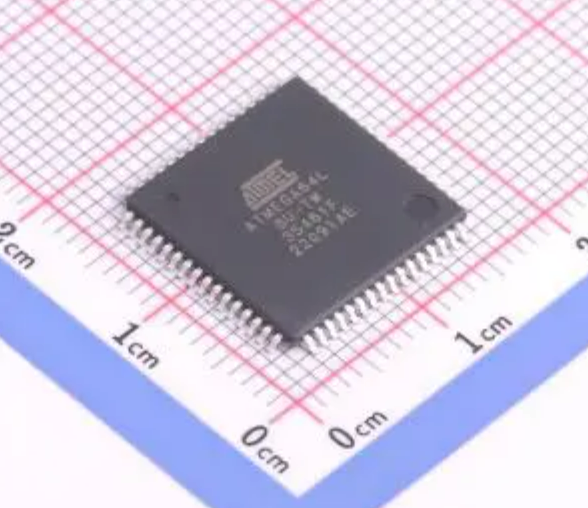
We can Recover IC ATMEGA64L Binary, please view below IC ATMEGA64L features for your reference:
· High-performance, Low-power Atmel® AVR® 8-bit Microcontroller
· Advanced RISC Architecture
– 130 Powerful Instructions – Most Single Clock Cycle Execution
– 32 x 8 General Purpose Working Registers + Peripheral Control Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
Our service addresses scenarios where the ATmega64L is protected, locked, encrypted, or otherwise secured against standard readout. Through controlled attack and decode strategies, we are able to retrieve firmware, memory content, and embedded data while preserving device integrity. The objective is not merely to copy or duplicate files, but to recover usable flash, EEPROM, and program archives that enable repair, refurbishment, migration, or controlled cloning of existing hardware. This approach is especially valuable for end users managing discontinued products or mission-critical equipment with no vendor support.

High Endurance Non-volatile Memory segments
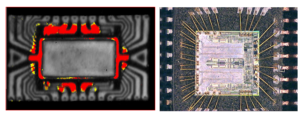
From a technical perspective, recovering IC ATmega64L binary data involves multiple layers of analysis. Depending on protection settings, engineers may need to break access controls, decapsulate the chip package, or apply non-invasive and semi-invasive techniques to retrieve secured memory regions. Challenges often include encrypted firmware blocks, corrupted flash sectors, or undocumented configuration fuses. Each step requires precise handling to avoid data loss, ensuring the recovered binary, heximal output, or source code equivalent remains accurate and verifiable for downstream use.
– 64 Kbytes of In-System Reprogrammable Flash program memory
– 2 Kbytes EEPROM
– 4 Kbytes Internal SRAM
– Write/Erase Cycles: 10,000 Flash/100,000 EEPROM
– Data retention: 20 years at 85°C/100 years at 25°C(1)
– Optional Boot Code Section with Independent Lock Bits
In-System Programming by On-chip Boot Program
True Read-While-Write Operation
– Up to 64 Kbytes Optional External Memory Space
The benefits of our ATmega64L recovery service are tangible and measurable. Clients gain the ability to restore production, duplicate legacy controllers, audit embedded firmware, or migrate designs to new platforms without redesign from scratch. By retrieving protected memory and archived program files, organizations reduce downtime, protect intellectual investment, and regain control over embedded systems. Our structured, compliant workflow ensures that even highly secured and embedded microcontroller projects can be recovered efficiently, reliably, and with long-term value for engineering and operations teams.
– Programming Lock for Software Security
– SPI Interface for In-System Programming
JTAG (IEEE std. 1149.1 Compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– Two Expanded 16-bit Timer/Counters with Separate Prescaler, Compare Mode, and Capture Mode
– Real Time Counter with Separate Oscillator
– Two 8-bit PWM Channels
– 6 PWM Channels with Programmable Resolution from 1 to 16 Bits
– 8-channel, 10-bit ADC
8 Single-ended Channels
7 Differential Channels
2 Differential Channels with Programmable Gain (1x, 10x, 200x)
– Byte-oriented Two-wire Serial Interface
– Dual Programmable Serial USARTs
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Six Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, Standby
and Extended Standby
– Software Selectable Clock Frequency
– ATmega103 Compatibility Mode Selected by a Fuse
– Global Pull-up Disable
I/O and Packages
– 53 Programmable I/O Lines
– 64-lead TQFP and 64-pad QFN/MLF
Operating Voltages
– 2.7V – 5.5V for ATmega64L
– 4.5V – 5.5V for ATmega64
Speed Grades
– 0 – 8 MHz for ATmega64L
– 0 – 16 MHz for ATmega64

