Attack Chip ST62T00CB6 Firmware
Attack Chip ST62T00CB6 Firmware
We can Attack Chip ST62T00CB6 Firmware and extract its source code out of eeprom, please view below Chip ST62T00CB6 features for your reference:
Memories
– 1K or 2K bytes Program memory (OTP, EPROM, FASTROM or ROM) with read-out protection
– 64 bytes RAM
Clock, Reset and Supply Management
– Enhanced reset system
PDIP16
– Low voltage detector (LVD) for safe Reset and Crack MCU
– Clock sources: crystal/ceramic resonator or RC network, external clock, backup oscillator (LFAO)
– Oscillator safeguard (OSG)
SO16
– 2 Power saving modes: Wait and Stop
Interrupt Management
– 4 interrupt vectors plus NMI and RESET
– 9 external interrupt lines (on 2 vectors)
SSOP16
9 I/O Ports
– 9 multifunctional bidirectional I/O lines
– 4 alternate function lines
– 3 high sink outputs (20mA)
2 Timers
– Configurable watchdog timer
CDIP16W
– 8-bit timer/counter with a 7-bit prescaler
Analog Peripheral
(See Section 11.5 for Ordering Information)
– 8-bit ADC with 4 input channels (except on ST6203C) Instruction Set
Development Tools
– Full hardware/software development package
– 8-bit data manipulation
– 40 basic instructions
– 9 addressing modes
– Bit manipulation
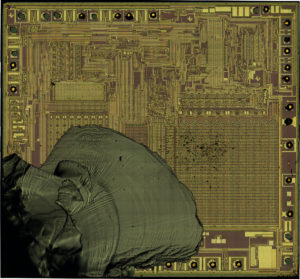
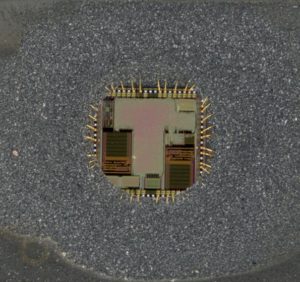
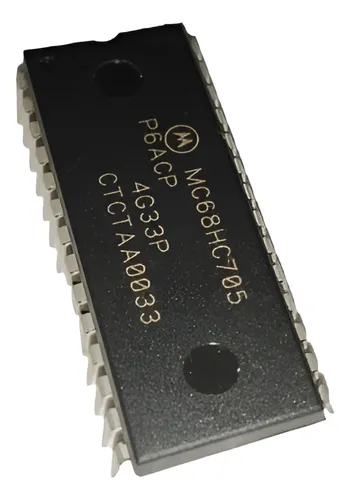
 Attack Microcontroller MC68HC705P6ACDW Binary
Attack Microcontroller MC68HC705P6ACDW Binary
The phrase “Attack Microcontroller MC68HC705P6ACDW Binary” captures a real and growing need across industries: authorized recovery and analysis of protected or legacy firmware on Freescale/Motorola MC68HC705 series devices. While the term “attack” may sound aggressive, in a professional setting it refers to disciplined, lawful work performed to restore, decode, or recover firmware and data from protected, locked, or encrypted embedded systems for legitimate purposes.

Many organizations encounter situations where the original firmware/binary/heximal files for an embedded product are lost, corrupted, or inaccessible. The MC68HC705 family has been widely used in automotive modules, industrial controllers, consumer electronics, and medical devices. When a device fails, or when a product line needs to be migrated or maintained decades after manufacture, technicians and engineers require access to the device’s flash, EEPROM, or program memory — whether to restore a corrupted archive, duplicate an aging system for production, or extract a file for validation and security review.
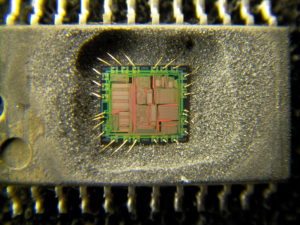
We can Attack Microcontroller MC68HC705P6ACDW Binary, please view Microcontroller MC68HC705P6ACDW feature for your reference:
Features of the MC68HC705P6A include:
· Low cost
· M68HC05 core
· 28-pin SOIC, PDIP, or windowed DIP package
· 4672 bytes of user EPROM (including 48 bytes of page zero EPROM and 16 bytes of user vectors)
· 239 bytes of bootloader ROM
· 176 bytes of on-chip RAM
· 4-channel 8-bit A/D converter
Our service approaches these needs with an emphasis on legality, confidentiality, and technical rigor. Typical, high-level engagements begin with an authorized assessment: verifying ownership or permission to work on the device, cataloging the data, program, and firmware formats involved, and agreeing on lawful objectives. We do not provide or publish instructions on disabling security protections or bypassing fuse bits; any recovery work is only performed under explicit client authorization and in compliance with local laws and contractual terms.

