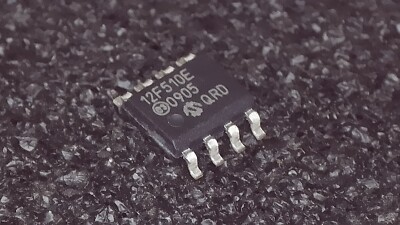
Attack IC PIC12F510 Program
Attack IC PIC12F510 Program
Electronic systems built around the Microchip PIC12F510 microcontroller continue to operate in industrial equipment, compact control modules, consumer electronics, sensor hardware, and smart automation devices worldwide. As these systems mature, owners frequently discover that the internal program, calibration data, or eeprom configuration cannot be accessed due to encrypted, protected, or fully locked security settings. Our advanced service, operating under the subject Attack IC PIC12F510 Program, is designed to assist legitimate system owners with retrieving and safeguarding valuable firmware from this device when no alternative documentation or original source code exists.
We can Attack IC PIC12F510 Program, please view the IC PIC12F510 features for your reference:
High-Performance RISC CPU:
· Only 33 single-word instructions to learn
· All single-cycle instructions except for program branches, which are two-cycle
· 12-bit wide instructions
· 2-level deep hardware stack
· Direct, Indirect and Relative Addressing modes for data and instructions
· 8-bit wide data path
Why PIC12F510 Matters in Modern and Legacy Systems
The PIC12F510 is a compact and highly efficient embedded microcontroller with an 8-bit architecture, onboard oscillator, and dedicated flash storage. Despite its small footprint, it supports a wide range of automation and control functions. It is widely deployed in:

- Smart sensors and IoT-style low-power modules
- Consumer electronic controllers and accessories
- Industrial interface boards and portable tools
- Compact robotics, power drivers, and lighting products
- Entry-level programmable devices used in educational engineering
Manufacturers often rely on custom-developed logic stored within the internal binary or heximal image, making the internal archive extremely valuable.
· 10 Special Function Hardware registers (PIC12F510)
· 13 Special Function Hardware registers (PIC16F506)
· Operating speed:
– DC – 8 MHz Crystal Oscillator (PIC12F510)
– DC – 500 ns instruction cycle (PIC12F510)
– DC – 20 MHz Crystal Oscillator (PIC16F506)
– DC – 200 ns instruction cycle (PIC16F506)
Special Microcontroller Features:

· 4 or 8 MHz selectable precision internal oscillator
– Factory calibrated to ±1%
· In-Circuit Serial Programming™ (ICSP™)
· In-Circuit Debugging (ICD) support
· Power-on Reset (POR)
· Device Reset Timer (DRT):
– Short DRT (1.125 ms, typical) for INTOSC, EXTRC and EC
– DRT (18 ms, typical) for HS, XT and LP
· Watchdog Timer (WDT) with dedicated on-chip RC oscillator for reliable operation
· Programmable code protection
· Multiplexed MCLR input pin
What Our Service Provides
Our role is to assist organizations or authorized owners who need to break through inaccessible security layers and safely extract the embedded file containing the functional logic of the device. We provide a full solution covering:
- Controlled evaluation of chip condition and security level
- Secure retrieve, clone, or duplicate memory output for approved clients
- Preservation of internal program and calibration memory
- Reconstruction of missing engineering documentation for long-term maintenance
While some cases require advanced measurement or optional decapsulation, we never disclose technical methodology. Our focus is on compliance, confidentiality, and precision—not teaching users how to hack or decode hardware protections on their own.
· Selectable internal weak pull-ups on I/O pins
· Power-Saving Sleep mode
· Wake-up from Sleep on pin change
· Wake-up from Sleep on comparator change
· Selectable oscillator options:
– INTOSC: 4/8 MHz precision Internal oscillator
– EXTRC: External low-cost RC oscillator
– XT: Standard crystal/resonator
– LP: Power-saving, low-frequency crystal
– HS: High-speed crystal/resonator (PIC16F506 only)
– EC: High-speed external clock input (PIC16F506 only)
· Analog-to-Digital (A/D) Converter:
– 8-bit resolution
General Recovery Approach (Non-Technical and Safe)
Each PIC12F510 is assessed based on its configuration state, environmental condition, and secured parameters. Once feasibility is confirmed, controlled extraction operations are performed to recover the internal firmware in a stable and verifiable format. After recovery, clients receive a clean binary or heximal memory image suitable for redevelopment, migration, or duplication into new hardware.