 Break IC ATmega169P Code
Break IC ATmega169P Code
The calibrated internal RC Oscillator provides a fixed 8.0 MHz clock. The frequency is nominal value at 3V and 25°C. If 8 MHz frequency exceeds the specification of the device (depends on VCC), the CKDIV8 Fuse must be programmed in order to divide the internal frequency by 8 during start-up to facilitate Break IC ATmega169P Code.
The device is shipped with the CKDIV8 Fuse programmed. See “System Clock Prescaler” on page 29. for more details. This clock may be selected as the system clock by programming the CKSEL Fuses as shown in Table 8. If selected, it will operate with no external components. During reset, hardware loads the calibration byte into the OSCCAL Register and thereby automatically calibrates the RC Oscillator.
At 3V and 25°C, this calibration gives a frequency within ± 10% of the nominal frequency. Using calibration methods as described in application notes available at www.atmel.com/avr it is possible to achieve ± 2% accuracy at any given VCC and Temperature. When this Oscillator is used as the IC clock, the Watchdog Oscillator will still be used for the Watchdog Timer and for the Reset Time-out.
For more information on the pre-programmed calibration value, see the section “Calibration Byte” on page 269. When this Oscillator is selected, start-up times are determined by the SUT Fuses as shown in Table 9. Selecting internal RC Oscillator allows the XTAL1/TOSC1 and XTAL2/TOSC2 pins to be used as timer oscillator pins.
Writing the calibration byte to this address will trim the internal Oscillator to remove process variations from the Oscillator frequency. This is done automatically during IC Reset. When OSCCAL is zero, the lowest available frequency is chosen in the process of Break IC ATmega169P Code. Writing nonzero values to this register will increase the frequency of the internal Oscillator.
Writing 0x7F to the register gives the highest available frequency. The calibrated Oscillator is used to time EEPROM and Flash access. If EEPROM or Flash is written, do not calibrate to more than 10% above the nominal frequency. Otherwise, the EEPROM or Flash write may fail. Note that the Oscillator is intended for calibration to 8.0 MHz. Tuning to other values is not guaranteed, as indicated in Table 10.
When applying an external clock, it is required to avoid sudden changes in the applied clock frequency to ensure stable operation of the MCU. A variation in frequency of more than 2% from one clock cycle to the next can lead to unpredictable behavior. It is required to ensure that the MCU is kept in Reset during such changes in the clock frequency.
Note that the System Clock Prescaler can be used to implement run-time changes of the internal clock frequency while still ensuring stable operation. Refer to “System Clock Prescaler” on page 29 for details. When the CKOUT Fuse is programmed, the system Clock will be output on CLKO. This mode is suitable when IC clock is used to drive other circuits on the system.
The clock will be output also during reset and the normal operation of I/O pin will be overridden when the fuse is programmed. Any clock source, including internal RC Oscillator, can be selected when CLKO serves as clock output. If the System Clock Prescaler is used, it is the divided system clock that is output when the CKOUT Fuse is programmed.
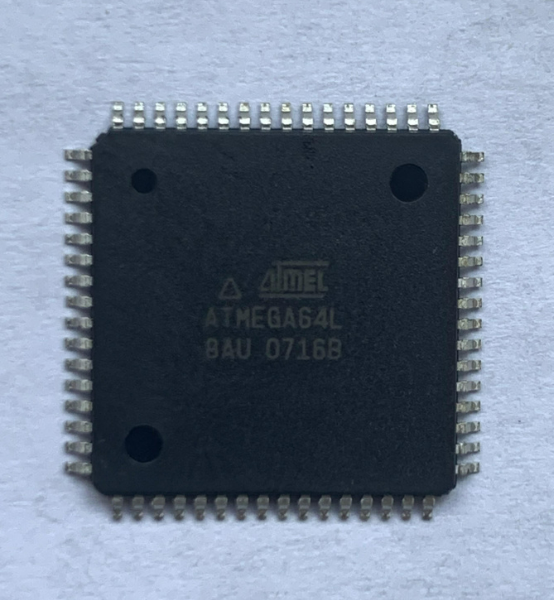
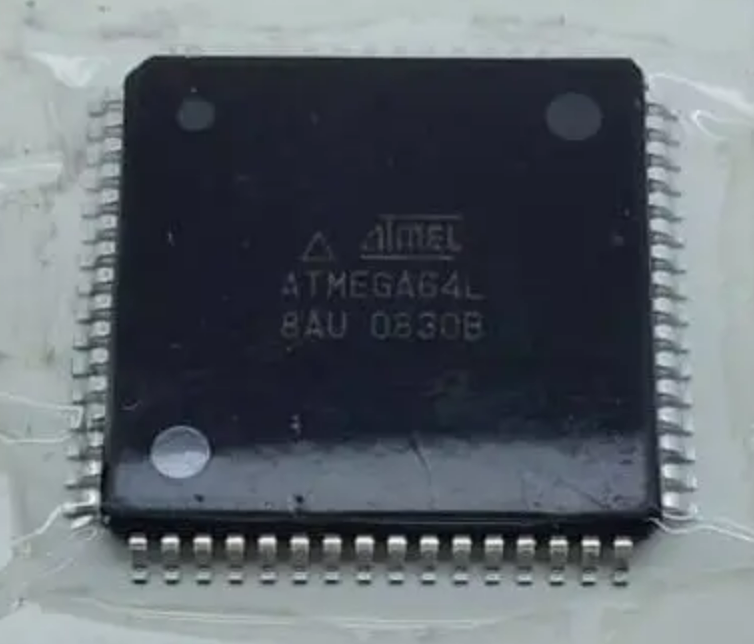
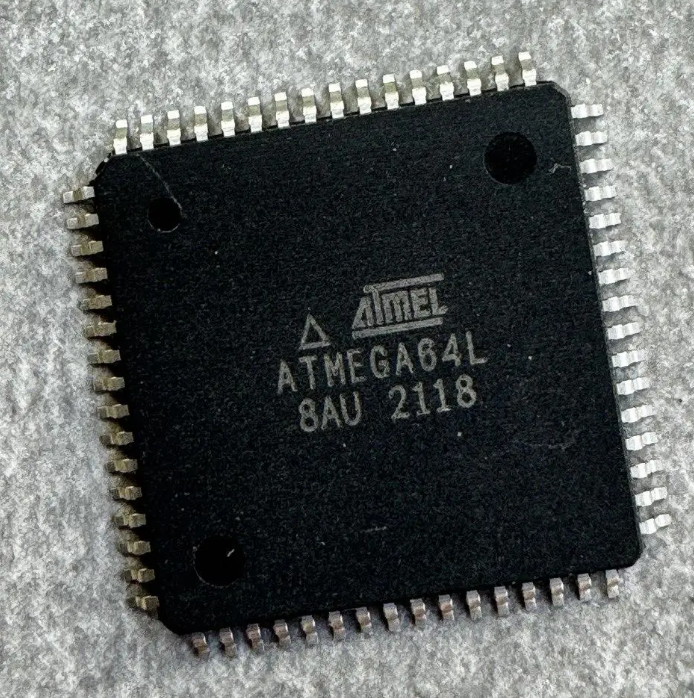
 Copy Chip ATmega64L Eeprom
Copy Chip ATmega64L Eeprom
Copy Chip ATmega64L EEPROM is a specialized professional service designed for legitimate owners who need to recover, preserve, or migrate critical embedded data from legacy or active AVR-based systems. The ATmega64L is a widely adopted 8-bit microcontroller from Atmel (Microchip) known for its low-power operation, rich peripheral set, and stable architecture, making it a long-term choice in industrial control, consumer electronics, automotive modules, medical instruments, smart meters, security devices, and various customized embedded products. In many of these applications, essential configuration data, calibration parameters, device identifiers, and control logic are stored inside EEPROM, flash memory, or protected program areas, often in a locked, encrypted, or otherwise secured state.

We can Copy Chip ATmega64L Eeprom, please view below chip features for your reference:
· High-performance, Low-power Atmel® CHIP® 8-bit Microcontroller
· Advanced RISC Architecture
– 130 Powerful Instructions – Most Single Clock Cycle Execution
– 32 x 8 General Purpose Working Registers + Peripheral Control Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
When original firmware documentation, source code, or archived files are lost, businesses may face production stoppages, maintenance risks, or costly redesigns. Our Copy Chip ATmega64L EEPROM service helps customers legally attack these barriers at a high level, enabling them to retrieve, decode, clone, or duplicate their own embedded firmware, binary, or heximal data without revealing sensitive technical methods. The ATmega64L’s unique features—such as multiple communication interfaces, flexible memory mapping, and reliable EEPROM endurance—also introduce challenges when protection bits are enabled, as standard programmers cannot access locked memory regions. In such cases, advanced analysis may be required to break through protective mechanisms and retrieve the embedded data archive in a controlled and secure manner.

