 Break Microcontroller PIC16F886 Software
Break Microcontroller PIC16F886 Software
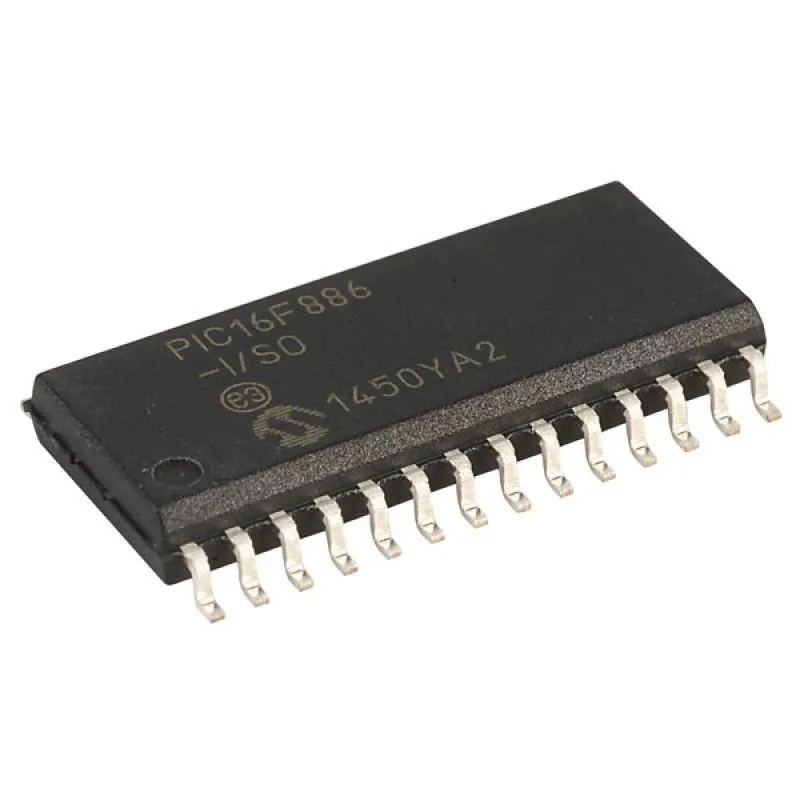
When an embedded device built around the Microchip PIC16F886 becomes inaccessible due to protected, locked, or encrypted flash, organizations face costly downtime, loss of calibration data, or the inability to support legacy systems. Our service, indexed as Break Microcontroller PIC16F886 Software, helps authorized owners open, readout, recover, and duplicate the firmware/binary/heximal contents of PIC16F886 devices — delivering usable program images and analysis while operating strictly within legal and ethical boundaries.
Why clients request this service
Common legitimate reasons to seek help include:
- Restore corrupted or accidentally erased flash/eeprom program files.
- Recover critical calibration data or archived device settings.
- Duplicate/clone firmware for authorized manufacturing, spares provisioning, or legacy support.
- Audit embedded code for compliance, safety validation, or security assessment.
What we provide (high-level, non-technical)
We perform authorized recovery and analysis without publishing or enabling methods to bypass protections. Our deliverables typically include:
- Verified binary/heximal dumps of on-chip memory where legally permitted.
- High-level disassembly and annotated summaries (non-actionable) to aid system engineers.
- Export of recovered program files/archives in formats suitable for testing or migration.
- Documentation and recommendations to restore devices, migrate firmware, or rebuild lost source where possible.
We can Break Microcontroller PIC16F886 Software, please view the Microcontroller PIC16F886 features for your reference:
The Program Counter (PC) is 13 bits wide. The low byte comes from the PCL register, which is a readable and writable register. The high byte (PC<12:8>) is not directly readable or writable and comes from PCLATH. On any Reset, the PC is cleared.
Figure 2-7 shows the two situations for the loading of the PC. The upper example in Figure 2-7 shows how the PC is loaded on a write to PCL (PCLATH<4:0> → PCH). The lower example in Figure 2-7 shows how the PC is loaded during a CALL or GOTO instruction (PCLATH<4:3> → PCH to Copy microcontroller.

The PIC16F882/883/884/886/887 devices have an 8-level x 13-bit wide hardware stack (see Figures 2-2 and 2-3). The stack space is not part of either program or data space and the Stack Pointer is not readable or writable when Extract MCU. The PC is PUSHed onto the stack when a CALL instruction is executed or an interrupt causes a branch. The stack is POPed in the event of a RETURN, RETLW or a RETFIE instruction execution. PCLATH is not affected by a PUSH or POP operation.
What we provide (high-level, non-technical)
We perform authorized recovery and analysis without publishing or enabling methods to bypass protections. Our deliverables typically include:
- Verified binary/heximal dumps of on-chip memory where legally permitted.
- High-level disassembly and annotated summaries (non-actionable) to aid system engineers.