– 4-input channels (1 channel is dedicated to conversion of the internal 0.6V absolute voltage reference)
· High current sink/source for direct LED drive
· 8-bit real-time clock/counter (TMR0) with 8-bit programmable prescaler
Low-Power Features/CMOS Technology:
· Operating Current:
– < 170 ìA @ 2V, 4 MHz
· Standby Current:
– 100 nA @ 2V, typical
· Low-power, high-speed Flash technology:
– 100,000 cycle Flash endurance
– > 40-year retention
· Fully static design
· Wide operating voltage range: 2.0V to 5.5V
· Wide temperature range:
– Industrial: -40°C to +85°C
– Extended: -40°C to +125°C
Peripheral Features (PIC12F510):
· 6 I/O pins:
– 5 I/O pins with individual direction control
– 1 input only pin
· 1 Analog Comparator with absolute reference
Peripheral Features (PIC16F506):
· 12 I/O pins:
– 11 I/O pins with individual direction control
– 1 input only pin
· 2 Analog Comparators with absolute reference and programmable reference .
8-bit resolution
– 4-input channels (1 channel is dedicated to conversion of the internal 0.6V absolute voltage reference)
· High current sink/source for direct LED drive
· 8-bit real-time clock/counter (TMR0) with 8-bit programmable prescaler
Low-Power Features/CMOS Technology:
· Operating Current:
– < 170 ìA @ 2V, 4 MHz
· Standby Current:
– 100 nA @ 2V, typical
· Low-power, high-speed Flash technology:
– 100,000 cycle Flash endurance
– > 40-year retention
· Fully static design
· Wide operating voltage range: 2.0V to 5.5V
· Wide temperature range:
– Industrial: -40°C to +85°C
– Extended: -40°C to +125°C
Benefits to the End User
Clients choose this service because it allows them to:
- Continue production when the original developer or supplier is unavailable
- Protect operational investments tied to legacy microcontroller platforms
- Avoid rewriting devices from scratch due to lost source code
- Maintain or redesign systems without unknown programming risks
- Build a controlled archive for future engineering and servicing
This ensures long-term sustainability, reduced operational cost, and business continuity.
 Attack IC PIC16F54 Eeprom
Attack IC PIC16F54 Eeprom
We can attack IC PIC16F54 Eeprom, please view the IC PIC16F54 features for your reference:
High-Performance RISC CPU:
· Only 33 single-word instructions to learn
· All instructions are single cycle except for program branches which are two-cycle
· Two-level deep hardware stack
· Direct, Indirect and Relative Addressing modes for data and instructions
· Operating speed:
– DC – 20 MHz clock speed
– DC – 200 ns instruction cycle time
· On-ic Flash program memory:
– 512 x 12 on PIC16F54
– 2048 x 12 on PIC16F57
– 2048 x 12 on PIC16F59
· General Purpose Registers (SRAM)
– 25 x 8 on PIC16F54
– 72 x 8 on PIC16F57
– 134 x 8 on PIC16F59
Special Microcontroller Features:
· Power-on Reset (POR)
· Device Reset Timer (DRT)
· Watchdog Timer (WDT) with its own on-ic RC oscillator for reliable operation
· Programmable Code Protection to prevent Microcontroller unlocking
· Power-Saving Sleep mode
· In-Circuit Serial Programming™ (ICSP™)
· Selectable oscillator options:
– RC: Low-cost RC oscillator
– XT: Standard crystal/resonator
– HS: High-speed crystal/resonator
– LP: Power-saving, low-frequency crystal
· Packages:
– 18-pin PDIP and SOIC for PIC16F54
– 20-pin SSOP for PIC16F54
– 28-pin PDIP, SOIC and SSOP for PIC16F57
– 40-pin PDIP for PIC16F59
– 44-pin TQFP for PIC16F59
Low-Power Features:
· Operating Current:
– 170 ìA @ 2V, 4 MHz, typical
– 15 ìA @ 2V, 32 kHz, typical
· Standby Current:
– 500 nA @ 2V, typical
Peripheral Features:
· 12/20/32 I/O pins:
– Individual direction control
– High current source/sink
· 8-bit real-time clock/counter (TMR0) with 8-bit programmable prescaler
CMOS Technology:
· Wide operating voltage range:
– Industrial: 2.0V to 5.5V
– Extended: 2.0V to 5.5V
· Wide temperature range:
– Industrial: -40°C to 85°C
– Extended: -40°C to 125°C
· High-endurance Flash:
– 100K write/erase cycles
– > 40-year retention
 Break Chip PIC16F59 Eeprom
Break Chip PIC16F59 Eeprom
Modern industrial systems rely heavily on stable low-power microcontrollers, and the Microchip PIC16F59 remains a popular choice in manufacturing, appliance control, compact automation modules, and a wide range of embedded designs. As equipment ages, owners often face difficulties accessing the eeprom, flash, and internal memory due to protected, locked, or encrypted configurations. Our high-end service, introduced under the subject Break Chip PIC16F59 EEPROM, is designed to help legitimate clients safely retrieve operational data, program logic, and legacy firmware without exposing any attack techniques.

The high performance of the PIC16F5X family can be attributed to a number of architectural features commonly found in RISC microprocessors to Break Chip PIC16F59 Eeprom. To begin with, the PIC16F5X uses a Harvard architecture in which program and data are accessed on separate buses.
Industry Use Cases & Unique Features of PIC16F59
The PIC16F59 is widely used because of its flexible architecture, low power consumption, and stable embedded design. You will find it in:
- Household electronic controllers
- Industrial signal modules and measurement devices
- Educational hardware, training boards, and simple robotics
- Automotive auxiliary electronics
- Consumer and semi-industrial automation tools
Its internal 12-bit core, versatile I/O structure, and reliable eeprom storage make it a long-term favorite among OEMs. Many manufacturers build custom logic inside this device, making the stored binary or heximal archive extremely valuable to business continuity.
This improves bandwidth over traditional von Neumann architecture where program and data are fetched on the same bus. Separating program and data memory further allows instructions to be sized differently than the 8-bit wide data word. Instruction opcodes are 12-bits wide, making it possible to have all single-word instructions. A 12-bit wide program memory access bus fetches a 12-bit instruction in a single cycle.
A two-stage pipeline overlaps fetch and execution of instructions. Consequently, all instructions (33) execute in a single cycle except for program branches. The PIC16F54 addresses 512 x 12 of program memory, the PIC16F57 and PIC16F59 addresses 2048 x 12 of program memory. All program memory is internal.
The PIC16F5X can directly or indirectly address its register files and data memory. All Special Function Registers (SFR), including the program counter, are mapped in the data memory. The PIC16F5X has a highly orthogonal (symmetrical) instruction set that makes it possible to carry out any operation on any register using any Addressing mode when Break Chip PIC16F59 Eeprom. This symmetrical nature and lack of ‘special optimal situations’ make programming with the PIC16F5X simple, yet efficient. In addition, the learning curve is reduced significantly.

The PIC16F5X device contains an 8-bit ALU and working register. The ALU is a general purpose arithmetic unit. It performs arithmetic and Boolean functions between data in the working register and any register file.
What Our Service Provides
Our service assists authorized device owners who need to break through inaccessible flash or eeprom regions due to forgotten revisions, discontinued suppliers, or lost source code. We support scenarios where systems must continue running for many years, but the original file or firmware is no longer obtainable.
We help legitimate clients:
- Retrieve the internal program and operational data
- Clone or duplicate their existing unit for maintenance or redesign
- Rebuild missing archive records for long-term service
- Recover critical logic damaged by aging components
Although some devices require inspection or controlled decapsulation, we do not disclose any internal processes. The goal is always to return a verified, functional binary or heximal image of your own property.
The ALU is 8-bits wide and capable of addition, subtraction, shift and logical operations. Unless otherwise mentioned, arithmetic operations are two’s complement in nature. In two-operand instructions, typically one operand is the W (working) register. The other operand is either a file register or an immediate constant. In single operand instructions, the operand is either the W register or a file register.