Rather than focusing on intrusive techniques, our process centers on safe, controlled analysis and verification. Deliverables commonly include a validated heximal binary dump (when lawful and possible), a cleaned and documented firmware image, and support for migration, duplication, or archival. For clients who require higher-level understanding, we can provide disassembly summaries and non-sensitive reverse-engineering reports that explain program structure and interfaces without revealing sensitive exploitation details.
· SIOP serial communications port
· 16-bit timer with output compare and input capture
· 20 bidirectional I/O lines and 1 input-only line
· PC0 and PC1 high-current outputs
· Single-chip, bootloader, and test modes
· Power-saving stop, halt, and wait modes
· Static EPROM mask option register (MOR) selectable options:
– COP watchdog timer enable or disable
– Edge-sensitive or edge- and level-sensitive external interrupt
– SIOP most significant bit (MSB) or least significant bit (LSB) first
– SIOP clock rates: OSC divided by 8, 16, 32, or 64
– Stop instruction mode, STOP or HALT
– EPROM security external lockout
– Programmable keyscan (pullups/interrupts) on PA0–PA7
The MC68HC705’s long service life and presence in critical equipment make such services invaluable for aftermarket support, forensic analysis, and security audits. Industries benefit by extending equipment lifetimes, ensuring continuity in production, and enabling vulnerability assessments that strengthen product resilience.
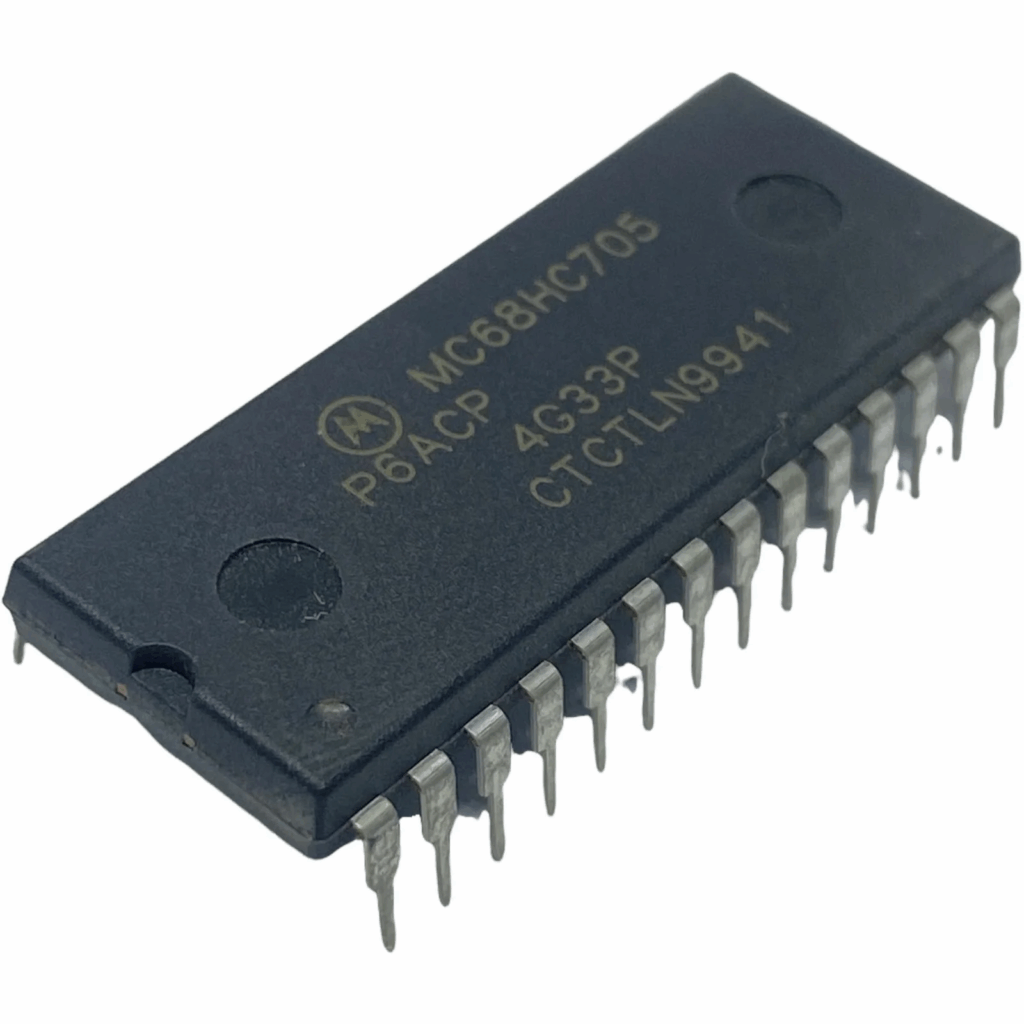
Finally, we emphasize transparency. Keywords like restore / crack / hack / decode / decrypt / unlock / open / copy / clone / duplicate reflect the range of outcomes clients seek; we pursue them only within legal, ethical boundaries and never offer step-by-step methods to defeat security mechanisms. If you need lawful firmware recovery, archival, or an authorized security assessment for MC68HC705 series parts, we provide confidential, professional assistance tailored to your compliance and engineering needs.
Circuit Engineering Company Limited continues to be recognized as the Southern China Leader in Services for IC Break, MCU crack, Chip Recover, Microcontroller Copy service. With the advancement of today’s modern circuit board technology, it is more important than ever to have specialists available to help you at a moment’s notice. Our engineering and commercial teams collectively have a vast amount of electronic experience covering field include Consumer Electronics, Industrial Automation Electronics, Wireless Communication Electronics., etc. For more information please contact us through email.
 Attack MCU TMX320F28027PTA Archive
Attack MCU TMX320F28027PTA Archive
We can Attack MCU TMX320F28027PTA Archive, please view MCU TMX320F28027PTA features for your reference:
Highlights
– High-Efficiency 32-Bit CPU ( TMS320C28x™)
– 60-MHz, 50-MHz, and 40-MHz Devices
– Single 3.3-V Supply
– Integrated Power-on and Brown-out Resets
– Two Internal Zero-pin Oscillators
– Up to 22 Multiplexed GPIO Pins
– Three 32-Bit CPU Timers
– On-Chip Flash, SARAM, OTP Memory
– Code-security Module
– Serial Port Peripherals (SCI/SPI/I2C)
– Enhanced Control Peripherals
· Low Device and System Cost:
– Single 3.3-V Supply
– No Power Sequencing Requirement
– Integrated Power-on and Brown-out Resets
– Small Packaging, as Low as 38-Pin Available
– Low Power
– No Analog Support Pins
· Clocking:
– Two Internal Zero-pin Oscillators
– On-Chip Crystal Oscillator/External Clock Input
– Dynamic PLL Ratio Changes Supported
Enhanced Pulse Width Modulator (ePWM) And High-Resolution PWM (HRPWM)
– Watchdog Timer Module
– Missing Clock Detection Circuitry
· Enhanced Capture (eCAP)
· Analog-to-Digital Converter (ADC)
· On-Chip Temperature Sensor
· Comparator
– 38-Pin and 48-Pin Packages
· High-Efficiency 32-Bit CPU ( TMS320C28x™)
– 60 MHz (16.67-ns Cycle Time)
– 50 MHz (20-ns Cycle Time)
– 40 MHz (25-ns Cycle Time)
– 16 x 16 and 32 x 32 MAC Operations
– 16 x 16 Dual MAC
– Harvard Bus Architecture
– Atomic Operations
– Fast Interrupt Response and Processing
– Unified Memory Programming Model
– Code-Efficient (in C/C++ and Assembly)
· Endianness: Little Endian
· Up to 22 Individually Programmable, Multiplexed GPIO Pins With Input Filtering
· Peripheral Interrupt Expansion (PIE) Block That Supports All Peripheral Interrupts to Unlock Microcontroller
· Three 32-Bit CPU Timers
· Independent 16-Bit Timer in Each ePWM
Module
· On-Chip Memory
– Flash, SARAM, OTP, Boot ROM Available
· 128-Bit Security Key/Lock
– Protects Secure Memory Blocks
– Prevents Firmware Reverse Engineering
· Serial Port Peripherals
– One SCI (UART) Module
– One SPI Module
– One Inter-Integrated-Circuit (I2C) Bus
· Advanced Emulation Features
– Analysis and Breakpoint Functions
– Real-Time Debug via Hardware
· 2802x, 2802xx Packages
– 38-Pin DA Thin Shrink Small-Outline Package (TSSOP)
– 48-Pin PT Low-Profile Quad Flatpack (LQFP)
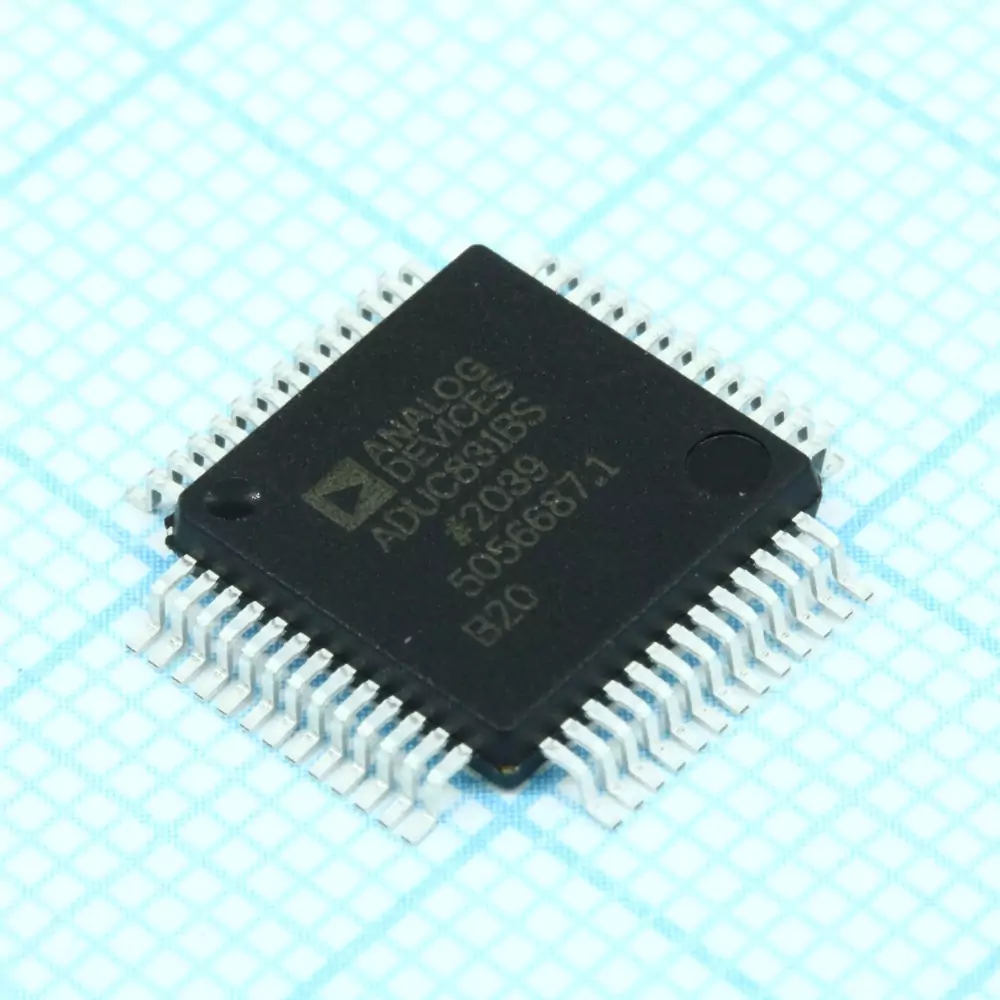
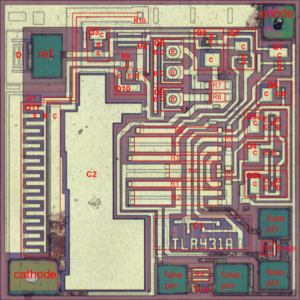
 Attack IC ADUC831BSZ Firmware
Attack IC ADUC831BSZ Firmware
The Analog Devices ADUC831BSZ is a powerful single-chip microcontroller that integrates a high-performance 8051 core with precision analog-to-digital converters and flash memory. Widely adopted in industrial automation, instrumentation, automotive electronics, and consumer devices, this chip is often deployed in environments where reliability and accuracy are paramount. To protect proprietary intellectual property, manufacturers frequently enable protective fuse bits and implement locked or encrypted firmware. This creates challenges when users need to access, restore, or modify the binary, heximal, or source code stored in its flash memory or EEPROM.