- Export of recovered program files/archives in formats suitable for testing or migration.
- Documentation and recommendations to restore devices, migrate firmware, or rebuild lost source where possible.
Applications of the PIC16F886
The PIC16F886 is commonly deployed across many industries because of its mix of I/O, analog capability, and low power characteristics. Typical applications include:
- Industrial control and small PLC peripherals.
- Consumer appliances and smart home devices.
- Measurement and instrumentation, including sensors and data loggers.
- Automotive subsystems and aftermarket modules.
Understanding the device context helps prioritize what data matters most — calibration tables, control loops, or configuration archives — and tailor recovery goals accordingly.
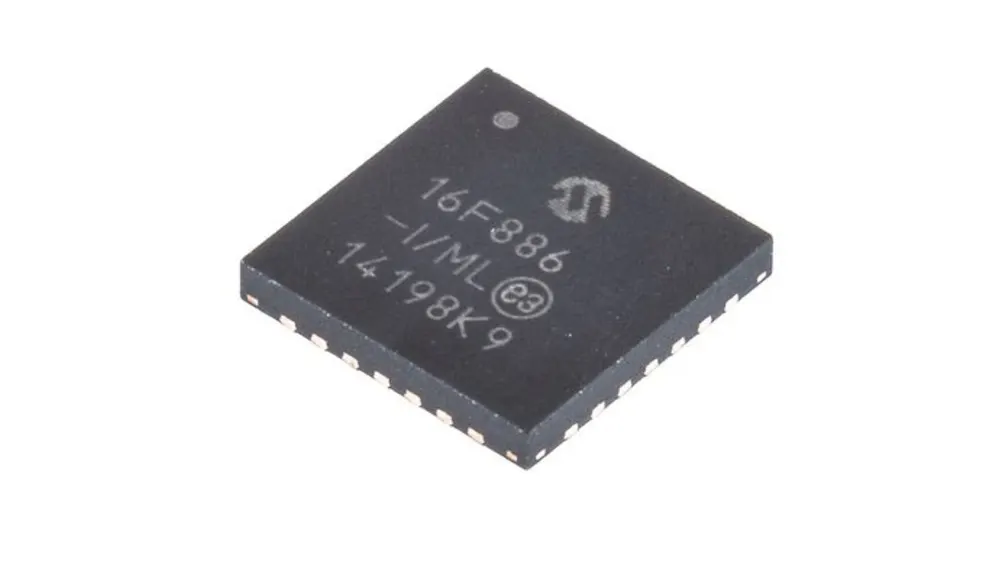
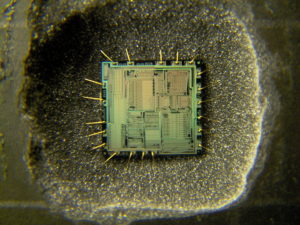
Unique features that affect recovery
The PIC16F886 integrates flash program memory, EEPROM, analog peripherals, and configurable I/O. These features, combined with manufacturer or integrator-applied protective settings, influence how firmware and data are stored and the complexity of a lawful recovery effort. Recovery work therefore needs careful non-destructive handling to avoid corrupting valuable memory or device hardware.
Benefits for the end user
Clients who use our service gain:
- Rapid restoration of device functionality and reduction of downtime.
- Secure backups of previously inaccessible firmware and data.
- Support for legacy equipment where original source code or production files are lost.
- Improved ability to maintain, test, and redeploy critical systems.
The stack operates as a circular buffer. This means that after the stack has been PUSHed eight times, the ninth push overwrites the value that was stored from the first push. The tenth push overwrites the second push (and so on). Executing any instruction with the PCL register as the destination simultaneously causes the Program Counter PC<12:8> bits (PCH) to be replaced by the contents of the PCLATH register. This allows the entire contents of the program counter to be changed by writing the desired upper 5 bits to the PCLATH register. When the lower 8 bits are written to the PCL register, all 13 bits of the program counter will change to the values contained in the PCLATH register and those being written to the PCL register.
Challenges and limitations
Recovery can encounter obstacles such as obscure device configurations, partial data corruption, or layered protection mechanisms. Not every recovery is guaranteed to restore full source-level clarity — sometimes only binary/heximal archives are recoverable. We always communicate limitations up front and provide practical options for mitigation.
Ethics, authorization & confidentiality
We require proof of ownership or explicit authorization before attempting any recovery. We do not provide guidance or tools intended to illegally crack, hack, or bypass protections, nor do we support unauthorized copying or distribution of copyrighted firmware. All engagements are performed under strict confidentiality and with clear legal agreements.
If you need to Break Microcontroller PIC16F886 Software for legitimate recovery, maintenance, or audit purposes, our experienced team offers secure, professional support to recover, duplicate, and restore embedded program data while protecting your intellectual property and operational continuity.