General High-Level Recovery Concept (Non-technical & Safe)
The process begins with a feasibility assessment based on device condition, level of secured configuration, and memory integrity. Some units require physical stabilization or deeper evaluation, while others can be processed through standardized extraction workflows designed to respect IP ownership, legal compliance, and data confidentiality.
Our team does not “teach” customers how to hack, decode, or attack the security. Instead, we perform all procedures internally and return only the final, usable file.
Purpose & Benefits for End Users
Clients choose this service because it helps them:
- Keep old machinery running without redesign
- Preserve unique source code and calibration data
- Extend the life cycle of products reliant on PIC16F59
- Avoid costly downtime caused by lost or inaccessible firmware
- Ensure a secure, company-controlled archive for future engineering
By providing a complete and validated memory image, we enable stable maintenance, redesign, or modernization.
Typical Challenges We Encounter
Recovery of PIC16F59 may involve:
- Heavily protected or embedded firmware regions
- Partial memory decay or corruption
- Environmental wear or physical damage
- Complex security configurations depending on revision
Despite these difficulties, our methodical workflow and advanced evaluation tools help ensure high success rates under legally authorized conditions.
The W register is an 8-bit working register used for ALU operations. It is not an addressable register. Depending on the instruction executed, the ALU may affect the values of the Carry (C), Digit Carry (DC) and Zero (Z) bits in the STATUS Register to Extract IC code. The C and DC bits operate as a borrow and digit borrow out bit, respectively, in subtraction. See the SUBWF and ADDWF instructions for examples.
A simplified block diagram is shown in Figure 2-1 with the corresponding device pins described in Table 2-1 (for PIC16F54), Table 2-2 (for PIC16F57) and Table 2-3 (for PIC16F59).
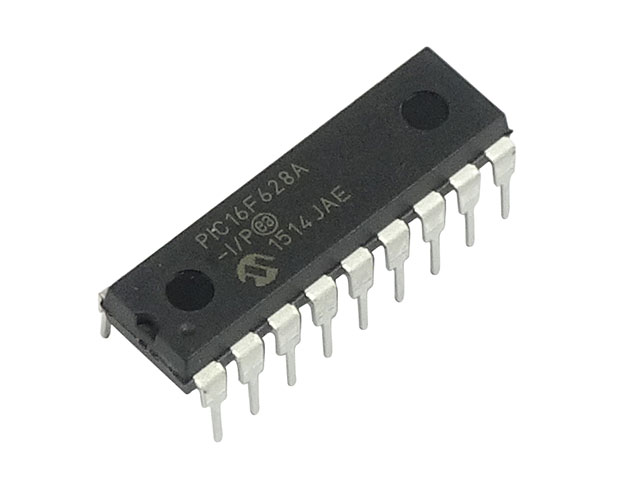
 Break Microcontroller PIC16F628A Content
Break Microcontroller PIC16F628A Content
In many long-running products, industrial tools, and legacy control modules, the Microchip PIC16F628A remains a highly trusted and widely deployed microcontroller. Its balance of cost, performance, and stable embedded design makes it a backbone component across manufacturing equipment, consumer devices, smart access systems, and compact automation solutions. When access to its flash, EEPROM, or internal memory becomes restricted due to protective, locked, or encrypted settings, equipment owners may struggle to maintain or revive their production assets. Our authorized recovery service, introduced under the subject Break Microcontroller PIC16F628A Content, is specifically created to help legitimate customers regain access to their own data, program configuration, and operational firmware without disclosing technical attack methods.
Industry Use Cases of PIC16F628A
The PIC16F628A is extensively adopted in:
- Compact automation controllers and industrial timers
- Entry-level motor drivers and sensor control modules
- Communication interface boards and remote monitors
- Consumer appliances and low-power handheld devices
Because these applications store calibrated parameters, system logic, or customer-specific source code, preserving or retrieving the internal archive becomes critical whenever the hardware needs repair, replacement, or upscaling.

We can break Microcontroller PIC16F628A Content, please view the Microcontroller PIC16F628A features for your reference:
GENERAL DESCRIPTION
The PIC16F627A/628A/648A are 18-Pin FLASH-based members of the versatile PIC16CXX family low cost, high performance, CMOS, fully-static, 8-bit microcontroller.
All PICmicro® microcontrollers employ an advanced RISC architecture. The PIC16F627A/628A/648A have enhanced core features, eight-level deep stack, and multiple internal and external interrupt sources. The separate instruction and data buses of the Harvard architecture allow a 14-bit wide instruction word with the separate 8-bit wide data.
The two-stage instruction pipeline allows all instructions to execute in a single-cycle, except for program branches (which require two cycles). A total of 35 instructions (reduced instruction set) are available, complemented by a large register set.
Our service focuses on helping authorized owners retrieve, clone, or duplicate the binary or heximal image stored in the PIC16F628A’s flash and EEPROM regions. Many units are shipped with protected or secured settings that prevent unauthorized copying; however, legitimate companies may still need to break barriers caused by forgotten revision histories, unavailable designers, supplier bankruptcy, or aging hardware.
We support clients by generating a verified file containing the extracted program and operational data, ensuring that future repairs or redesigns remain possible. All engagements emphasize confidentiality, legal compliance, and IP ownership verification.
General High-Level Concept (Non-Technical & Non-Actionable)
A typical recovery evaluation looks at the device condition, the level of encrypted or locked configuration, and possible integrity issues within the embedded memory. In some cases, physical analysis may be required, such as chip inspection or authorized decapsulation assessments, though details of any internal processes are never disclosed.