The Need for Firmware Recovery
There are many scenarios where end users require access to the firmware program of the ADUC831BSZ. For example:
- Recovering lost or corrupted data archives.
- Migrating existing systems to new hardware platforms.
- Conducting security audits or patching vulnerabilities.
- Cloning or duplicating a system for production scaling.
In such cases, the demand arises for a professional service to attack IC ADUC831BSZ firmware in order to crack, hack, decode, or decrypt the locked system and extract the protected program file.
General Steps of Unlocking and Extraction
Breaking the secured firmware of the ADUC831BSZ involves carefully engineered procedures. The most general steps include:
- Chip Identification – Recognizing the exact microcontroller variant and analyzing its fuse bit configuration.
- Protection Analysis – Studying the enabled security features, whether it involves simple code-lock mechanisms or encrypted flash memory.
- Fuse Bit Disablement – Using advanced techniques to bypass or disable protective bits without damaging the device.
- Firmware Dumping – Extracting the heximal file or binary program from the flash and EEPROM memory.
- Disassembly and Decryption – Decoding the low-level instructions, restoring the firmware to a usable format, and if required, reconstructing C/C++ source code.
These steps demand a combination of deep expertise in embedded systems and custom-engineered hardware interfaces to ensure successful recovery.
Unique Features of ADUC831BSZ

The ADUC831BSZ stands out due to:
- Integrated high-precision ADC/DAC for mixed-signal processing.
- On-chip flash memory with programmable protection levels.
- Low-power consumption, making it suitable for battery-powered devices.
- Enhanced embedded security, designed to safeguard proprietary program data.
While these features benefit developers, they also increase the difficulty of unlocking or copying the firmware once security measures are enabled.
Applications of Firmware Extraction
By successfully attacking and unlocking the firmware, end users gain the ability to:
- Restore original program files from damaged devices.
- Copy and clone embedded systems for legacy support.
- Duplicate memory archives for large-scale deployment.
- Perform reverse engineering for debugging, compatibility testing, or academic research.

Such capabilities are especially valuable in industrial control systems, medical instrumentation, automotive modules, and consumer electronics, where firmware access is often the key to extending the lifecycle of equipment or ensuring continued support.
Conclusion
The process to attack IC ADUC831BSZ firmware is not trivial, given the device’s protected and secured architecture. However, with advanced methods, it is possible to unlock, open, crack, and decode the embedded binary program stored inside its memory. The recovered heximal data can then be restored into functional form, enabling duplication, modification, or further development. This service provides clients with the essential access required to keep their embedded systems functional, optimized, and future-ready.
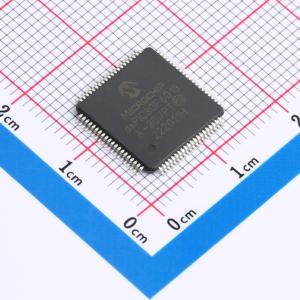
 Break Chip PIC16F720 Firmware
Break Chip PIC16F720 Firmware
The Microchip PIC16F720 is a popular 8-bit microcontroller widely deployed in industrial controls, consumer electronics, automotive modules, and a variety of embedded applications. With its compact architecture, integrated flash memory, and reliable performance, it is a preferred choice for engineers seeking efficiency and cost-effectiveness. However, many of these devices are shipped with protective or locked mechanisms enabled, making it nearly impossible to directly access or copy the stored firmware, binary data, or heximal program file. This is where professional reverse-engineering techniques come into play, offering the capability to Break Chip PIC16F720 Firmware and recover valuable system code.
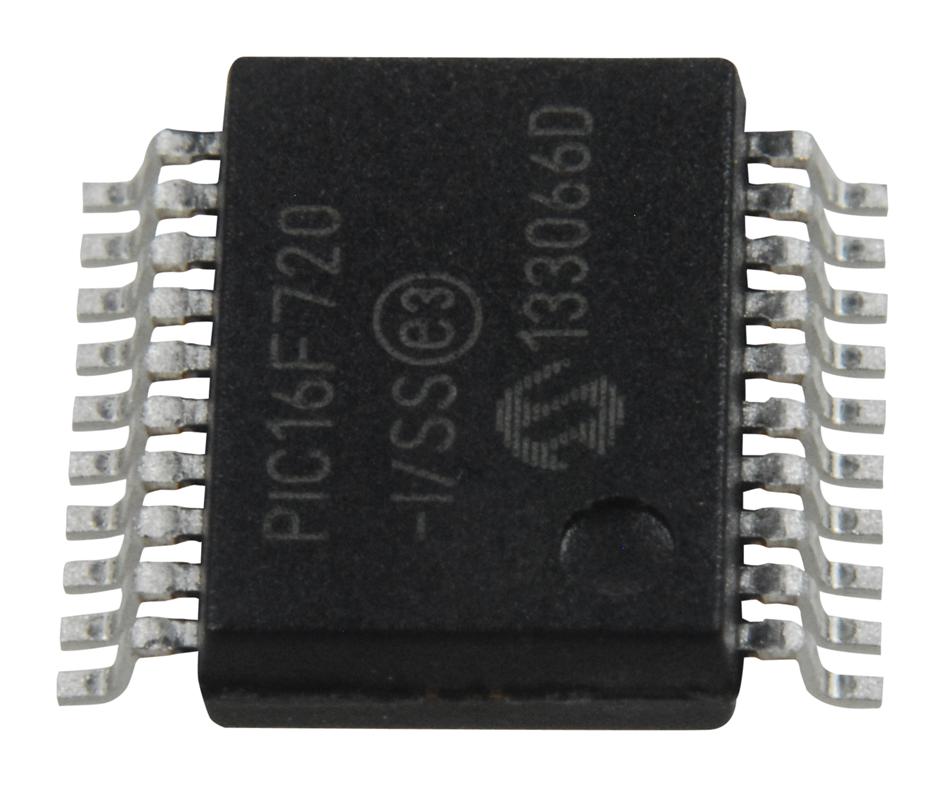
Why Breaking PIC16F720 Firmware Matters
For engineers, manufacturers, and developers, accessing the original firmware from a protected PIC16F720 can be essential for multiple reasons:
- Restoration of lost source code when the original development files are missing.
- Cloning or duplicating embedded systems for hardware remanufacturing.
- Decoding or decrypting encrypted memory for system audits and security testing.
- Unlocking and copying archived data for repair, maintenance, or upgrade of long-life industrial devices.
By extracting the locked program from the device’s flash memory and EEPROM, one can reconstruct the embedded logic, analyze vulnerabilities, or migrate to upgraded platforms without losing critical functionality.
General Steps in Breaking Chip Protection
Although the PIC16F720 employs secured fuse bits and protective lock functions, specialized processes exist to bypass these restrictions. The most common and general steps include:
Verification and duplication – Ensuring the recovered firmware matches the original program and can be safely cloned, copied, or restored to new devices.
Preparation and identification – Recognizing the exact device package and verifying whether protective fuses are enabled.
Disabling security fuses – Using advanced hardware and software tools to bypass or neutralize the lock bits that prevent readout.
Data extraction – Recovering the raw heximal file directly from flash memory or EEPROM.
Disassembly and decoding – Translating the binary archive into human-readable assembly language and, if needed, restoring it toward C/C++ source code for analysis or modification.
The PIC16F/LF720 and PIC16F/LF721 devices are programmed using In-Circuit Serial Programming™ (ICSP™). This programming specification applies to the PIC16F/LF720 and PIC16F/LF721 devices in all packages
With the exception of memory size and the voltage regulator, all other aspects of the PIC16F/LF720 and PIC16F/LF721 devices are identical.
Configuration Words
The PIC16F/LF720 and PIC16F/LF721 have two Configuration Words, Configuration Word 1 (2007h) and Configuration Word 2 (2008h). The individual bits within these Configuration Words are used to enable or disable device functions such as the Brown-out Reset, code protection to prevent MCU Reading and Power-up Timer.
Calibration Words
For the PIC16F/LF720 and PIC16F/LF721 devices, the 16 MHz internal oscillator (INTOSC) and the Brown-out Reset (BOR) are factory calibrated and stored in Calibration Words 1 and 2 (2009h and 200Ah). The Calibration Words do not participate in erase operations. The device can be erased without affecting the Calibration Words.
Unique Features of PIC16F720 and Its Applications
The PIC16F720 microcontroller is valued for its low-power design, integrated peripherals, and efficient instruction set. With on-chip oscillator, multiple I/O ports, ADC capabilities, and flexible timers, it finds applications in:
- Automotive systems such as dashboard modules and engine controllers.
- Industrial automation including motor drives, power supply regulation, and sensor interfaces.
- Consumer devices like home appliances, smart gadgets, and portable instruments.
- Medical electronics requiring compact and reliable embedded solutions.
These widespread uses make the recovery of firmware not only practical but often critical when upgrading or servicing hardware deployed in the field.