High Endurance Non-volatile Memory segments
– 64 Kbytes of In-System Reprogrammable Flash program memory
– 2 Kbytes EEPROM
– 4 Kbytes Internal SRAM
– Write/Erase Cycles: 10,000 Flash/100,000 EEPROM
– Data retention: 20 years at 85°C/100 years at 25°C(1)
– Optional Boot Code Section with Independent Lock Bits
In-System Programming by On-chip Boot Program
True Read-While-Write Operation
– Up to 64 Kbytes Optional External Memory Space
– Programming Lock for Software Security
– SPI Interface for In-System Programming
JTAG (IEEE std. 1149.1 Compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– Two Expanded 16-bit Timer/Counters with Separate Prescaler, Compare Mode, and Capture Mode
– Real Time Counter with Separate Oscillator
– Two 8-bit PWM Channels
– 6 PWM Channels with Programmable Resolution from 1 to 16 Bits
– 8-channel, 10-bit ADC
8 Single-ended Channels
7 Differential Channels
2 Differential Channels with Programmable Gain (1x, 10x, 200x)
– Byte-oriented Two-wire Serial Interface
– Dual Programmable Serial USARTs
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Six Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, Standby
and Extended Standby
– Software Selectable Clock Frequency
– ATmega103 Compatibility Mode Selected by a Fuse
– Global Pull-up Disable
I/O and Packages
– 53 Programmable I/O Lines
– 64-lead TQFP and 64-pad QFN/MLF
Operating Voltages
– 2.7V – 5.5V for ATmega64L
– 4.5V – 5.5V for ATmega64
The purpose of this service is not to encourage unauthorized hack activities, but to support product lifecycle continuity, intellectual property preservation, and system recovery for authorized users. Typical use cases include restoring EEPROM data after a supplier shutdown, cloning a proven controller for small-batch manufacturing, duplicating a stable program file for backup, or migrating firmware to a newer platform while keeping original behavior intact.
During the recovery process, difficulties may arise from aging silicon, partially corrupted memory cells, undocumented firmware revisions, or deeply encrypted security configurations that require careful handling to avoid data loss. Despite these challenges, successful EEPROM and flash retrieval allows customers to rebuild their firmware archive, validate binary integrity, and securely store recovered source-level representations where applicable.
The benefits for end users include reduced downtime, lower redevelopment costs, extended product lifespan, and improved operational resilience, all while maintaining confidentiality and compliance. By delivering verified firmware, EEPROM, and memory files in usable formats, our Copy Chip ATmega64L EEPROM service provides a practical, professional solution for industries that rely on stable embedded systems and cannot afford to lose access to their secured microcontroller data.
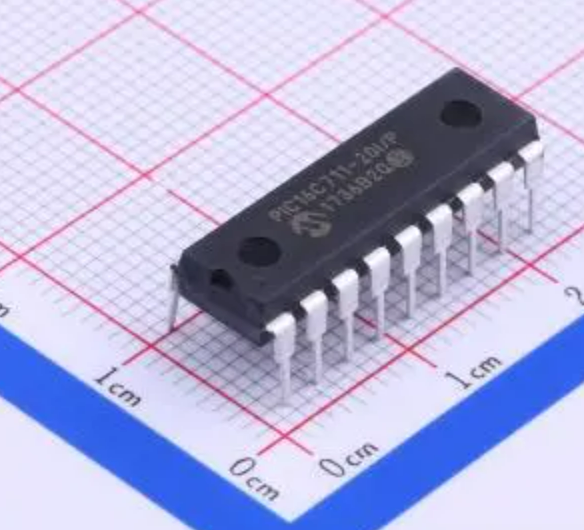
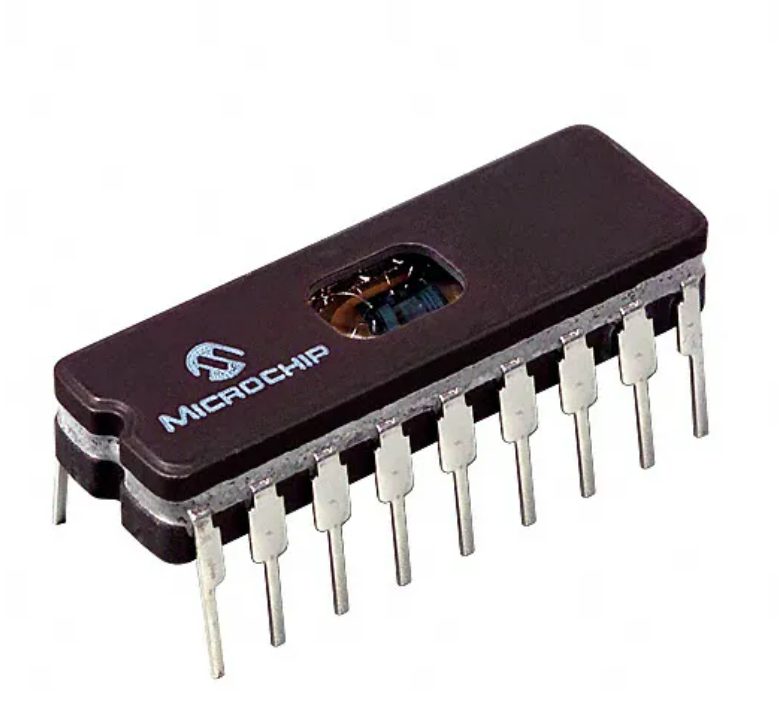
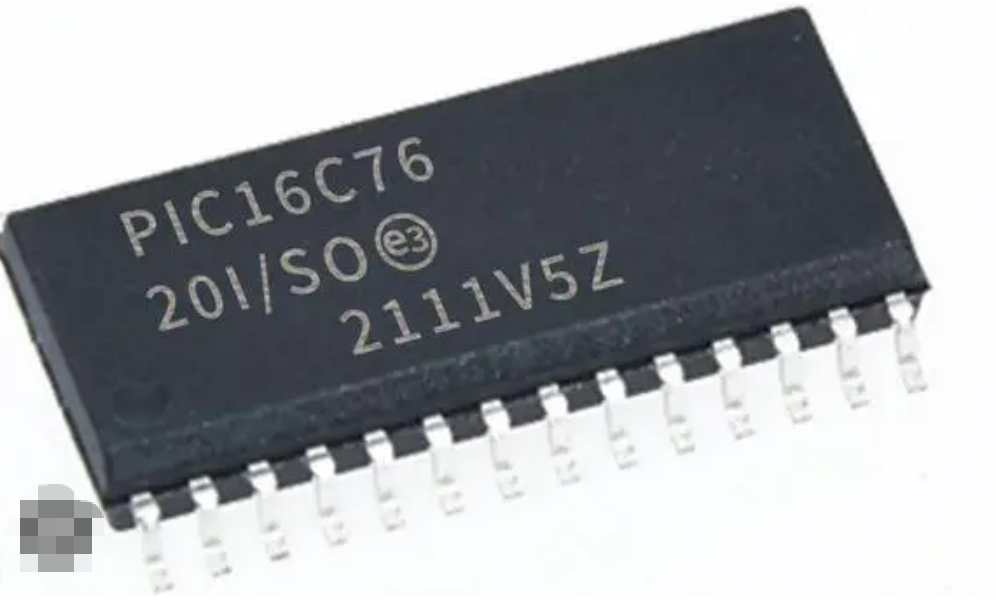
 Copy Microcontroller PIC16C76 Heximal
Copy Microcontroller PIC16C76 Heximal
The Microchip PIC16C76 is a classic 8-bit microcontroller that continues to operate in a wide range of industrial and commercial products. When customers search for Copy Microcontroller PIC16C76 Heximal, it is usually because the original source code, program, or compiled firmware has been lost, yet the hardware remains essential to daily operations. Our professional recovery service is designed to help authorized owners retrieve, clone, or duplicate the internal heximal and binary content from protected and secured PIC16C76 devices—without exposing sensitive technical details.
We can Copy Microcontroller PIC16C76 Heximal, please view the Microcontroller PIC16C76 features for your reference:
Any instruction which writes, operates internally as a read followed by a write operation. The BCF and BSF instructions, for example, read the register into the CPU, execute the bit operation and write the result back to the register.