The objective is not to teach customers how to hack, decode, or attack a device, but rather to deliver a complete, usable archive that restores their ability to maintain, continue, or evolve their own systems.
PIC16F628A microcontrollers typically achieve a 2:1 code compression and a 4:1 speed improvement over other 8-bit microcontrollers in their class. PIC16F627A/628A/648A devices have integrated features to reduce external components, thus reducing system cost, enhancing system reliability and reducing power consumption.
The PIC16F628A has 8 oscillator configurations. The single-pin RC oscillator provides a low cost solution. The LP oscillator minimizes power consumption, XT is a standard crystal, and INTOSC is a self-contained precision two-speed internal oscillator to read MCU. The family HS is for High-Speed crystals. The EC mode is for an external clock source.
Clients turn to our service for several legitimate reasons:
- Restoring access to lost or outdated firmware
- Migrating old product lines to new hardware platforms
- Preparing backup binary archives for compliance or safety audits
- Rebuilding operational settings when the original design house is unavailable
- Maintaining machines that must stay functional for many more years
With a validated memory file, businesses avoid production downtime, eliminate guesswork, and continue improving their systems with confidence.
Challenges We May Encounter
Projects involving PIC16F628A often involve obstacles such as:
- Deeply protected configuration bits
- Possible memory wear and partial corruption
- Device variants with different internal layouts
- Environmental damage or aging affecting access reliability
Nonetheless, our team provides clear feasibility evaluations, transparent expectations, and controlled, professional workflow throughout the entire recovery cycle.
 Break MCU PIC16F631 Flash
Break MCU PIC16F631 Flash
When a device depends on the Microchip PIC16F631 for control, timing, or sensor interfacing, loss of access to on-chip flash or EEPROM can stop equipment and erase critical calibration data. Our service, indexed as Break MCU PIC16F631 Flash, helps legitimate owners and authorized technicians open, readout, restore, and duplicate the embedded firmware/binary/heximal images stored in these controllers. We focus on safe, lawful recovery that returns usable program archives without revealing methods to crack, hack, or bypass protections.
Clients commonly need us to restore corrupted files, copy firmware for authorized spares, clone settings for production, or duplicate configuration archives before servicing legacy systems. Devices using the PIC16F631 often contain small but vital pieces of source code, calibration tables and settings in flash or EEPROM — assets that, when protected, may be inaccessible without professional, authorized support.
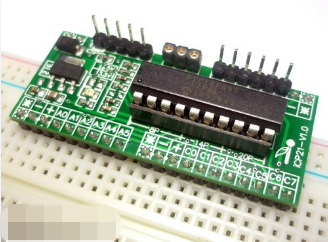
We can Break MCU PIC16F685 flash, please view the MCU PIC16F685 features for your reference:
High-Performance RISC CPU:
· Only 35 instructions to learn:
– All single-cycle instructions except branches
The PIC16F631’s compact footprint and mixed-signal capabilities make it a frequent choice across many industries:
- Consumer electronics and appliance controllers.
- Industrial sensors and simple automation modules.
- Instrumentation and small test equipment.
- Aftermarket automotive modules and hobbyist/legacy embedded systems.
Because these applications store operational data and program archives on the device, being able to recover a verified binary or heximal dump can be essential to restore service quickly.
· Operating speed:
– DC – 20 MHz oscillator/clock input
– DC – 200 ns instruction cycle
· Interrupt capability
· 8-level deep hardware stack
· Direct, Indirect and Relative Addressing modes
Special Microcontroller Features:
· Precision Internal Oscillator:
– Factory calibrated to ± 1%
– Software selectable frequency range of 8 MHz to 32 kHz
– Software tunable
– Two-Speed Start-up mode
– Crystal fail detect for critical applications
– Clock mode switching during operation for power savings
· Power-Saving Sleep mode
· Wide operating voltage range (2.0V-5.5V)
· Industrial and Extended Temperature range
· Power-on Reset (POR)
· Power-up Timer (PWRTE) and Oscillator Start-up Timer (OST)
· Brown-out Reset (BOR) with software control option and for MCU reading
· Enhanced low-current Watchdog Timer (WDT) with on-chip oscillator (software selectable nominal 268 seconds with full prescaler) with software enable
· Multiplexed Master Clear/Input pin
· Programmable code protection
· High Endurance Flash/EEPROM cell:
– 100,000 write Flash endurance
– 1,000,000 write EEPROM endurance
– Flash/Data EEPROM retention: > 40 years
· Enhanced USART module:
– Supports RS-485, RS-232 and LIN 2.0
– Auto-Baud Detect
– Auto-wake-up on Start bit
The PIC16F631 integrates modest program flash, EEPROM, and analog/digital peripherals in a tight package. Its memory layout concentrates configuration and calibration data in discrete regions, and many designs set protective or locked configurations to prevent unauthorized copying. Those features shape how a lawful recovery is scoped and the kinds of deliverables that best serve the end user.

What we provide (high level, non-actionable)
Our engagements emphasize ethical, non-destructive recovery. Typical deliverables include validated binary/heximal dumps of flash and EEPROM where permitted, integrity and checksum reports, and high-level annotated summaries that help engineers interpret recovered program logic. We can assist clients to restore devices to operation using recovered files, prepare migration packages for replacement hardware, and advise on safe duplication and archival strategies. Importantly, we do not publish or provide step-by-step instructions to decrypt, unlock, or otherwise compromise manufacturer protections.
Conceptual approach and purpose
A responsible recovery project begins with verification of ownership and a feasibility assessment. The objective is to obtain a reliable memory archive and translate raw data into a usable representation for maintenance, testing, or authorized redevelopment. The primary purposes are to reduce downtime, secure previously inaccessible firmware, and enable legitimate copying or cloning for spares and production.
Benefits for the end user
Clients benefit from secure backups of embedded firmware and data, faster restoration of equipment, and the ability to duplicate or deploy authorized copies across installations. Recovered program archives reduce the need to rebuild software from scratch and protect investment in specialized hardware.
Challenges and limitations
Obstacles can include layered protective settings, partial memory corruption, variant device revisions, and proprietary integrity checks. Full source-level reconstruction is not always possible; often the practical outcome is a validated heximal or binary archive with assembly-level annotations. We communicate feasibility and likely outcomes before proceeding.
Legal & ethical safeguards
All projects require explicit authorization and operate under confidentiality agreements. Our mission is to help rightful owners recover, restore, and preserve their embedded systems for lawful, constructive purposes only.
If you need to Break MCU PIC16F631 Flash for authorized recovery, maintenance, or archival purposes, our experienced team provides confidential, professional support to retrieve and document your embedded program and data while protecting your IP and operational continuity.
 Break IC PIC16F685 Code
Break IC PIC16F685 Code
When an embedded system depends on the Microchip PIC16F685, losing access to its program or finding the device set to protected can halt operations and complicate maintenance. Our service, searchable under the keyword Break IC PIC16F685 Code, helps authorized owners and engineers open, readout, restore, and duplicate the firmware/binary/heximal contents of these microcontrollers. We deliver validated memory archives and high-level analysis while strictly avoiding publication of methods to illegally crack or hack protections.
The need to copy, clone, or duplicate a PIC16F685’s program file arises in many legitimate scenarios: restoring corrupted flash or EEPROM after a failure, recovering crucial calibration data, preparing authorized spares, or migrating long-lived products to replacement hardware. In many cases the firmware is locked or secured by the original integrator; safely extracting a verified binary or heximal dump can be the fastest route to restore operation without redesign.
We can Break IC PIC16F685 Code, please view the Ic PIC16F685 features for your reference:
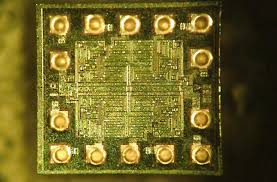
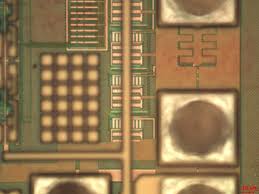
The PIC16F685 has a 13-bit program counter capable of addressing an 8K x 14 program memory space. Only the first 1K x 14 (0000h-03FFh) is physically implemented for the PIC16F631, the first 2K x 14 (0000h-07FFh) for the PIC16F677/PIC16F687, and the first 4K x 14 (0000h-0FFFh) for the PIC16F685/PIC16F689/ PIC16F690 when Break Ic. Accessing a location above these boundaries will cause a wraparound. The Reset vector is at 0000h and the interrupt vector is at 0004h.
The data memory (see Figures 2-6 through 2-8) is partitioned into four banks which contain the General Purpose Registers (GPR) and the Special Function Registers (SFR). The Special Function Registers are located in the first 32 locations of each bank. The CALL, RETURN RETFIE, RETLW.
General Purpose Registers, implemented as static RAM, are located in the last 96 locations of each Bank. Register locations F0h-FFh in Bank 1, 170h-17Fh in Bank 2 and 1F0h-1FFh in Bank 3 point to addresses 70h-7Fh in Bank 0. The actual number of General Purpose Resisters (GPR) in each Bank depends on the device. Details are shown in Figures 2-4 through 2-8.
All other RAM is unimplemented and returns ‘0’ when Reset Vector 0000h read. RP<1:0> of the STATUS register are the bank select bits:
The register file is organized as 128 x 8 in the PIC16F687 and 256 x 8 in the PIC16F685/PIC16F689/PIC16F690. Each register is accessed, either directly or indirectly, through the File Select Register (FSR) (see Section 2.4 “Indirect Addressing, INDF and FSR Registers”) by Break IC PIC16F685 Code.
SPECIAL FUNCTION REGISTERS
The Special Function Registers are registers used by the CPU and peripheral functions for controlling the desired operation of the device for MCU Reading (see Tables 2-1 through 2-4). These registers are static RAM.
The special registers can be classified into two sets: core and peripheral. The Special Function Registers associated with the “core” are described in this section. Registers related to the operation of peripheral features are described in the section of that peripheral feature.
The PIC16F685 is widely used where compact control and analog interfacing matter:
- Consumer electronics and appliance controllers.
- Industrial sensors and small automation modules.
- Instrumentation such as data loggers and test front-ends.
- Aftermarket automotive modules and hobbyist/legacy embedded systems.
Because these devices often store important configuration data and small program archives in on-chip memory, access to those files is frequently necessary for repair and continuity.
Unique features that affect recovery
This MCU combines flexible I/O, analog peripherals, and modest on-chip flash and EEPROM storage. Its architecture means that both program and calibration data may be tightly integrated, and many designs apply protective settings to prevent unauthorized copying. Those characteristics shape how recovery is approached and the kinds of deliverables that are most useful to end users.