Conclusion
The ability to Break Chip PIC16F720 Firmware is an advanced yet vital service for anyone working with protected or encrypted embedded devices. Through carefully executed steps—ranging from cracking locked memory to decoding binary data—users can regain access to program files, flash archives, and source code that would otherwise remain hidden behind protective security measures. This process ensures continuity, supports innovation, and secures long-term control over embedded system design.
 Recover Microcontroller TMS320F2812PGFA Firmware
Recover Microcontroller TMS320F2812PGFA Firmware
The Texas Instruments TMS320F2812PGFA is a powerful digital signal processor (DSP) microcontroller widely used in high-performance industrial and automotive applications. Its ability to handle complex real-time control systems makes it a cornerstone in embedded designs such as motor drives, robotics, power conversion, and automotive electronics. However, with its advanced functionality comes sophisticated security mechanisms, designed to keep its firmware protected from unauthorized access. When the original source code, binary, or heximal file becomes inaccessible due to locked or encrypted flash memory, the need arises to recover microcontroller TMS320F2812PGFA firmware for further analysis, modification, or duplication.
Why Recovery Services Are Needed
There are countless situations where engineers or end users may need to restore or recover the firmware from this secured device. The original program file may be lost, corrupted, or stored in obsolete archives. In other cases, businesses may need to copy or clone the firmware from one protected chip to another for repair, testing, or mass duplication. The protective fuse bits of the TMS320F2812PGFA, once enabled, restrict normal access to the memory, making conventional readout tools ineffective. This creates a need for specialized techniques to unlock or open the device.
Unique Features of the TMS320F2812PGFA
This microcontroller offers unique advantages that make it a preferred choice across industries:
- High-Performance DSP Core: Capable of handling advanced algorithms in real-time.
- Extensive On-Chip Memory: Integrated flash and RAM for storing data, firmware, and critical program files.
- Peripheral Integration: Includes ADCs, communication interfaces, and PWM modules for motor and control systems.
- Security Features: Locking mechanisms and encryption options designed to protect sensitive firmware.
Because of these features, recovering firmware from this chip requires not just basic tools, but deep technical expertise in bypassing secured mechanisms without damaging the device.
General Steps in Breaking Protection
Although exact methods vary depending on chip configuration, the general process for cracking or decoding protected microcontrollers like the TMS320F2812PGFA involves several stages:
- Device Analysis – Identifying the locked memory regions, security fuse states, and encryption measures applied.
- Physical or Logical Access – Applying precision tools to interface with memory and bypass protective barriers.
- Disabling Fuse Bit Protection – Specialized methods are used to neutralize fuse-bit restrictions without corrupting stored data.
- Firmware Extraction – Once unlocked, the heximal firmware is read out from flash, EEPROM, or other memory banks.
- Conversion & Reconstruction – The extracted binary or data file is decoded into a usable format, sometimes decompiled into C/C++ source code for easier analysis.
- Verification & Duplication – The recovered firmware is validated and can be duplicated, copied, or cloned onto new devices as required.
Applications Across Industries
The TMS320F2812PGFA is commonly embedded in:
- Industrial Automation Systems – Robotics, motor drives, and process controllers.
- Automotive Electronics – Engine management, braking, and safety systems.
- Power Systems – Renewable energy inverters, UPS units, and high-efficiency converters.
- Aerospace and Defense – Rugged control systems requiring reliable real-time DSP performance.
In each of these fields, losing access to the embedded firmware could mean costly downtime or inability to restore critical equipment. That is why professional services to recover microcontroller TMS320F2812PGFA firmware are invaluable.
We can Recover Microcontroller TMS320F2812PGFA Firmware, please view below the Microcontroller TMS320F2812PGFA features for your reference:
High-Performance Static CMOS Technology
– 150 MHz (6.67-ns Cycle Time)
– Low-Power (1.8-V Core at 135 MHz, 1.9-V Core at 150 MHz, 3.3-V I/O) Design
· JTAG Boundary Scan Support (1)
· High-Performance 32-Bit CPU ( TMS320C28x™)
– 16 x 16 and 32 x 32 MAC Operations
– 16 x 16 Dual MAC
– Harvard Bus Architecture
– Atomic Operations
– Fast Interrupt Response and Processing
– Unified Memory Programming Model
– 4M Linear Program/Data Address Reach
– Code-Efficient (in C/C++ and Assembly)

