 Break AVR ATmega64A Binary
Break AVR ATmega64A Binary
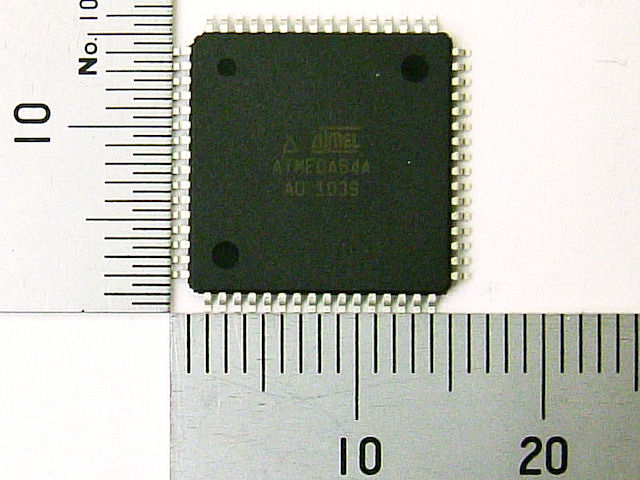
Break AVR ATmega64A Binary is a specialized engineering service designed to support manufacturers, system integrators, and maintenance teams that must legally regain access to embedded firmware when original development resources are unavailable. The AVR ATmega64A is a widely deployed 8-bit microcontroller known for its balanced performance, integrated flash and EEPROM memory, and flexible peripheral set. It is commonly used in industrial controllers, automation equipment, medical devices, smart instruments, and long-life consumer electronics.

In many of these products, the firmware binary or heximal program becomes a critical asset over time, especially when devices remain operational long after the original supplier or source code archive is lost.

We can Break AVR ATMEGA64A Binary, please view below AVR ATMEGA64A features for your reference:
The ATmega64A features on-chip flash, EEPROM, and SRAM, combined with multiple communication interfaces and low-power operation, making it ideal for embedded systems that require stability and long-term availability. To protect intellectual property, vendors often enable protected, locked, or encrypted security configurations that restrict access to firmware, source code, and internal memory data. While these protective mechanisms are effective for IP control, they can create serious obstacles during product refurbishment, failure analysis, migration, or compliance verification. Our service focuses on helping authorized clients attack, break, decode, or retrieve essential program files and embedded firmware in a controlled and professional manner, without disclosing sensitive technical details.
· High-performance, Low-power AVR® 8-bit Microcontroller
· Advanced RISC Architecture
– 130 Powerful Instructions – Most Single Clock Cycle Execution
– 32 x 8 General Purpose Working Registers + Peripheral Control Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
High Endurance Non-volatile Memory segments
– 64K Bytes of In-System Reprogrammable Flash program memory
– 2K Bytes EEPROM
– 4K Bytes Internal SRAM
– Write/Erase Cycles: 10,000 Flash/100,000 EEPROM
– Data retention: 20 years at 85°C/100 years at 25°C(1)
– Optional Boot Code Section with Independent Lock Bits
· In-System Programming by On-chip Boot Program
· True Read-While-Write Operation
– Up to 64K Bytes Optional External Memory Space
– Programming Lock for Software Security
– SPI Interface for In-System Programming
JTAG (IEEE std. 1149.1 Compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– Two Expanded 16-bit Timer/Counters with Separate Prescaler, Compare Mode, and Capture Mode
– Real Time Counter with Separate Oscillator
– Two 8-bit PWM Channels
– 6 PWM Channels with Programmable Resolution from 1 to 16 Bits
– 8-channel, 10-bit ADC
· 8 Single-ended Channels
· 7 Differential Channels
· 2 Differential Channels with Programmable Gain (1x, 10x, 200x)
– Byte-oriented Two-wire Serial Interface
– Dual Programmable Serial USARTs
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources when Break AVR
– Six Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, Standby and Extended Standby
– Software Selectable Clock Frequency
– ATmega103 Compatibility Mode Selected by a Fuse
– Global Pull-up Disable I/O and Packages
– 53 Programmable I/O Lines
– 64-lead TQFP and 64-pad QFN/MLF Operating Voltages
– 2.7 – 5.5V for ATmega64A Speed Grades
From a high-level perspective, recovering a secured AVR ATmega64A binary requires deep understanding of the MCU architecture, memory organization, and protection logic. Challenges often include locked flash regions, secured EEPROM blocks, and fragmented archive data that cannot be accessed through standard programming interfaces. Each case is different, and the difficulty depends on firmware size, security configuration, and device condition. Our engineers apply advanced analysis and controlled recovery workflows to clone or duplicate the required firmware, binary, or heximal file while preserving data integrity. The goal is not simply to copy memory, but to restore usable program archives that can support engineering, validation, or controlled reproduction.
The business value of our Break AVR ATmega64A Binary service lies in risk reduction and lifecycle continuity. End users benefit by avoiding costly redesigns, minimizing downtime, and extending the usable life of embedded products. Recovered firmware and memory data can be used for backup, migration to new hardware, compatibility testing, or regulated documentation. By offering a secure, discreet, and SEO-focused service model, we support industries that rely on embedded systems while respecting confidentiality and commercial requirements. Our role is to provide a reliable technical bridge between protected microcontrollers and real-world operational needs.