What we provide (high-level, non-actionable)
Our engagements focus on ethical, non-destructive recovery outcomes. Typical services include: validated extraction of memory images (producing binary/heximal dumps), integrity checks and verification reports, and high-level disassembly summaries that help engineers interpret recovered program logic. We can assist clients in using recovered files to restore devices to operation or prepare migration packages for replacement hardware. We do not provide step-by-step instructions or tools intended to decrypt, bypass, or otherwise subvert manufacturer or integrator-applied protections.
General idea (conceptual)
A responsible recovery project begins with ownership verification and a feasibility assessment. Engineers then pursue conservative, evidence-based techniques to obtain a reliable archive of the device’s memory and to validate its integrity. The aim is to return a usable program image that enables authorized copying, duplication, or rebuilding while preserving device health and intellectual property.
Benefits and likely outcomes
Clients who use this service gain secure backups of previously inaccessible firmware and data, reduced downtime through faster restoration, and the ability to clone or duplicate devices for approved spares provisioning. Recovered binary or heximal archives support testing, compliance checks, and migration without starting from scratch.
Challenges and limitations
Recovery may be hindered by layered protections, partial data corruption, variant hardware revisions, or proprietary integrity checks. Full source-code reconstruction is not always possible; often the realistic deliverable is a validated firmware image with assembly-level annotations.
Ethics and authorization
We require proof of ownership or explicit authorization for all projects and operate under strict confidentiality agreements. Our mission is to help rightful owners unlock, restore, and preserve their embedded systems for lawful, constructive purposes only.

If you need to Break IC PIC16F685 Code for authorized recovery, maintenance, or archival purposes, our team provides confidential, professional support to retrieve and document your embedded firmware and data while protecting your IP and operational continuity.
 Recover Chip PIC16F689 Flash
Recover Chip PIC16F689 Flash
When a device depends on a Microchip PIC16F689 for control, timing, or sensor interfacing, losing access to the on-chip flash or EEPROM can halt production, disrupt service, or erase critical calibration data. Our service, searchable under the keyword Recover Chip PIC16F689 Flash, helps legitimate owners and authorized technicians open, readout, restore, and duplicate the firmware/binary/heximal contents of this microcontroller while maintaining strict legal, ethical, and confidentiality standards. We emphasize recovery and preservation — not publishing methods to crack or illegally hack protections.

The PIC16F689 is commonly embedded in devices where small, reliable control programs and configuration archives are essential. Clients come to us to restore corrupted program files, copy firmware for authorized spares provisioning, clone configuration data for scaled deployment, or duplicate critical archives before servicing legacy systems. In many scenarios the firmware or memory image is protected, locked, or encrypted by design, so an authorized recovery partner is required to retrieve usable program files without risking further damage.

We can Recover Chip PIC16F689 Flash, please view the CHIP PIC16F689 features below for your reference:
High-Performance RISC CPU:
· Only 35 Instructions to Learn:
– All single-cycle instructions except branches
· Operating Speed:
– DC – 20 MHz oscillator/clock input
– DC – 200 ns instruction cycle
· Interrupt Capability
· 8-level Deep Hardware Stack
Low-Power Features:
The PIC16F689’s blend of I/O, timers, and analog features makes it popular across many industries:
- Consumer electronics and appliance controllers.
- Industrial monitoring and simple automation modules.
- Instrumentation such as small data loggers and measurement front-ends.
- Aftermarket automotive or specialty embedded projects that rely on compact, efficient code.
In these contexts, recovered binary or heximal files enable quicker repairs, validated backups, and smoother migration to replacement hardware.