– TMS320F24x/LF240x Processor Source Code Compatible to Copy microcontroller
· On-Chip Memory
– Flash Devices: Up to 128K x 16 Flash (Four 8K x 16 and Six 16K x 16 Sectors)
– ROM Devices: Up to 128K x 16 ROM
– 1K x 16 OTP ROM
– L0 and L1: 2 Blocks of 4K x 16 Each Single-Access RAM (SARAM)
– H0: 1 Block of 8K x 16 SARAM
– M0 and M1: 2 Blocks of 1K x 16 Each SARAM
· Boot ROM (4K x 16)
– With Software Boot Modes
– Standard Math Tables
· External Interface (2812)
– Over 1M x 16 Total Memory
– Programmable Wait States
– Programmable Read/Write Strobe Timing
– Three Individual Chip Selects
· Endianness: Little Endian
· Clock and System Control
– Dynamic PLL Ratio Changes Supported
– On-Chip Oscillator
– Watchdog Timer Module
· Three External Interrupts
· Peripheral Interrupt Expansion (PIE) Block That Supports 45 Peripheral Interrupts
· Three 32-Bit CPU-Timers
· 128-Bit Security Key/Lock
– Protects Flash/ROM/OTP and L0/L1 SARAM
– Prevents Firmware Reverse-Engineering
· Motor Control Peripherals
– Two Event Managers (EVA, EVB)
– Compatible to 240xA Devices
· Serial Port Peripherals
– Serial Peripheral Interface (SPI)
– Two Serial Communications Interfaces (SCIs), Standard UART
– Enhanced Controller Area Network (eCAN)
– Multichannel Buffered Serial Port (McBSP)
· 12-Bit ADC, 16 Channels
– 2 x 8 Channel Input Multiplexer
– Two Sample-and-Hold
– Single/Simultaneous Conversions
– Fast Conversion Rate: 80 ns/12.5 MSPS
· Up to 56 General-Purpose I/O (GPIO) Pins
· Advanced Emulation Features
– Analysis and Breakpoint Functions
– Real-Time Debug via Hardware
· Development Tools Include
– ANSI C/C++ Compiler/Assembler/Linker
– Code Composer Studio™ IDE
– DSP/BIOS™
– JTAG Scan Controllers(1)
· Low-Power Modes and Power Savings
– IDLE, STANDBY, HALT Modes Supported
– Disable Individual Peripheral Clocks
Recovering protected or encrypted firmware from the TMS320F2812PGFA requires advanced expertise, precise methods, and an understanding of both hardware and software security. By applying proven techniques to crack locked memory, decode binary data, and unlock encrypted program files, it becomes possible to restore the original firmware and duplicate it for practical applications. This ensures that valuable embedded systems continue to operate efficiently, while also allowing engineers to analyze and improve upon existing designs.
 Recover MCU dsPIC30F6013A30IP Firmware
Recover MCU dsPIC30F6013A30IP Firmware
The Microchip dsPIC30F6013A is a powerful 16-bit Digital Signal Controller (DSC) widely adopted in industrial automation, automotive systems, medical devices, and high-performance embedded applications. Its combination of digital signal processing with traditional microcontroller capabilities makes it a popular choice for engineers who require real-time control and reliability. However, the very features that make this chip valuable—such as its protective lock bits, secured program memory, and encrypted data storage—also create challenges when users need to access or recover MCU dsPIC30F6013A firmware.
Why Firmware Recovery Matters
Firmware serves as the heart of any embedded design. The binary or heximal files stored in the flash, EEPROM, and other memory regions control every operation of the system. When this firmware becomes corrupted, locked, or otherwise inaccessible, the entire device may be unusable. Being able to restore, copy, or duplicate the original program file is essential for maintenance, legacy support, or further development.
In many cases, manufacturers activate fuse bits to prevent outsiders from reading the firmware. While these security measures help protect intellectual property, they can also create difficulties for end users who legitimately need access to their own firmware. Our specialized service focuses on overcoming these barriers and providing a reliable path to recover the required data.
General Steps to Unlock Protected Firmware
Recovering dsPIC30F6013A firmware often involves several stages:
- Initial Device Analysis – Inspecting the target chip, identifying the security status, and verifying the condition of the flash and EEPROM.
- Bypassing Protection – Techniques to disable fuse bits or bypass secured configurations, allowing access to the locked memory.
- Data Extraction – Reading out the binary or heximal archive from the program memory and EEPROM.
- Disassembly and Conversion – When needed, decoding or decompiling the binary file into more understandable forms such as assembly or partial source code.
- Validation and Restoration – Ensuring that the recovered file is accurate, functional, and ready for reprogramming into new devices or used for analysis.
These steps may require advanced tools and a combination of hardware probing, cryptographic decode/decrypt methods, and firmware hacking strategies.
Applications of dsPIC30F6013A
The dsPIC30F6013A is widely used in:
- Automotive systems – engine control, sensor interfaces, and powertrain modules.
- Industrial automation – motor control, real-time monitoring, and robotics.
- Medical equipment – secured embedded devices for patient monitoring and diagnostics.
- Consumer electronics – high-efficiency devices where digital signal processing is critical.
In each case, the ability to unlock, open, or recover the firmware ensures product longevity, supports upgrades, and enables manufacturers or end users to duplicate or redevelop systems without losing functionality.
We can Recover MCU dsPIC30F6013A30IP Firmware, please view below MCU DSPIC30F6013A30IP features for your reference:
The dsPIC30F family of DSCs contains a region of on-chip memory used to simplify device programming. This region of memory can store a programming executive, which allows the dsPIC30F to be programmed faster than the traditional means. Once the programming executive is stored to memory by an external programmer (such as Microchip’s MPLAB ICD 2, MPLAB PM3, PRO MATE® II, or MPLAB REAL uses control codes to serially execute instructions on the dsPIC30F device.
This specification describes the ICSP and Enhanced ICSP programming methods. Section 3.0 “Programming Executive Application” describes the programming executive application and Section 5.0 “Device Programming” describes its application programmer’s interface for the host programmer before Recover MCU. Section 11.0 “ICSP™ Mode” describes the ICSP programming method. ICE™), it can then interact with the external programmer to efficiently program devices.

2.1 Hardware Requirements
The programmer and programming executive have a master-slave relationship, where the programmer is the master programming device and the programming executive is the slave.
Circuit Engineering Company Limited continues to be recognized as the Southern China Leader in Services for IC Break, MCU attack, MCU Recover, Microcontroller Copy service. With the advancement of today’s modern circuit board technology, it is more important than ever to have specialists available to help you at a moment’s notice. Our engineering and commercial teams collectively have a vast amount of electronic experience covering field include Consumer Electronics, Industrial Automation Electronics, Wireless Communication Electronics., etc. For more information please contact us through email.
Recovering MCU dsPIC30F6013A firmware is a complex process that requires expertise in reverse engineering, cryptographic bypass, and secure memory handling. By extracting and restoring the protected program and data files from this versatile microcontroller, it becomes possible to extend the life of valuable embedded systems, replicate critical functions, or simply safeguard against data loss. For industries relying on the dsPIC30F6013A, having the ability to recover its firmware can be the key to maintaining competitiveness and ensuring continued operation of vital equipment.

 Break IC SST89E58RD2A Software
Break IC SST89E58RD2A Software
The SST89E58RD2A is a high-performance, 8051-based microcontroller that is widely used in industrial control systems, automotive electronics, communication devices, consumer products, and other embedded applications. It integrates on-chip flash memory and EEPROM, enabling flexible firmware updates. In many deployments, the chip’s program memory is protected, with security fuse bits set to prevent reading or copying. These protections safeguard the intellectual property within the device but also pose challenges when legitimate access is required.