Thanks to its stable architecture, integrated peripherals, and reliable embedded design, the PIC16C76 has been widely used in:
- Industrial automation controllers and monitoring systems
- Measurement instruments and data acquisition devices
- Motor control and power management modules
- Consumer electronics and appliance controllers
- Educational platforms and OEM-specific embedded products
In these applications, critical operational logic and calibration data are stored in internal flash, EEPROM, and memory areas. Once these regions become locked or encrypted, standard programmers are unable to access the internal archive, creating major risks for maintenance and production continuity.
Caution must be used when these instructions are applied to a port with both inputs and outputs defined. For example, a BSF operation on bit5 of PORTB will cause all eight bits of PORTB to be read into the CPU.

Our service supports legitimate clients who need to attack access barriers in order to recover their own intellectual property. We help customers break through protective security mechanisms and safely decode the embedded program stored within the microcontroller.
Depending on the device condition and security configuration, recovery may involve controlled analysis, advanced inspection, or authorized decapsulation. The final result is a verified file containing the recovered firmware, delivered as a binary or heximal image suitable for archiving, system migration, or controlled duplication. We do not disclose how the recovery is performed, and we do not provide instructions on how to hack devices.

Then the BSF operation takes place on bit5 and PORTB is written to the output latches. If another bit of PORTB is used as a bi-directional I/O pin (e.g., bit0) and it is defined as an input at this time, the input signal present on the pin itself would be read into the CPU and rewritten to the data latch of this particular pin, overwriting the previous content.
Organizations rely on this service for several important reasons:
- Restoring production when original source code is unavailable
- Avoiding costly redesign of proven legacy hardware
- Creating a secure archive for long-term product support
- Enabling accurate system clone or duplicate manufacturing
- Protecting existing engineering investment and operational know-how
Recovered firmware allows businesses to extend product life cycles, reduce downtime, and maintain control over their embedded systems.
As long as the pin stays in the input mode, no problem occurs. However, if bit0 is switched to an output, the content of the data latch may now be unknown.
Reading the port register, reads the values of the port pins. Writing to the port register writes the value to the port latch. When using read-modify-write instructions (ex.BCF, BSF, etc.) on a port, the value of the port pins is read, the desired operation is done to this value, and this value is then written to the port latch.
Example 5-4 shows the effect of two sequential read-modify-write instructions on an I/O port. A pin actively outputting a Low or High should not be driven from external devices at the same time in order to change the level on this pin (“wired-or”, “wired-and”). The resulting high output currents may damage the chip.
The actual write to an I/O port happens at the end of an instruction cycle, whereas for reading, the data must be valid at the beginning of the instruction cycle (Figure 5-10). Therefore, care must be exercised if a write followed by a read operation is carried out on the same I/ O port.
The sequence of instructions should be such to allow the pin voltage to stabilize (load dependent) before the next instruction which causes that file to be read into the CPU is executed. Otherwise, the previous state of that pin may be read into the CPU rather than the new state in the process of Copy Microcontroller PIC16C76 Heximal. When in doubt, it is better to separate these instructions with a NOP or another instruction not accessing this I/O port.
It can directly interface to an 8-bit microprocessor data bus. The external microprocessor can read or write the PORTD latch as an 8-bi t latch. Setting bit PSPMODE enables port pin RE0/RD/AN5 to be the RD input, RE1/WR/AN6 to be the WR input and RE2/CS/AN7 to be the CS (chip select) input to Crack MCU. For this functionality, the corresponding data direction bits of the TRISE register (TRISE<2:0>) must be configured as inputs (set) and the A/D port configuration bits PCFG2:PCFG0 (ADCON1<2:0>) must be set, which will configure pins RE2:RE0 as digital I/O.
Each PIC16C76 unit is first evaluated to confirm feasibility. Once approved, controlled processes are applied to retrieve internal data while preserving memory integrity. The recovered output is validated to ensure completeness and usability. Common difficulties include aging silicon, partial memory degradation, undocumented device revisions, or deeply secured configurations. These challenges require experience and precision to ensure reliable results without data loss.
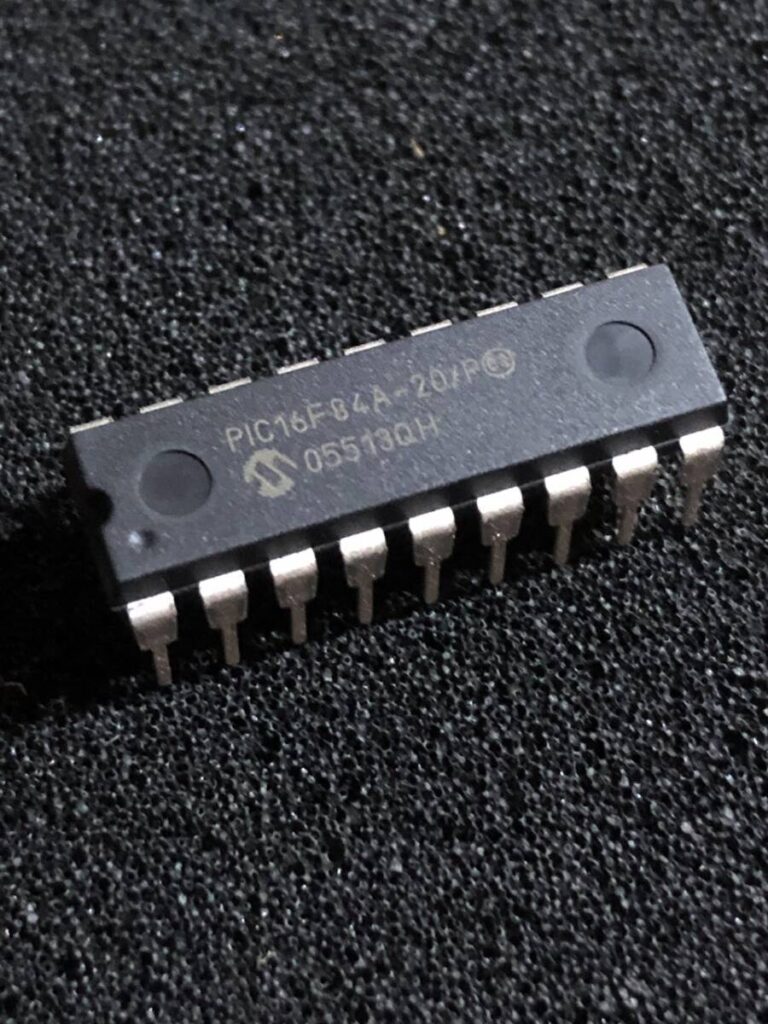
 Copy IC PIC16F84 Code
Copy IC PIC16F84 Code
The Microchip PIC16F84 is one of the most widely recognized microcontrollers in the history of embedded design. Even today, it remains active inside countless industrial controllers, educational platforms, automation modules, access systems, and consumer electronics. When organizations search for Copy IC PIC16F84 Code, it is typically because the original source code, program, or compiled firmware has been lost, while the hardware must continue operating. Our specialized service is designed to help legitimate owners retrieve, clone, or duplicate the embedded binary or heximal content from protected devices—without exposing any technical methods.
All PICmicro™ microcontrollers employ an advanced RISC architecture. PIC16F8X devices have enhanced core features, eight-level deep stack, and multiple internal and external interrupt sources. The separate instruction and data buses of the Harvard architecture allow a 14-bit wide instruction word with a separate 8-bit wide data bus which can be used for Copy IC PIC16F84 Code. The two stage instruction pipeline allows all instructions to execute in a single cycle, except for program branches (which require two cycles). A total of 35 instructions (reduced instruction set) are available. Additionally, a large register set is used to achieve a very high performance level.