· Standby Current:
– 50 nA @ 2.0V, typical
· Operating Current:
– 11 ìA @ 32 kHz, 2.0V, typical
– 220 ìA @ 4 MHz, 2.0V, typical
· Watchdog Timer Current:
– 1 ìA @ 2.0V, typical
· Direct, Indirect and Relative Addressing modes
Peripheral Features:
Special Microcontroller Features:
· Precision Internal Oscillator:
– Factory calibrated to ±1%
– Software selectable frequency range of 8 MHz to 125 kHz
– Software tunable
– Two-Speed Start-Up mode
– Crystal fail detect for critical applications
– Clock mode switching during operation for power savings
· Power-Saving Sleep mode
· Wide Operating Voltage Range (2.0V-5.5V)
· Industrial and Extended Temperature Range
· Power-on Reset (POR)
· Power-up Timer (PWRT) and Oscillator Start-up Timer (OST)
· Brown-out Reset (BOR) with Software Control Option

· Enhanced Low-Current Watchdog Timer (WDT) with on-chip oscillator (software selectable nominal 268 seconds with full prescaler) with software enable
· Multiplexed Master Clear with Weak Pull-up or Input Only Pin
· Programmable Code Protection
· High-Endurance Flash/EEPROM Cell:
– 100,000 write Flash endurance
– 1,000,000 write EEPROM endurance
– Flash/Data EEPROM retention: > 40 years
· 12 I/O Pins with Individual Direction Control:
– High-current source/sink for direct LED drive
– Interrupt-on-change pin
– Individually programmable weak pull-ups
– Ultra Low-Power Wake-up
· Analog Comparator module with:
– Two analog comparators
– Programmable On-chip Voltage Reference (CVREF) module (% of VDD)
– Comparator inputs and outputs externally accessible
· A/D Converter:
– 10-bit resolution and 8 channels
· Timer0: 8-bit Timer/Counter with 8-bit Programmable Prescaler
· Enhanced Timer1:
– 16-bit timer/counter with prescaler
– External Timer1 Gate (count enable)
– Option to use OSC1 and OSC2 in LP mode as Timer1 oscillator if INTOSC mode selected
· Enhanced USART Module:
– Supports RS-485, RS-232, LIN 2.0/2.1 and J2602
– Auto-Baud Detect
– Auto-wake-up on Start bit
· In-Circuit Serial Programming™ (ICSP™) via two pins
The PIC16F689 integrates program flash, EEPROM, and mixed-signal peripherals in a compact package. Its memory layout and on-chip configuration bits influence how the source code (if available) maps to raw files and how sensitive calibration data is stored. Because many designs apply protective settings to prevent unauthorized copying, recovery must be planned carefully to avoid corrupting valuable data.
What we provide (high level & non-actionable)
Our engagements are oriented around ethical recovery. Services include: validated extraction of on-chip images producing heximal or binary dumps (where lawful), integrity checks and documented verification, and high-level disassembly summaries to help engineers interpret the recovered program. We can assist with restoring devices to operation using recovered images and preparing migration packages for replacement boards. We do not provide step-by-step instructions to crack, decrypt, or bypass manufacturer protections — all work is performed only with proof of ownership or explicit authorization.
Conceptual workflow and purpose
A responsible recovery effort begins with authorization and a risk assessment. Non-destructive techniques are used to obtain a reliable memory archive, which is then validated and annotated. The primary purpose is practical: reduce downtime, secure backups, enable authorized copying or cloning, and preserve investment in specialized hardware.
Benefits and limitations
Clients gain rapid restoration of functionality, secure copies of previously inaccessible firmware and configuration archives, and the ability to duplicate systems for authorized maintenance. Limitations can include partial corruption, proprietary integrity checks, or layered locked settings — outcomes that may restrict full source-level recovery. We make feasibility and likely results clear before work begins.
Legal & ethical safeguards
Every project requires ownership verification and a confidentiality agreement. Our mission is to unlock and recover embedded software for lawful, constructive purposes only — repair, continuity, authorized audit, and migration.
If you need to Recover Chip PIC16F689 Flash for legitimate recovery or maintenance, our experienced team provides confidential, professional support to retrieve and document embedded firmware while protecting your IP and operational continuity.
 Copy Chip PIC16F73 Program
Copy Chip PIC16F73 Program
When an embedded product built around the Microchip PIC16F73 faces firmware loss, corruption, or locked flash, the need to copy chip PIC16F73 program becomes urgent. Our service helps authorized owners and system integrators open, readout, restore, and duplicate the firmware/binary/heximal images stored in these protected microcontrollers, delivering dependable outcomes while maintaining strict legal and ethical controls.

Why customers ask for this service
The PIC16F73 is a classic 8-bit microcontroller found in a wide range of low- to mid-complexity systems. Legitimate reasons to request recovery include the need to restore corrupted program files after an update failure, copy/clone software for authorized manufacturing runs, or duplicate configuration archives for spares provisioning. Other uses are migrating legacy systems to newer hardware or performing authorized audits to validate safety and compliance. In each case, being able to access the embedded program and data is essential to maintain uptime and preserve investment.