The ability to Break IC SST89E58RD2A Software is essential in scenarios such as equipment repair, legacy system recovery, or upgrading customized firmware when the original source is lost. Through advanced crack, hack, decode, and decrypt techniques, it is possible to recover the binary or heximal file stored in the microcontroller’s memory. Once retrieved, the data can be restored, copied, cloned, or duplicated for further analysis or reprogramming.
Common Applications of the SST89E58RD2A
This microcontroller’s robust design makes it suitable for:
- Industrial automation controllers
- Telecommunication systems
- Automotive modules
- Security systems
- Consumer electronics and instrumentation
Its unique features include In-System Programming (ISP), high endurance flash, embedded EEPROM for parameter storage, and configurable I/O ports—making it both versatile and reliable for long-term use.

General Steps in Breaking Protection and Recovering Data
While the specific technical details remain confidential, the general process for unlocking or opening the chip involves:
- Identification – Verifying the exact chip model, package type, and security configuration.
- Interface Preparation – Establishing a reliable hardware connection to the chip’s programming pins or test pads.
- Security Analysis – Determining the presence of fuse bits, encrypted program storage, or other protective measures.
- Protection Bypass – Applying specialized procedures to disable or circumvent security bits while preserving the integrity of stored program data.
- Data Extraction – Reading the firmware, flash, or EEPROM content in binary or heximal format.
- Post-Processing – Decoding, verifying, and formatting the recovered file, archive, or source code for usability.
These steps require precise hardware tools, custom software utilities, and experience in embedded reverse engineering to avoid damaging the chip or corrupting the data.
Benefits of Recovering SST89E58RD2A Firmware
Gaining access to a protected SST89E58RD2A allows for:
- Restoring lost program files for legacy systems
- Debugging or modifying embedded functions
- Cloning or duplicating existing control boards for manufacturing continuity
- Migrating firmware to upgraded hardware platforms
- Performing in-depth security audits or performance optimization.
The process to Break IC SST89E58RD2A Software is a specialized service that blends hardware-level expertise with deep knowledge of embedded microcontroller architecture. By carefully bypassing security and recovering protected firmware, users regain control over their systems, ensuring continued operation, adaptability, and long-term maintainability—without compromising system stability.
We can Break IC SST89E58RD2A Software, below please find the IC SST89E58RD2A features for your reference:
SST89E/V58 / 54 / 52RD2/RD FlashFlex51 MCU
Preliminary FEATURES:
· 8-bit 8051-Compatible Microcontroller (MCU)
· Ten Interrupt Sources at 4 Priority with Embedded SuperFlash Memory to Clone IC
– Four External Interrupt Inputs
– Fully Software Compatible
· Programmable Watchdog Timer
– Development Toolset Compatible
· Programmable Counter Array (PCA)
– Pin-For-Pin Package Compatible
· Four 8-bit I/O Ports (32 I/O Pins)
· SST89E5xRD2 Operation
One 4-bit Port
– 0 to 40 MHz at 5V
· Second DPTR register
· SST89V5xRD2 Operation
· Low EMI Mode (Inhibit ALE)
– 0 to 33 MHz at 3V
· SPI Serial Interface
· 1 KByte Internal RAM
· Standard 12 Clocks per cycle
· Dual Block SuperFlash EEPROM option to double the speed to 6
– 8/16/32 KByte primary block +
· TTL- and CMOS-Compatible Logic 8 KByte secondary block
· Brown-out Detection (128-Byte sector size for both blocks)
· Low Power Modes
– Individual Block Security Lock with SoftLock
– Concurrent Operation during
– Power-down Mode with External In-Application Programming (IAP)
– Idle Mode
– Memory Overlay for Interrupt Support during IAP
· Temperature Ranges:
· Support External Address Range up to 64
– Commercial (0°C to +70°C) KByte of Program and Data Memory
– Industrial (-40°C to +85°C)
· Three High-Current Drive Ports (16 mA each)
· Packages Available
· Three 16-bit Timers/Counters
– 44-lead PLCC
· Full-Duplex, Enhanced UART
– 40-pin PDIP (Port 4 feature
– 44-lead TQFP
– Framing Error Detection
– Automatic Address Recognition
· All non-Pb (lead-free) devices

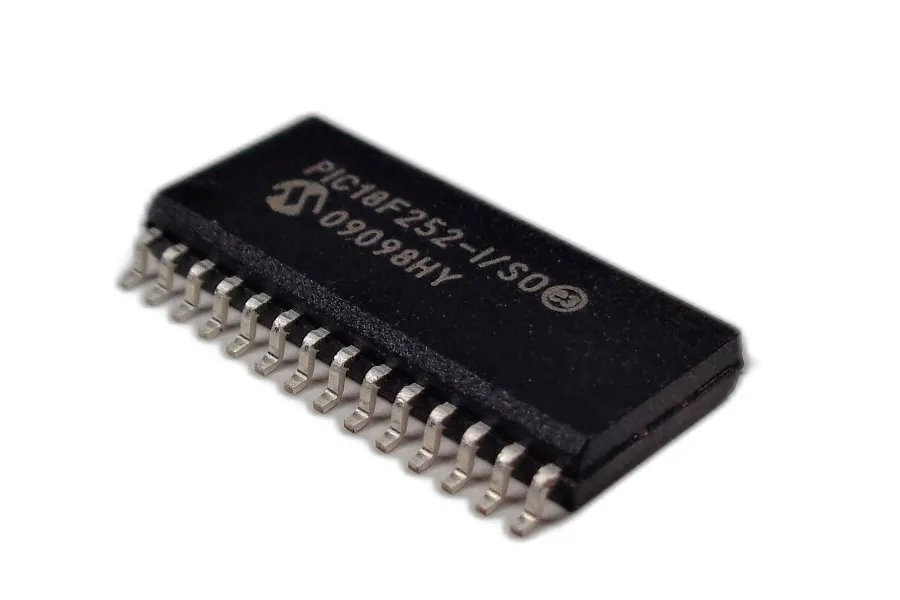
 Copy Chip PIC18F252 Flash
Copy Chip PIC18F252 Flash
In the realm of industrial control, automotive modules, and smart devices, the Microchip PIC18F252 microcontroller is a widely adopted solution, prized for its performance and reliability. However, when dealing with protected or locked firmware, retrieving the critical binary, flash, or EEPROM data stored inside becomes a technical challenge. At [Your Company Name], we offer expert Copy Chip PIC18F252 Flash services — helping clients clone, duplicate, or restore the essential program data from this secured embedded microcontroller.

About the PIC18F252 Microcontroller
The PIC18F252 is an 8-bit MCU from Microchip featuring 32 KB of flash memory, 1.5 KB of RAM, and 256 bytes of EEPROM. With a built-in 10-bit ADC, a high-speed 8 MHz internal oscillator, and multiple serial communication interfaces, it is ideal for automotive applications, industrial automation, instrumentation, and home appliances. What makes it particularly popular is its balance of performance and simplicity, along with robust code protection features that aim to block unauthorized access to its internal firmware.
Overcoming Firmware Security Measures
Unfortunately, such encrypted or protected memory blocks the user from reading or editing the existing firmware, even for legitimate purposes like troubleshooting, system updates, or legacy equipment repair. Our Copy Chip PIC18F252 Flash service is designed to help recover this locked binary, even if code protection or readout lock bits have been enabled.