The PIC16F84 gained popularity due to its simplicity, reliability, and on-chip flash and EEPROM memory, which made it ideal for early embedded applications such as:
- Industrial automation and timing controllers
- Educational development boards and training systems
- Home appliances and basic consumer electronics
- Security alarms and access-control units
- Small robotic and sensor-based products
Its non-volatile memory allows systems to store logic and configuration data even after power loss, making the internal archive essential for maintenance and future expansion.
PIC16F8X microcontrollers typically achieve a 2:1 code compression and up to a 4:1 speed improvement (at 20 MHz) over other 8-bit microcontrollers in their class. The PIC16F8X has up to 68 bytes of RAM, 64 bytes of Data EEPROM memory, and 13 I/O pins. A timer/counter is also available.
Our service assists authorized clients who need to attack or break access restrictions imposed by locked, encrypted, or secured configurations. Standard programmers cannot decode or read these devices once protection is enabled. Through controlled analysis and, when required, approved decapsulation, we safely retrieve the internal program and reconstruct a usable file.
We do not provide instructions on how to hack devices. All processes are handled internally, and customers receive only the final recovered firmware, suitable for validation, redesign, or controlled replication.
The PIC16CXX family has special features to reduce external components, thus reducing cost, enhancing system reliability and reducing power consumption.
There are four oscillator options, of which the single pin RC oscillator provides a low-cost solution, the LP oscillator minimizes power consumption, XT is a standard crystal, and the HS is for High Speed crystals.
Clients use this service to:
- Restore production when original developers are unavailable
- Avoid costly redesign of proven legacy systems
- Build verified archives for long-term product support
- Enable accurate clone or duplicate manufacturing
- Preserve intellectual property already embedded in hardware
Recovering the PIC16F84 code ensures continuity, lowers risk, and protects prior engineering investment.
The SLEEP (power-down) mode offers power saving. The user can wake the chip from sleep through several external and internal interrupts and resets. A highly reliable Watchdog Timer with its own on-chip RC oscillator provides protection against software lock-up. The devices with Flash program memory allow the same device package to be used for prototyping and production.

In-circuit reprogrammability allows the code to be updated without the device being removed from the end application. This is useful in the development of many applications where the device may not be easily accessible to Copy IC PIC16F84 Code, but the prototypes may require code updates. This is also useful for remote applications where the code may need to be updated (such as rate information).
The PIC16F8X fits perfectly in applications ranging from high speed automotive and appliance motor control to low-power remote sensors, electronic locks, security devices and smart cards. The Flash/EEPROM technology makes customization of application programs (transmitter codes, motor speeds, receiver frequencies, security codes, etc.) extremely fast and convenient.