We can Copy Chip PIC16F73 Program, please view the Chip PIC16F73 features for your reference:
The PIC16C7X is a family of low-cost, high-performance, CMOS, fully-static, 8-bit chips with integrated analog-to-digital (A/D) converters, in the PIC16CXX mid-range family. All PIC16/17 chips employ an advanced RISC architecture. The PIC16CXX chip family has enhanced core features, eight-level deep stack, and multiple internal and external interrupt sources.
Typical applications of PIC16F73
This MCU appears in many industries because of its simple, reliable architecture:
- Consumer electronics (appliances, toys, small controllers).
- Industrial sensors and controllers (simple PLC peripherals, timers).
- Instrumentation and test equipment (data loggers, measurement front-ends).
- Hobbyist and legacy embedded projects where small flash and EEPROM suffice.
Its ubiquity means firmware recovery often supports long-lived products where original source code or production files are no longer available.
Unique features that shape recovery
The PIC16F73’s modest flash and EEPROM memory, combined with configurable I/O and basic analog peripherals, influences how the binary/heximal image is stored and what data is most valuable — for example, calibration tables or small configuration archives. Many devices protect their flash to prevent unauthorized copying; such locked or secured settings require careful, authorized handling to avoid damaging the device or corrupting memory.
What we provide (high-level, non-actionable)
Our engagements focus on lawful, confidential recovery and analysis. Services include: verified extraction of flash and EEPROM images (producing heximal or binary dumps), validated checksums and integrity reports, and high-level disassembly summaries to help engineers understand recovered program logic. We can assist clients to restore devices to operation using recovered files, and prepare migration packages for replacement hardware. We do not provide instructions to crack or illegally hack protections; all work is performed only with proof of ownership or explicit authorization.
The separate instruction and data buses of the Harvard architecture allow a 14-bit wide instruction word with the separate 8-bit wide data. The two stage instruction pipeline allows all instructions to execute in a single cycle, except for program branches which require two cycles. A total of 35 instructions (reduced instruction set) are available. Additionally, a large register set gives some of the architectural innovations used to achieve a very high performance.
PIC16CXX chips typically achieve a 2:1 code compression and a 4:1 speed improvement over other 8-bit chips in their class. The PIC16C72 has 128 bytes of RAM and 22 I/O pins.
In addition several peripheral features are available including: three timer/counters, one Capture/Compare/PWM module and one serial port. The Synchronous Serial Port can be configured as either a 3-wire Serial Peripheral Interface (SPI) or the two-wire Inter-Integrated Circuit (I 2C) bus. Also a 5-channel high-speed 8-bit A/D is provided. The 8-bit resolution is ideally suited for applications requiring low-cost analog interface, e.g. thermostat control, pressure sensing, etc.
The PIC16C73/73A devices have 192 bytes of RAM, while the PIC16C76 has 368 byes of RAM. Each device has 22 I/O pins. In addition, several peripheral features are available including: three timer/counters, two Capsuited for applications requiring low-cost analog interface, e.g. thermostat control, pressure sensing, etc.

The PIC16C7X family has special features to reduce external components, thus reducing cost, enhancing system reliability and reducing power consumption which can be used for MCU Cracking.
There are four oscillator options, of which the single pin RC oscillator provides a low-cost solution, the LP oscillator minimizes power consumption, XT is a standard crystal, and the HS is for High Speed crystals. The SLEEP (power-down) feature provides a power saving mode. The user can wake up the chip from SLEEP through several external and internal interrupts and resets.
General idea of the process (conceptual)
A project begins with ownership verification and a risk assessment. Engineers then perform conservative, non-destructive readout attempts to obtain a safe memory archive. Extracted program files are validated, documented, and, where permitted, annotated to aid integration or redevelopment. This conceptual workflow prioritizes preserving device integrity and the confidentiality of sensitive code.
Benefits and likely outcomes
Clients receive secure backups of previously inaccessible firmware and data, reducing downtime and enabling authorized copying or cloning for spares and production. Recoveries can unlock the ability to test, debug, or redeploy legacy systems without rewriting entire applications from scratch.
Challenges and limitations
Recovery can be complicated by layered protections, partial corruption, or variant device memory maps. Full source-level restoration is not always possible; often the deliverable is a validated binary/heximal archive and assembly-level annotations.
We require legal authorization for every job and operate under strict confidentiality agreements. If you need to Copy Chip PIC16F73 Program for legitimate restoration, duplication, or migration, our experienced team can help you recover and secure your embedded firmware while protecting your IP and operational continuity.

A highly reliable Watchdog Timer with its own on-chip RC oscillator provides protection against software lock up.
A UV erasable CERDIP packaged version is ideal for code development while the cost-effective One-Time-Programmable (OTP) version is suitable for production in any volume.
The PIC16C7X family fits perfectly in applications ranging from security and remote sensors to appliance control and automotive. The EPROM technology makes customization of application programs (transmitter codes, motor speeds, receiver frequencies, etc.) extremely fast and convenient. The small footprint packages make this chip series perfect for all applications with space limitations.
Low cost, low power, high performance, ease of use and I/O flexibility make the PIC16C7X very versatile even in areas where no chip use has been considered before (e.g. timer functions, serial communication, capture and compare, PWM functions and coprocessor applications).
 Copy MCU XC18V04PC44C Program
Copy MCU XC18V04PC44C Program
In the specialized field of reverse engineering, few tasks are as technically demanding as attempting to copy, clone, or recover program code from secured microcontrollers like the XILINX XC18V04PC44C CPLD. This complex FPGA configuration chip is often deployed in critical systems where intellectual property protection is paramount. The process of firmware extraction from such protected, encrypted, or locked devices represents the pinnacle of technical reverse engineering, requiring sophisticated methodologies to decrypt, decode, or otherwise break advanced security mechanisms without physical destruction of the component. This article explores the technical challenges, ethical considerations, and significant benefits underlying this delicate process.
We can Copy MCU XC18V04PC44C Program, please view below MCU XC18V04PC44C features for your reference:
XILINX XC18V04PC44C: Deployment and Security Significance
The XILINX XC18V04PC44C is not a standard microcontroller but a CPLD (Complex Programmable Logic Device) specifically designed for configuration storage in high-reliability applications. This chip frequently serves critical functions across several industries:
- Telecommunications Infrastructure: Used in network routing and switching equipment for storing configuration bitstreams that define hardware functionality
- Aerospace and Defense Systems: Employed in avionics and military hardware where firmware integrity is crucial for operational safety and security
- Industrial Automation: Found in programmable logic controllers (PLCs) and manufacturing control systems
- Medical Electronics: Utilized in diagnostic and therapeutic medical devices requiring reliable configuration storage

As a non-volatile memory component, the XC18V04PC44C stores configuration data that defines the operational characteristics of associated FPGAs or other programmable logic. The secured nature of this chip prevents unauthorized access to proprietary algorithms and hardware implementations, protecting significant research and development investments embodied in the firmware
XC18V00 Series In-System-Programmable Configuration PROMs:
Product Specification:
In-System Programmable 3.3V PROMs for Configuration of Xilinx FPGAs
♦ Endurance of 20,000 Program/Erase Cycles
♦ Program/Erase Over Full Industrial Voltage and Temperature Range (–40°C to +85°C)
IEEE Std 1149.1 Boundary-Scan (JTAG) Support
JTAG Command Initiation of Standard FPGA Configuration
Simple Interface to the FPGA

