Posts Tagged ‘odnaleźć układ scalony eeprom’
 Break IC PIC16F685 Code
Break IC PIC16F685 Code
When an embedded system depends on the Microchip PIC16F685, losing access to its program or finding the device set to protected can halt operations and complicate maintenance. Our service, searchable under the keyword Break IC PIC16F685 Code, helps authorized owners and engineers open, readout, restore, and duplicate the firmware/binary/heximal contents of these microcontrollers. We deliver validated memory archives and high-level analysis while strictly avoiding publication of methods to illegally crack or hack protections.
The need to copy, clone, or duplicate a PIC16F685’s program file arises in many legitimate scenarios: restoring corrupted flash or EEPROM after a failure, recovering crucial calibration data, preparing authorized spares, or migrating long-lived products to replacement hardware. In many cases the firmware is locked or secured by the original integrator; safely extracting a verified binary or heximal dump can be the fastest route to restore operation without redesign.
We can Break IC PIC16F685 Code, please view the Ic PIC16F685 features for your reference:
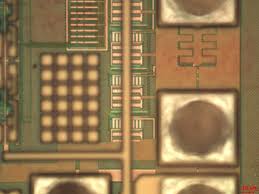
The PIC16F685 has a 13-bit program counter capable of addressing an 8K x 14 program memory space. Only the first 1K x 14 (0000h-03FFh) is physically implemented for the PIC16F631, the first 2K x 14 (0000h-07FFh) for the PIC16F677/PIC16F687, and the first 4K x 14 (0000h-0FFFh) for the PIC16F685/PIC16F689/ PIC16F690 when Break Ic. Accessing a location above these boundaries will cause a wraparound. The Reset vector is at 0000h and the interrupt vector is at 0004h.
The data memory (see Figures 2-6 through 2-8) is partitioned into four banks which contain the General Purpose Registers (GPR) and the Special Function Registers (SFR). The Special Function Registers are located in the first 32 locations of each bank. The CALL, RETURN RETFIE, RETLW.
General Purpose Registers, implemented as static RAM, are located in the last 96 locations of each Bank. Register locations F0h-FFh in Bank 1, 170h-17Fh in Bank 2 and 1F0h-1FFh in Bank 3 point to addresses 70h-7Fh in Bank 0. The actual number of General Purpose Resisters (GPR) in each Bank depends on the device. Details are shown in Figures 2-4 through 2-8.
All other RAM is unimplemented and returns ‘0’ when Reset Vector 0000h read. RP<1:0> of the STATUS register are the bank select bits:
The register file is organized as 128 x 8 in the PIC16F687 and 256 x 8 in the PIC16F685/PIC16F689/PIC16F690. Each register is accessed, either directly or indirectly, through the File Select Register (FSR) (see Section 2.4 “Indirect Addressing, INDF and FSR Registers”) by Break IC PIC16F685 Code.
SPECIAL FUNCTION REGISTERS
The Special Function Registers are registers used by the CPU and peripheral functions for controlling the desired operation of the device for MCU Reading (see Tables 2-1 through 2-4). These registers are static RAM.
The special registers can be classified into two sets: core and peripheral. The Special Function Registers associated with the “core” are described in this section. Registers related to the operation of peripheral features are described in the section of that peripheral feature.
The PIC16F685 is widely used where compact control and analog interfacing matter:
- Consumer electronics and appliance controllers.
- Industrial sensors and small automation modules.
- Instrumentation such as data loggers and test front-ends.
- Aftermarket automotive modules and hobbyist/legacy embedded systems.
Because these devices often store important configuration data and small program archives in on-chip memory, access to those files is frequently necessary for repair and continuity.
Unique features that affect recovery
This MCU combines flexible I/O, analog peripherals, and modest on-chip flash and EEPROM storage. Its architecture means that both program and calibration data may be tightly integrated, and many designs apply protective settings to prevent unauthorized copying. Those characteristics shape how recovery is approached and the kinds of deliverables that are most useful to end users.

What we provide (high-level, non-actionable)
Our engagements focus on ethical, non-destructive recovery outcomes. Typical services include: validated extraction of memory images (producing binary/heximal dumps), integrity checks and verification reports, and high-level disassembly summaries that help engineers interpret recovered program logic. We can assist clients in using recovered files to restore devices to operation or prepare migration packages for replacement hardware. We do not provide step-by-step instructions or tools intended to decrypt, bypass, or otherwise subvert manufacturer or integrator-applied protections.
General idea (conceptual)
A responsible recovery project begins with ownership verification and a feasibility assessment. Engineers then pursue conservative, evidence-based techniques to obtain a reliable archive of the device’s memory and to validate its integrity. The aim is to return a usable program image that enables authorized copying, duplication, or rebuilding while preserving device health and intellectual property.
Benefits and likely outcomes
Clients who use this service gain secure backups of previously inaccessible firmware and data, reduced downtime through faster restoration, and the ability to clone or duplicate devices for approved spares provisioning. Recovered binary or heximal archives support testing, compliance checks, and migration without starting from scratch.
Challenges and limitations
Recovery may be hindered by layered protections, partial data corruption, variant hardware revisions, or proprietary integrity checks. Full source-code reconstruction is not always possible; often the realistic deliverable is a validated firmware image with assembly-level annotations.
Ethics and authorization
We require proof of ownership or explicit authorization for all projects and operate under strict confidentiality agreements. Our mission is to help rightful owners unlock, restore, and preserve their embedded systems for lawful, constructive purposes only.

If you need to Break IC PIC16F685 Code for authorized recovery, maintenance, or archival purposes, our team provides confidential, professional support to retrieve and document your embedded firmware and data while protecting your IP and operational continuity.