The small footprint packages make this microcontroller series perfect for all applications with space limitations. Low-cost, low-power, high performance, ease-of-use and I/O flexibility make the PIC16F8X very versatile even in areas where no microcontroller use has been considered (e.g., timer functions; serial communication; capture, compare and PWM functions; and co-processor applications).
The serial in-system programming feature (via two pins) offers flexibility of customizing the product after complete assembly and testing. This feature can be used to serialize a product, store calibration data, or program the device with the current firmware before shipping.
Typical difficulties include aging silicon, partially degraded EEPROM, undocumented revisions, or deeply protective security settings. These challenges require experience and precision to ensure complete and reliable output.
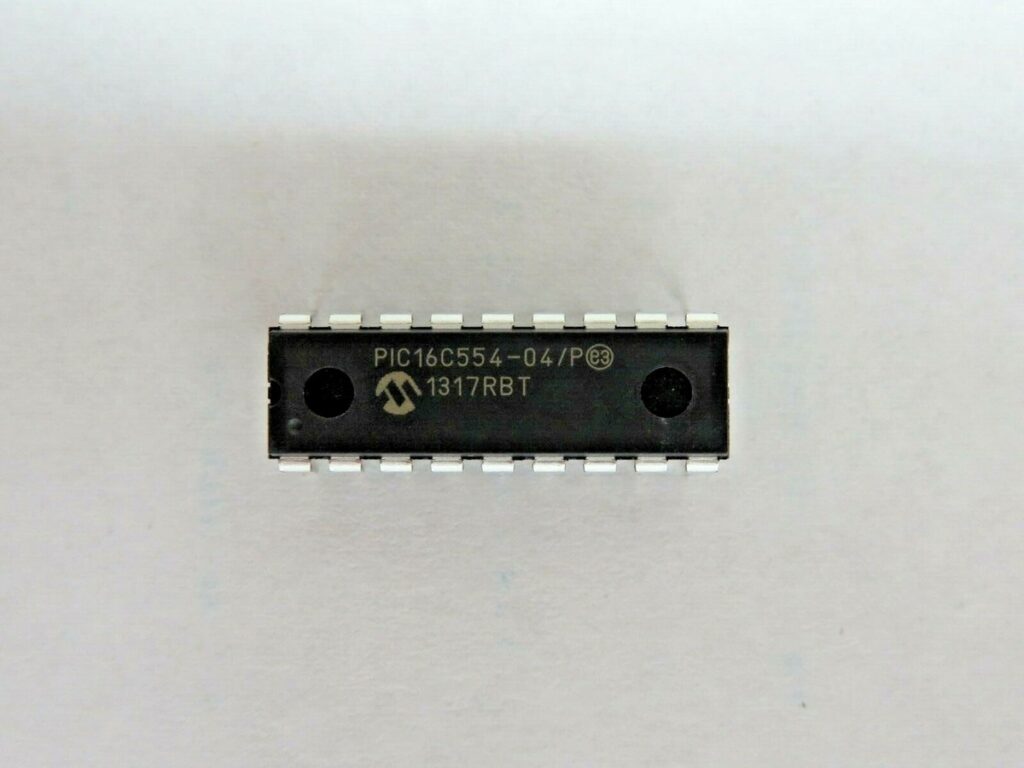
 Copy MCU PIC16C554A Eeprom
Copy MCU PIC16C554A Eeprom
The Microchip PIC16C554A is a classic 8-bit microcontroller that continues to operate inside many long-lifecycle products across industrial, consumer, and control-system markets. When customers search for Copy MCU PIC16C554A EEPROM, it is usually because the original firmware, source code, or internal archive has been lost, while the equipment itself remains mission-critical. In these cases, our specialized service provides a reliable path to retrieve, clone, or duplicate the original embedded program without disclosing sensitive technical methods.
The PIC16C55X(A) are 18 and 20-Pin EPROM-based members of the versatile PIC16CXX family of low-cost, high-performance, CMOS, fully-static, 8-bit microcontrollers which is the reason for Copy MCU PIC16C554A Eeprom.
All PICmicro™ microcontrollers employ an advanced RISC architecture. The PIC16C55X(A) have enhanced core features, eight-level deep stack, and multiple internal and external interrupt sources. The separate instruction and data buses of the Harvard architecture allow a 14-bit wide instruction word with the separate 8-bit wide data.

Thanks to its simple architecture, stable timing, and low power consumption, the PIC16C554A has been widely adopted in:
- Industrial control panels and signal converters
- Consumer appliances and portable electronic products
- Automotive auxiliary electronics and monitoring units
- Security devices and access-control modules
- Educational and OEM-specific embedded systems
In many of these designs, custom logic and calibration data are stored inside EEPROM, flash, or internal memory, often protected by locked, encrypted, or secured configurations.
The two-stage instruction pipeline allows all instructions to execute in a single-cycle, except for program branches (which require two cycles). A total of 35 instructions (reduced instruction set) are available. Additionally, a large register set gives some of the architectural innovations used to achieve a very high performance.
PIC16C55X(A) microcontrollers typically achieve a 2:1 code compression and a 4:1 speed improvement over other 8-bit microcontrollers in their class.
Our service focuses on helping legitimate owners break through inaccessible protection layers in order to recover their own binary or heximal file. We support projects where standard tools cannot read the embedded firmware due to protective security settings.
Depending on the condition of the device, recovery may involve controlled analysis, specialized evaluation, or advanced inspection such as authorized decapsulation. The goal is to safely decode and reconstruct the internal program structure while preserving data integrity. We do not provide instructions on how to hack devices; all work is performed internally under strict confidentiality.
The PIC16C554(A) and PIC16C556A have 80 bytes of RAM. The PIC16C558(A) has 128 bytes of RAM. Each device has 13 I/O pins and an 8-bit timer/counter with an 8-bit programmable prescaler.
PIC16C55X(A) devices have special features to reduce external components, thus reducing cost, enhancing system reliability and reducing power consumption in the process of Copy MCU PIC16C554A Eeprom.
There are four oscillator options, of which the single pin RC oscillator provides a low-cost solution, the LP oscillator minimizes power consumption, XT is a standard crystal, and the HS is for High Speed crystals. The SLEEP (power-down) mode offers power saving.

The user can wake up the MCU from SLEEP through several external and internal interrupts and reset.A highly reliable Watchdog Timer with its own on-MCU RC oscillator provides protection against software lock- up. A UV-erasable CERDIP-packaged version is ideal for code development while the cost-effective One-Time Programmable (OTP) version is suitable for production in any volume.
Customers rely on our PIC16C554A EEPROM recovery service to:
- Restore production when original source code is unavailable
- Avoid costly redesign of legacy products
- Build verified archives for long-term maintenance
- Enable accurate system clone or controlled duplicate manufacturing
- Protect existing engineering investment and intellectual property
Recovered firmware allows businesses to maintain continuity, extend product life cycles, and reduce operational risk.
Challenges in the Recovery Process
Typical difficulties include aged silicon, partial memory degradation, deeply protected configurations, or undocumented variations between chip revisions. These factors require experience and precision to ensure a complete and usable output.

 Attack Chip PIC16C622A Software
Attack Chip PIC16C622A Software
The Microchip PIC16C622A remains a widely deployed 8-bit MCU across consumer electronics, industrial automation, automotive interfaces, security devices, sensor modules, and legacy embedded systems. Its reliability, compact architecture, and stable flash and eeprom handling make it a long-lasting favorite among engineers. However, once development archives or source code are lost, the internal software becomes extremely difficult to access—especially when the chip is in a protected, encrypted, or fully locked configuration. Our specialized service under the topic Attack Chip PIC16C622A Software is designed to help legitimate product owners safely retrieve, clone, or duplicate the MCU’s original firmware, without revealing or disclosing any sensitive technical methods.