Our engineers apply specialized decoding, decryption, and reverse engineering methods to carefully open, crack, and copy the data without damaging the chip. We can help you retrieve not just the main flash, but also related memory blocks including EEPROM and configuration words — allowing you to fully duplicate the system onto another chip or examine the code in a heximal or source code format.
From Chip to File: Firmware Recovery and Restoration
With our service, you will receive the extracted firmware file, typically in .hex, .bin, or other industry-compatible formats, depending on your requirements. If requested, we can also assist in converting it into assembly or attempt C-like source code reconstruction for further editing or analysis.
Supporting Older Devices: PIC16F57 Flash and Hex Recovery
Beyond PIC18F252, we also support heximal file recovery from older or legacy Microchip MCUs such as PIC16F57, which often lack modern debugging interfaces. For legacy systems, we can help you recover lost or undocumented firmware that is crucial for continued operation or hardware upgrades.
Why Clients Trust Us
- Confidentiality and security in all projects
- Deep technical experience with Microchip architectures
- Custom recovery strategies based on your end application
- Ability to handle secured, encrypted, and obfuscated firmware
- Option to duplicate, replicate, or restore the firmware onto replacement hardware
Applications and Use Cases

This service is ideal for clients in industries such as automotive ECU repair, industrial control board restoration, reverse engineering for obsolete parts, program recovery, and quality inspection of embedded designs.
We can Copy Chip PIC18F252 Flash, please view below Chip PIC18F252 features for your reference:
Power Management Features:
Run: CPU on, Peripherals on
Idle: CPU off, Peripherals on
Sleep: CPU off, Peripherals off
Ultra Low 50nA Input Leakage
Run mode Currents Down to 11 ìA Typical
Idle mode Currents Down to 2.5 ìA Typical
Sleep mode Current Down to 100 nA Typical
Timer1 Oscillator: 900 nA, 32 kHz, 2V
Watchdog Timer: 1.4 ìA, 2V Typical
Two-Speed Oscillator Start-up
· Master Synchronous Serial Port (MSSP) module
Master and Slave modes
· Enhanced Addressable USART module:
– Supports RS-485, RS-232 and LIN/J2602
– RS-232 operation using internal oscillator
block (no external crystal required)
– Auto-wake-up on Start bit
– Auto-Baud Detect
· 10-Bit, up to 13-Channel Analog-to-Digital (A/D)
Flexible Oscillator Structure:
· Four Crystal modes, up to 40 MHz
· 4x Phase Lock Loop (PLL) – Available for Crystal
and Internal Oscillators
· Two External RC modes, up to 4 MHz
· Two External Clock modes, up to 40 MHz
· Internal Oscillator Block:
– Fast wake from Sleep and Idle, 1 ìs typical
– 8 use-selectable frequencies, from 31 kHz to 8 MHz
– Provides a complete range of clock speeds
from 31 kHz to 32 MHz when used with PLL
– User-tunable to compensate for frequency drift
· Secondary Oscillator using Timer1 @ 32 kHz
· Fail-Safe Clock Monitor:
– Allows for safe shutdown if peripheral clock stops
Peripheral Highlights:
Converter module:
– Auto-acquisition capability
– Conversion available during Sleep
· Dual Analog Comparators with Input Multiplexing
· Programmable 16-Level High/Low-Voltage
Detection (HLVD) module:
– Supports interrupt on High/Low-Voltage Detection
Special Microcontroller Features:
· C Compiler Optimized Architecture:
– Optional extended instruction set designed to optimize re-entrant code
· 100,000 Erase/Write Cycle Enhanced Flash
Program Memory Typical
· 1,000,000 Erase/Write Cycle Data EEPROM
Memory Typical
· Flash/Data EEPROM Retention: 100 Years Typical which is important for IC Extraction
· Self-Programmable under Software Control
High-Current Sink/Source 25 mA/25 mA
Three Programmable External Interrupts
Four Input Change Interrupts
Up to 2 Capture/Compare/PWM (CCP) modules,
· Priority Levels for Interrupts
· 8 x 8 Single-Cycle Hardware Multiplier
· Extended Watchdog Timer (WDT):
– Programmable period from 4 ms to 131s
one with Auto-Shutdown (28-pin devices)
· Enhanced Capture/Compare/PWM (ECCP)
module (40/44-pin devices only):
– One, two or four PWM outputs
– Selectable polarity
– Programmable dead time
– Auto-shutdown and auto-restart
· Single-Supply 5V In-Circuit Serial
Programming™ (ICSP™) via Two Pins
· In-Circuit Debug (ICD) via Two Pins
· Wide Operating Voltage Range: 2.0V to 5.5V
· Programmable Brown-out Reset (BOR) with
Software Enable Option
If you’re working with a locked PIC18F252 or struggling to retrieve the firmware from an old PIC16F57, contact CIRCUIT ENGINEERING CO., LTD today. With our Copy Chip PIC18F252 Flash service, we help you recover, clone, and understand your embedded system like never before — securely, accurately, and efficiently.
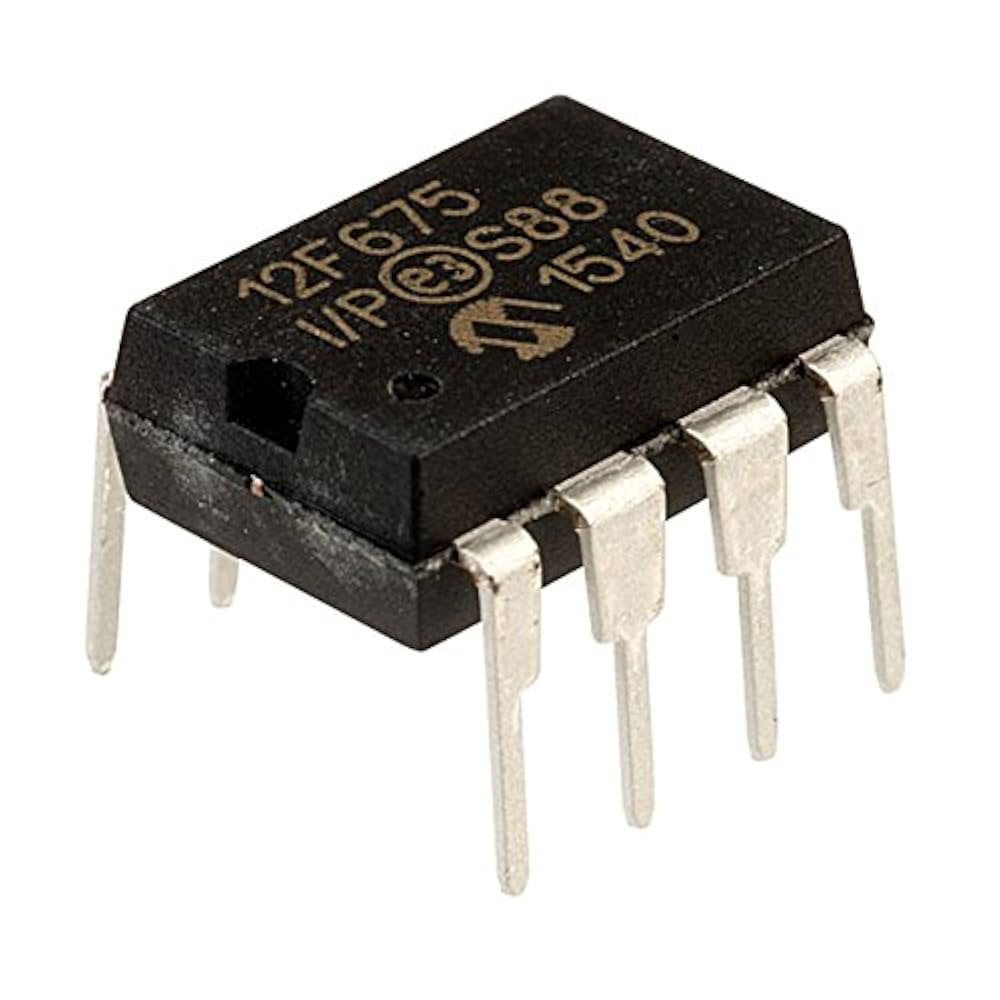
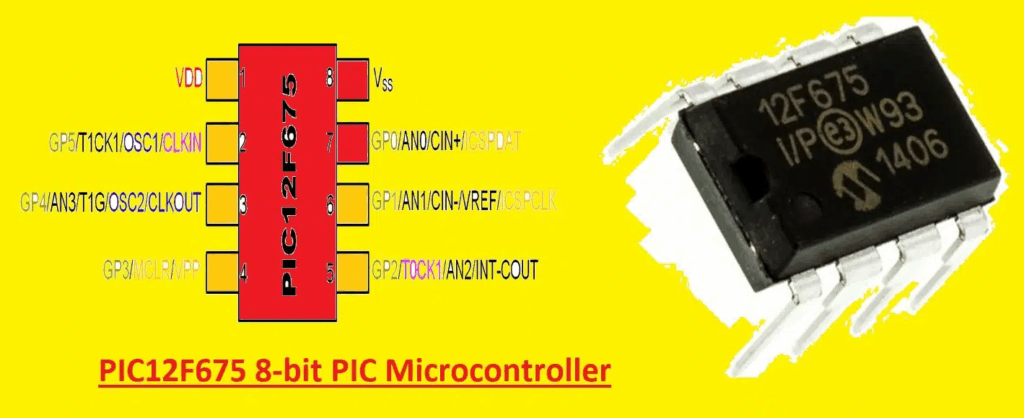
 Copy Microcontroller PIC12F675 Firmware
Copy Microcontroller PIC12F675 Firmware
Microchip’s PIC12F675 is a compact yet powerful 8-bit microcontroller commonly used in embedded control systems, industrial automation, smart sensors, and consumer electronics. With integrated features like internal oscillators, analog comparators, and EEPROM memory, this protected microcontroller is favored for its efficiency and versatility. However, its secured architecture and locked memory regions often pose significant challenges for those needing access to the original firmware for analysis, restoration, or duplication.