Cascadable for Storing Longer or Multiple Bitstreams
Low-Power Advanced CMOS FLASH Process Dual Configuration Modes
Technical Challenges in Accessing Protected Memory
Attempting to recover, clone, or replicate the binary or heximal content from a secured XC18V04PC44C presents formidable technical obstacles that differentiate this process from simple microcontroller duplication:
- Advanced Encryption and Protection Schemes: Unlike simpler microprocessors, the XC18V04PC44C typically incorporates sophisticated security measures designed specifically to prevent firmware extraction. These may include hardware-based encryption of the configuration data, volatile key storage that disappears upon power disruption, and active tamper-detection circuits that can erase critical memory content if intrusion is detected
- Proprietary Memory Architecture: The internal flash or EEPROM memory structure of these specialized chips often differs significantly from standard microcontroller architectures. Without detailed documentation of the memory mapping and access protocols, even bypassing security does not guarantee successful interpretation of the extracted binary data
- Limited Attack Vectors: Standard reverse engineering approaches such as debug port exploitation or simple decapsulation often prove ineffective against properly implemented security in the XC18V04PC44C. The chip’s design specifically anticipates and mitigates these common attack methods, necessitating more advanced approaches
♦ Serial Slow/Fast Configuration (up to 33 MHz)
♦ Parallel (up to 264 Mb/s at 33 MHz)

5V-Tolerant I/O Pins Accept 5V, 3.3V and 2.5V Signals
3.3V or 2.5V Output Capability
Design Support Using the Xilinx ISE™ Foundation™ Software Packages
Available in PC20, SO20, PC44, and VQ44 Packages
Lead-Free (Pb-Free) Packaging
Description
Xilinx introduces the XC18V00 series of in-system programmable configuration PROMs (Figure 1). Devices in this 3.3V family include a 4-megabit, a 2-megabit, a 1-megabit, and a 512-kilobit PROM that provide an easy-to- use, cost-effective method for reprogramming and storing Xilinx FPGA configuration bitstreams. When the FPGA is in Master Serial mode, it generates a configuration clock that drives the PROM.
A short access time after CE and OE are enabled, data is available on the PROM DATA (D0) pin that is connected to the FPGA DIN pin. New data is available a short access time after each rising clock edge. The FPGA generates the appropriate number of clock pulses to complete the configuration. When the FPGA is in Slave Serial mode, the PROM and the FPGA are clocked by an external clock.
When the FPGA is in Master SelectMAP mode, the FPGA generates a configuration clock that drives the PROM. When the FPGA is in Slave Parallel or Slave SelectMAP mode, an external oscillator generates the configuration clock that drives the PROM and the FPGA.

After CE and OE are enabled, data is available on the PROM’s DATA (D0-D7) pins. New data is available a short access time after each rising clock edge. The data is clocked into the FPGA on the following rising edge of the CCLK. A free-running oscillator can be used in the Slave Parallel or Slave SelecMAP modes.
Multiple devices can be cascaded by using the CEO output to drive the CE input of the following device. The clock inputs and the DATA outputs of all PROMs in this chain are interconnected. All devices are compatible and can be cascaded with other members of the family or with the XC17V00 one-time programmable serial PROM family.
 Copy IC DSP TMS320LF2401AVFA Flash
Copy IC DSP TMS320LF2401AVFA Flash
We can Copy IC DSP TMS320LF2401AVFA Flash, please view below IC DSP TMS320LF2401AVFA features for your reference:
High-Performance Static CMOS Technology
− 25-ns Instruction Cycle Time (40 MHz)
− 40-MIPS Performance
− Low-Power 3.3-V Design Based on TMS320C2xx DSP CPU Core
− Code-Compatible With F243/F241/C242
− Instruction Set and Module Compatible With F240 Flash (LF) and ROM (LC) Device Options
− LF240xA: LF2407A, LF2406A, LF2403A, LF2402A
− LC240xA: LC2406A, LC2404A, LC2403A, LC2402A
On-Chip Memory
− Up to 32K Words x 16 Bits of Flash EEPROM (4 Sectors) or ROM
− Programmable “Code-Security” Feature for the On-Chip Flash/ROM
− Up to 2.5K Words x 16 Bits of Data/Program RAM
− 544 Words of Dual-Access RAM
− Up to 2K Words of Single-Access RAM Boot ROM (LF240xA Devices)
− SCI/SPI Bootloader Up to Two Event-Manager (EV) Modules (EVA and EVB), Each Includes:
− Two 16-Bit General-Purpose Timers
− Eight 16-Bit Pulse-Width Modulation (PWM) Channels Which Enable:
− Three-Phase Inverter Control
− Center- or Edge-Alignment of PWM Channels
− Emergency PWM Channel Shutdown With External PDPINTx Pin
− Programmable Deadband (Deadtime) Prevents Shoot-Through Faults
− Three Capture Units for Time-Stamping of External Events
− Input Qualifier for Select Pins
− On-Chip Position Encoder Interface Circuitry to faciliate the process of IC Cloning
− Synchronized A-to-D Conversion
− Designed for AC Induction, BLDC, Switched Reluctance, and Stepper Motor Control
− Applicable for Multiple Motor and/or Converter Control
External Memory Interface (LF2407A)
− 192K Words x 16 Bits of Total Memory:
64K Program, 64K Data, 64K I/O Watchdog (WD) Timer Module 10-Bit Analog-to-Digital Converter (ADC)
− 8 or 16 Multiplexed Input Channels
− 500-ns MIN Conversion Time
− Selectable Twin 8-State Sequencers Triggered by Two Event Managers Controller Area Network (CAN) 2.0B Module (LF2407A, 2406A, 2403A)
Serial Communications Interface (SCI)
16-Bit Serial Peripheral Interface (SPI)
(LF2407A, 2406A, LC2404A, 2403A)
Phase-Locked-Loop (PLL)-Based Clock
Generation
Up to 40 Individually Programmable,
Multiplexed General-Purpose Input / Output (GPIO) Pins
Up to Five External Interrupts (Power Drive
Protection, Reset, Two Maskable Interrupts) Power Management:
− Three Power-Down Modes
− Ability to Power Down Each Peripheral Independently
Real-Time JTAG-Compliant Scan-Based
Emulation, IEEE Standard 1149.1† (JTAG)
Development Tools Include:
− Texas Instruments (TI) ANSI C Compiler, Assembler/ Linker, and Code Composer Studio Debugger
− Evaluation Modules
− Scan-Based Self-Emulation (XDS510)
− Broad Third-Party Digital Motor Control Support Package Options
− 100-Pin LQFP PZ (2406A, LC2404A)
− 64-Pin TQFP PAG (LF2403A, LC2403A, LC2402A)
− 64-Pin QFP PG (2402A)
Extended Temperature Options (A and S)
− A: − 40°C to 85°C
− S: − 40°C to 125°C