Industrial Importance of the PIC16C622A
The PIC16C622A delivers a balance of low cost, low power usage, and versatile I/O features. This makes it a common choice in:
- Portable electronic products
- Access control, authentication, and smart security hardware
- Motor controllers and instrumentation devices
- Home appliances and small embedded consumer systems
- Customized OEM modules with long production cycles
In many of these applications, the internal binary, heximal, and configuration memory contain unique logic, calibration routines, and tailored program structures essential for stable system performance.

The high performance of the PIC16C62X family can be attributed to a number of architectural features commonly found in RISC microprocessors which is critical feature for Attack Chip PIC16C622A Software. To begin with, the PIC16C62X uses a Harvard architecture, in which, program and data are accessed from separate memories using separate busses. This improves bandwidth over traditional von Neumann architecture where program and data are fetched from the same memory. Separating program and data memory further allows instructions to be sized differently than 8-bit wide data word. Instruction opcodes are 14-bits wide making it possible to have all single word instructions.
A 14-bit wide program memory access bus fetches a 14-bit instruction in a single cycle. A two-stage pipeline overlaps fetch and execution of instructions.
Consequently, all instructions (35) execute in a single-cycle (200 ns @ 20 MHz) except for program branches. The PIC16C620A and PIC16CR620A address 512 x 14 on-chip program memory. The PIC16C621(A) addresses 1K x 14 program memory. The PIC16C622(A) addresses 2K x 14 program memory. All program memory is internal.
The PIC16C62X can directly or indirectly address its register files or data memory. All special function registers including the program counter are mapped in the data memory. The PIC16C62X have an orthogonal (symmetrical) instruction set that makes it possible to carry out any operation on any register using any addressing mode in order to Attack Chip PIC16C622A Software. This symmetrical nature and lack of ‘special optimal situations’ make programming with the PIC16C62X simple yet efficient. In addition, the learning curve is reduced significantly.
The PIC16C62X devices contain an 8-bit ALU and working register. The ALU is a general purpose arithmetic unit. It performs arithmetic and Boolean functions between data in the working register and any register file.
The ALU is 8-bit wide and capable of addition, subtraction, shift and logical operations. Unless otherwise mentioned, arithmetic operations are two’s complement in nature. In two-operand instructions, typically one operand is the working register (W register). The other operand is a file register or an immediate constant when Unlock Microcontroller. In single operand instructions, the operand is either the W register or a file register.

The W register is an 8-bit working register used for ALU operations. It is not an addressable register Depending on the instruction executed, the ALU may affect the values of the Carry (C), Digit Carry (DC), and Zero (Z) bits in the STATUS register. The C and DC bits operate as a Borrow and Digit Borrow out bit, respectively, bit in subtraction. See the SUBLW and SUBWF instructions for examples.
Our Service: Safe and Controlled Recovery of Embedded Software
We help businesses and engineers who need to break through inaccessible or obsolete MCU barriers to recover their own program files. Our objective is not unauthorized hacking but legitimate data restoration for owners who have lost the original design file or development archive.
Our service includes:
- Chip evaluation to confirm feasibility
- High-level security assessment before any attack or decode operation
- Optional non-destructive techniques or advanced decapsulation, depending on chip condition
- Secure extraction of internal firmware, calibration data, or eeprom contents
- Output of a clean, validated binary or heximal program ready for production or system repair
All internal procedures remain confidential, and we do not share technical details of how protections are unlocked.
General Concept of the Recovery Process (Non-Technical Overview)
Recovering embedded software from a secured PIC16C622A involves precisely controlled steps that may include reading device states, analyzing memory integrity, and applying specialized methods to decode or retrieve protected data. The goal is always to preserve the original program while avoiding any physical damage to the chip.
Why End-Users Choose This Service
Customers depend on this recovery solution for several business-critical reasons:
- Reviving production lines when development source code is lost
- Eliminating high redesign costs for legacy devices
- Ensuring long-term serviceability for field-deployed equipment
- Restoring intellectual property already paid for and designed internally
- Maintaining competitive advantage by controlling system logic
The ability to clone or duplicate the recovered firmware ensures product continuity without forced redesign.
Technical Challenges You Might Encounter
Some PIC16C622A units exhibit difficulties such as worn flash, degraded memory, heavy encrypted protections, or complex protective configurations. These conditions require precise handling to avoid partial or corrupted data output. Our team is experienced in processing such cases with the highest reliability.
 Attack Microcontroller PIC16C710 Program
Attack Microcontroller PIC16C710 Program
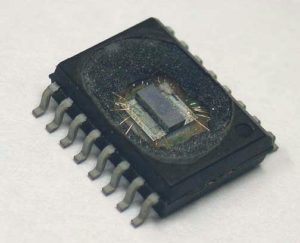
The Microchip PIC16C710 remains widely used in industrial controllers, home appliances, automotive interfaces, low-power automation boards, and specialized embedded modules. Over time, many companies face the challenge of maintaining or replicating systems built around this MCU, only to discover that the internal program, calibration data, or configuration eeprom cannot be accessed due to protected, encrypted, or fully locked security mechanisms. Our dedicated service under the subject Attack Microcontroller PIC16C710 Program is built specifically to help legitimate device owners retrieve and secure the original firmware when conventional development files or source code are no longer available.

Why the PIC16C710 Is Still Important Across Industries
Although it is part of an earlier generation of Microchip devices, the PIC16C710 offers dependable performance, integrated analog functionality, compact architecture, and stable embedded flash technology. These traits make it ideal for:
- Consumer electronic modules and appliance control boards
- Analog measurement devices and sensor processing units
- Automotive accessory drivers and interface systems
- Machine automation modules and industrial control panels
- Legacy devices that rely on highly customized logic
The internal binary and heximal code inside the PIC16C710 is often the heart of the product’s functional design—meaning that losing it can completely halt production or repair capabilities.
Our Service: Controlled Recovery of Protected Firmware
We provide specialized assistance to customers who need to break the barrier of inaccessible memory and safely retrieve, clone, or duplicate the MCU’s file contents. Our service focuses on legitimate recovery—never unauthorized hacking—and is structured to help owners restore what rightfully belongs to them.

What we offer includes:
- Non-destructive analysis of the chip’s protection state
- Controlled operations that may include chip-level evaluation or optional decapsulation, depending on condition
- Secure extraction of internal program, calibration memory, or eeprom
- Delivery of clean, verified firmware images suitable for future production or redesign
All technical processes remain confidential; we do not reveal how protections are bypassed or how decoding mechanisms function. We ensure compliance, safety, and professional handling.