At CIRCUIT ENGINEERING CO., LTD, we specialize in Copy Microcontroller PIC12F675 Firmware services, offering reliable support for clients who need to clone, duplicate, or restore the original code stored in these encrypted or protected devices.
Unlocking Locked Firmware with Advanced Reverse Engineering
The firmware stored in a secured microcontroller like the PIC12F675 is often locked or encrypted by design to prevent unauthorized duplication or reverse engineering. However, legitimate needs arise in various industries where end-users or system integrators require access to the original binary, heximal, or source code for system upgrades, repairs, or compatibility testing.
Using advanced hardware interfacing tools and firmware analysis techniques, our team can crack, decode, or decrypt the content stored in the PIC12F675’s flash, EEPROM, or internal memory. We help clients unlock access to the full firmware archive, extracting the program file and converting it to a usable heximal or source code format.
Specialized Support for PIC16F57 Hex File Recovery
In addition to the PIC12F675, we also offer heximal file recovery services for older or legacy microcontrollers such as the Microchip PIC16F57. This 28-pin, baseline PIC MCU, while limited in features compared to newer devices, is still found in legacy control systems, power modules, and older-generation automation circuits.
Our service allows users to open, read, and restore the firmware from PIC16F57 devices that are either obsolete or inaccessible due to missing documentation or locked protection bits. We reconstruct and export the program memory to a usable binary or hex file, preserving system functionality and preventing costly replacements or redesigns.
Applications of the PIC12F675
The Microchip PIC12F675 is widely deployed across a range of applications due to its compact size and powerful core. Typical uses include:
- Sensor interface and signal conditioning
- Home automation controllers
- Battery-powered devices
- Temperature or light sensing modules
- Motor speed and direction control
It features a 10-bit ADC, internal 4 MHz oscillator, and up to 1KB of flash memory, making it an ideal choice for low-cost and space-constrained embedded designs.
Why Choose Our Firmware Copy Service?
- Experience with Secured Devices: We handle both old and new Microchip MCUs, even those with advanced protection.
- Accurate Code Extraction: We ensure high-fidelity firmware extraction to support debugging, compatibility, or replacement.
- Confidential & Secure: All customer data and extracted files are kept confidential with strict handling protocols.
- Custom Output Options: We deliver the recovered firmware in formats including binary, hex, or C-source equivalents when needed.
We can Copy Microcontroller PIC12F675 Firmware, please view below Microcontroller PIC12F675 features for your reference:
High-Performance RISC CPU:
· Only 35 Instructions to Learn
– All single-cycle instructions except branches
· Operating Speed:
– DC – 20 MHz oscillator/clock input
– DC – 200 ns instruction cycle
· Interrupt Capability
· 8-Level Deep Hardware Stack
· Direct, Indirect, and Relative Addressing modes
Special Microcontroller Features:
· Internal and External Oscillator Options
– Precision Internal 4 MHz oscillator factory calibrated to ±1%
– External Oscillator support for crystals and resonators
– 5 ms wake-up from Sleep, 3.0V, typical
· Power-Saving Sleep mode
· Wide Operating Voltage Range – 2.0V to 5.5V
· Industrial and Extended Temperature Range
· Low-Power Power-on Reset (POR)
· Power-up Timer (PWRT) and Oscillator Start-up Timer (OST)
· Brown-out Detect (BOD)
· Watchdog Timer (WDT) with Independent
Oscillator for Reliable Operation
· Multiplexed MCLR/Input Pin
· Interrupt-on-Pin Change
· Individual Programmable Weak Pull-ups
· Programmable Code Protection
· High Endurance Flash/EEPROM Cell
– 100,000 write Flash endurance
– 1,000,000 write EEPROM endurance
– Flash/Data EEPROM Retention: > 40 years
Low-Power Features:
· Standby Current:
– 1 nA @ 2.0V, typical
· Operating Current:
– 8.5 mA @ 32 kHz, 2.0V, typical
– 100 mA @ 1 MHz, 2.0V, typical
· Watchdog Timer Current
– 300 nA @ 2.0V, typical
· Timer1 Oscillator Current:
– 4 mA @ 32 kHz, 2.0V, typical
Peripheral Features:
· 6 I/O Pins with Individual Direction Control
· High Current Sink/Source for Direct LED Drive
· Analog Comparator module with:
– One analog comparator
– Programmable on-chip comparator voltage reference (CVREF) module
– Programmable input multiplexing from device inputs
– Comparator output is externally accessible to Read MCU
· Analog-to-Digital Converter module (PIC12F675):
– 10-bit resolution
– Programmable 4-channel input
– Voltage reference input
· Timer0: 8-Bit Timer/Counter with 8-Bit Programmable Prescaler
· Enhanced Timer1:
– 16-bit timer/counter with prescaler
– External Gate Input mode
– Option to use OSC1 and OSC2 in LP mode as Timer1 oscillator, if INTOSC mode selected
· In-Circuit Serial ProgrammingTM (ICSPTM) via two pins
If you’re struggling with a locked, protected, or obsolete PIC microcontroller and need to copy, clone, or restore its original firmware, our expert team is ready to assist. With our Copy Microcontroller PIC12F675 Firmware service and specialized knowledge in hex file recovery for legacy chips like PIC16F57, we help you regain full control over your embedded applications. Contact us to learn more and begin your firmware recovery journey.