Break Chip PIC16F720 Firmware
Break Chip PIC16F720 Firmware
The Microchip PIC16F720 is a popular 8-bit microcontroller widely deployed in industrial controls, consumer electronics, automotive modules, and a variety of embedded applications. With its compact architecture, integrated flash memory, and reliable performance, it is a preferred choice for engineers seeking efficiency and cost-effectiveness. However, many of these devices are shipped with protective or locked mechanisms enabled, making it nearly impossible to directly access or copy the stored firmware, binary data, or heximal program file. This is where professional reverse-engineering techniques come into play, offering the capability to Break Chip PIC16F720 Firmware and recover valuable system code.
Why Breaking PIC16F720 Firmware Matters
For engineers, manufacturers, and developers, accessing the original firmware from a protected PIC16F720 can be essential for multiple reasons:
- Restoration of lost source code when the original development files are missing.
- Cloning or duplicating embedded systems for hardware remanufacturing.
- Decoding or decrypting encrypted memory for system audits and security testing.
- Unlocking and copying archived data for repair, maintenance, or upgrade of long-life industrial devices.
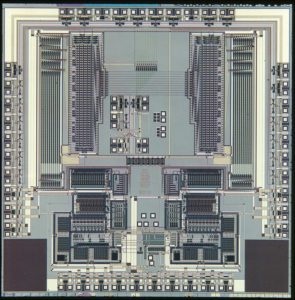
By extracting the locked program from the device’s flash memory and EEPROM, one can reconstruct the embedded logic, analyze vulnerabilities, or migrate to upgraded platforms without losing critical functionality.
General Steps in Breaking Chip Protection
Although the PIC16F720 employs secured fuse bits and protective lock functions, specialized processes exist to bypass these restrictions. The most common and general steps include:
Verification and duplication – Ensuring the recovered firmware matches the original program and can be safely cloned, copied, or restored to new devices.
Preparation and identification – Recognizing the exact device package and verifying whether protective fuses are enabled.
Disabling security fuses – Using advanced hardware and software tools to bypass or neutralize the lock bits that prevent readout.
Data extraction – Recovering the raw heximal file directly from flash memory or EEPROM.
Disassembly and decoding – Translating the binary archive into human-readable assembly language and, if needed, restoring it toward C/C++ source code for analysis or modification.
The PIC16F/LF720 and PIC16F/LF721 devices are programmed using In-Circuit Serial Programming™ (ICSP™). This programming specification applies to the PIC16F/LF720 and PIC16F/LF721 devices in all packages
With the exception of memory size and the voltage regulator, all other aspects of the PIC16F/LF720 and PIC16F/LF721 devices are identical.
Configuration Words
The PIC16F/LF720 and PIC16F/LF721 have two Configuration Words, Configuration Word 1 (2007h) and Configuration Word 2 (2008h). The individual bits within these Configuration Words are used to enable or disable device functions such as the Brown-out Reset, code protection to prevent MCU Reading and Power-up Timer.
Calibration Words
For the PIC16F/LF720 and PIC16F/LF721 devices, the 16 MHz internal oscillator (INTOSC) and the Brown-out Reset (BOR) are factory calibrated and stored in Calibration Words 1 and 2 (2009h and 200Ah). The Calibration Words do not participate in erase operations. The device can be erased without affecting the Calibration Words.
Unique Features of PIC16F720 and Its Applications
The PIC16F720 microcontroller is valued for its low-power design, integrated peripherals, and efficient instruction set. With on-chip oscillator, multiple I/O ports, ADC capabilities, and flexible timers, it finds applications in:
- Automotive systems such as dashboard modules and engine controllers.
- Industrial automation including motor drives, power supply regulation, and sensor interfaces.
- Consumer devices like home appliances, smart gadgets, and portable instruments.
- Medical electronics requiring compact and reliable embedded solutions.
These widespread uses make the recovery of firmware not only practical but often critical when upgrading or servicing hardware deployed in the field.

Conclusion
The ability to Break Chip PIC16F720 Firmware is an advanced yet vital service for anyone working with protected or encrypted embedded devices. Through carefully executed steps—ranging from cracking locked memory to decoding binary data—users can regain access to program files, flash archives, and source code that would otherwise remain hidden behind protective security measures. This process ensures continuity, supports innovation, and secures long-term control over embedded system design.