We can Attack Microcontroller PIC16C710 Program, please view the Microcontroller PIC16C710 features for your reference:
PIC16C71X Microcontroller Core Features:
· High-performance RISC CPU
· Only 35 single word instructions to learn
· All single cycle instructions except for program branches which are two cycle
· Operating speed: DC – 20 MHz clock input DC – 200 ns instruction cycle
· Up to 2K x 14 words of Program Memory, up to 128 x 8 bytes of Data Memory (RAM)
· Interrupt capability
· Eight level deep hardware stack
· Direct, indirect, and relative addressing modes
· Power-on Reset (POR)
· Power-up Timer (PWRT) and Oscillator Start-up Timer (OST)
· Watchdog Timer (WDT) with its own on-chip RC oscillator for reliable operation;
· Programmable code-protection
· Power saving SLEEP mode
· Selectable oscillator options
· Low-power, high-speed CMOS EPROM technology
· Fully static design
· Wide operating voltage range: 2.5V to 6.0V
· High Sink/Source Current 25/25 mA
· Commercial, Industrial and Extended temperature ranges
· Program Memory Parity Error Checking Circuitry
with Parity Error Reset (PER) (PIC16C715)
· Low-power consumption:
– < 2 mA @ 5V, 4 MHz
– 15 µA typical @ 3V, 32 kHz
– < 1 µA typical standby current
General Concept of the Recovery Process (High-Level Explanation Only)
Each PIC16C710 device undergoes a detailed preliminary check to determine the feasibility of recovery. Once confirmed, carefully orchestrated operations are performed to decode or access the internal archive without compromising memory integrity. The final output typically includes a binary or heximal dump that can be used to reprogram new units or verify system logic.
Why Clients Depend on This Service
Companies and engineers rely on our service to:
- Continue manufacturing products after losing original source code
- Rebuild or update legacy systems without redesigning from zero
- Reduce downtime caused by obsolete or discontinued MCUs
- Protect their technical investments and keep service departments operational
- Maintain strategic control over product functionality for the long term
Our ability to attack secured microcontrollers legally and professionally ensures business continuity and engineering independence.
Possible Challenges During Recovery
Some PIC16C710 units present more complex issues, such as degraded memory, ultra-tight secured configurations, or device aging that affects reliability. These conditions require specialized handling to guarantee a stable and complete firmware output.
 Attack MCU PIC16F711 Heximal
Attack MCU PIC16F711 Heximal
Embedded systems built on the Microchip PIC16F711 microcontroller are widely deployed in industrial automation, automotive subsystems, consumer electronics, and sensor-based applications. Over time, these systems often become inaccessible due to protected, locked, or encrypted firmware configurations, preventing rightful owners from maintaining or updating their equipment. Our specialized service, centered on the keyword Attack MCU PIC16F711 Heximal, provides a secure, authorized solution to retrieve, clone, and restore embedded program files, binary data, and heximal archives—without disclosing proprietary technical methods.
The PIC16C71X family has special features to reduce external components, thus reducing cost, enhancing system reliability and reducing power consumption which is critical for Attack MCU PIC16F711 Heximal.
There are four oscillator options, of which the single pin RC oscillator provides a low-cost solution, the LP oscillator minimizes power consumption, XT is a standard crystal, and the HS is for High Speed crystals. The SLEEP (power-down) feature provides a power saving mode. The user can wake up the MCU from SLEEP through several external and internal interrupts and resets.
The PIC16F711 is a versatile 8-bit microcontroller known for its integrated analog-to-digital converters, compact design, and low-power operation. It is commonly found in:
- Industrial Control Modules: Sensor interfaces, motor controllers, and PLC peripherals.
- Automotive Electronics: Auxiliary control units, lighting systems, and diagnostic tools.
- Consumer Appliances: Power management systems, remote controls, and smart home devices.
- Medical Devices: Portable monitors and diagnostic equipment requiring reliable embedded control.
Its secured flash and EEPROM memory often store calibration data, operational logic, and configuration parameters critical to system functionality.
A highly reliable Watchdog Timer with its own on-MCU RC oscillator provides protection against software lock up. A UV erasable CERDIP packaged version is ideal for code development while the cost-effective One-Time-Programmable (OTP) version is suitable for production in any volume.
The PIC16C71X family fits perfectly in applications ranging from security and remote sensors to appliance control and automotive which is the reason for its MCU cracking. The EPROM technology makes customization of application programs (transmitter codes, motor speeds, receiver frequencies, etc.) extremely fast and convenient.
We assist clients in scenarios where firmware archives are lost, corrupted, or locked due to protective settings. Our end-to-end solution includes:
- Non-Destructive Analysis: Assessing the device’s security configuration and memory integrity.
- Controlled Extraction: Using advanced techniques to decode and retrieve the embedded heximal or binary program.
- Data Validation: Verifying the integrity of extracted firmware and eeprom data.
- Legal Compliance: Ensuring all work is conducted under authorization and confidentiality agreements.
We do not disclose methods to hack or decapsulate devices for unauthorized purposes. Instead, we deliver a validated file or archive that enables clients to duplicate, migrate, or restore their systems.
The small footprint packages make this microcontroller series perfect for all applications with space limitations. Low cost, low power, high performance, ease of use and I/O flexibility make the PIC16C71X very versatile even in areas where no microcontroller use has been considered before Attack MCU PIC16F711 Heximal (e.g. timer functions, serial communication, capture and compare, PWM functions and coprocessor applications).

- Minimized Downtime: Rapid recovery of operational firmware keeps production lines and legacy systems running.
- IP Preservation: Safeguard proprietary source code and calibration data embedded in the microcontroller.
- Legacy System Support: Extend the lifespan of equipment reliant on obsolete or unsupported hardware.
- Authorized Cloning: Legally duplicate firmware for backup, scaling, or replacement units.
Users familiar with the PIC16C5X microcontroller family will realize that this is an enhanced version of the PIC16C5X architecture. Please refer to Appendix A for a detailed list of enhancements. Code written for the PIC16C5X can be easily ported to the PIC16CXX family of devices.
- Advanced Protections: Some PIC16F711 units employ layered encrypted or secured configurations.
- Hardware Degradation: Aging components may lead to partial memory corruption or read failures.
- Device Variants: Slight differences in silicon revisions can complicate extraction efforts.
Despite these challenges, our systematic approach maximizes success rates while prioritizing device integrity and data confidentiality. For organizations facing firmware accessibility issues with the PIC16F711, our service offers a reliable, ethical path to recover, clone, and preserve critical embedded data. By combining technical expertise with legal compliance, we help clients maintain operational continuity and protect their intellectual property.