 Attack MCU TMS320F241PG Heximal
Attack MCU TMS320F241PG Heximal
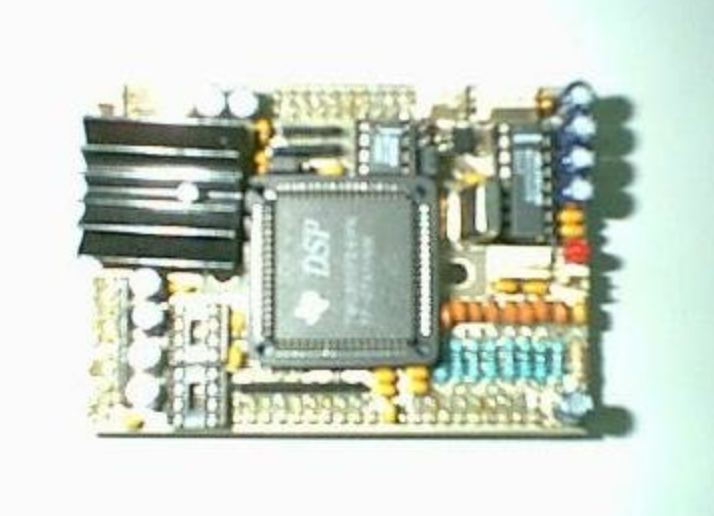
When a device relies on a Texas Instruments DSP such as the TMS320F241PG, the firmware stored in its on-chip memory is often the heart of the system — controlling timing, signal processing, and safety-critical loops. Our service, searchable under the keyword Attack MCU TMS320F241PG Heximal, helps authorized users restore, readout, decode, and recover the firmware/binary/heximal program and data from these protected or locked devices. We focus on lawful, confidential work that returns usable program images and high-level analysis without enabling misuse.
Legitimate needs to open, copy, clone, duplicate, or restore TMS320F241PG firmware commonly include: repairing equipment after firmware corruption; backing up archived program files for legacy support; migrating control software to replacement hardware; performing security audits; and recovering crucial calibration data or configuration archives. In many industrial settings, losing access to the embedded program can mean costly downtime — so secure recovery is essential.
We can Attack MCU TMS320F241PG Heximal, please view the MCU TMS320F241PG features below for your reference:
High-Performance Static CMOS Technology
D Includes the T320C2xx Core CPU
– Object-Compatible With the TMS320C2xx
– Source-Code-Compatible With TMS320C25
D Single 10-Bit Analog-to-Digital Converter
(ADC) Module With 8 Multiplexed Input Channels
D 26 Individually Programmable, Multiplexed
General-Purpose I / O (GPIO) Pins
– Upwardly Compatible With TMS320C5x
– 50-ns Instruction Cycle Time
Pin Compatible to Emulation Device
TMS320F241 (64-Pin/68-Pin)
Code Compatible to Emulation Devices TMS320F243 and TMS320F241
Commercial and Industrial Temperature Available

Memory
– 544 Words x 16 Bits of On-Chip Data/Program Dual-Access RAM (DARAM)
– 4K Words x 16 Bits of On-chip Program ROM Event-Manager Module
– Eight Compare/ Pulse-Width Modulation (PWM) Channels
– Two 16-Bit General-Purpose Timers With Six Modes, Including Continuous Up and Up / Down Counting
– Three 16-Bit Full Compare Units With Phase-Locked-Loop (PLL)-Based Clock Watchdog (WD) Timer Module
Serial Communications Interface (SCI);
Five External Interrupts (Power Drive Protection, Reset, NMI, and Two Maskable Interrupts)
Three Power-Down Modes for Low-Power
Operation
Scan-Based Emulation
Development Tools Available:
– Texas Instruments (TI) ANSI Compiler, Assembler / Linker, and
C-Source Debugger
– Full Range of Emulation Products
– Self-Emulation (XDS510)
– Third-Party Digital Motor Control and Fuzzy-Logic Development Support
68-Pin PLCC FN Package
64-Pin QFP PG Package
Deadband

– Three Capture Units (Two With Quadrature Encoder-Pulse Interface Capability)
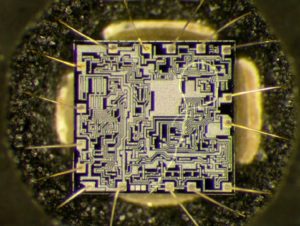
TMS320C2xx generation of 16-bit fixed-point DSPs.
The TMS320F241 device is fully compatible with the C242 to allow emulation during prototype development. (These two devices share similar core and peripherals.) This new family is optimized for digital motor / motion control applications
The DSP controllers combine the enhanced TMS320 architectural design of the ’C2xx core CPU for low-cost, high-performance processing capabilities and several advanced peripherals optimized for motor/motion control applications, These peripherals include the event manager module, which provides general-purpose timers and PWM registers to generate PWM outputs, and a single,10-bit analog-to-digital converter (ADC), which can perform conversion within 1 µs.
The TMS320 family and its variants like the F241PG are widely used across industries that require deterministic, high-performance signal processing and control:
- Motor drives and servo controllers (precision torque/speed loops).
- Power conversion and inverter systems (renewables, UPS, power supplies).
- Industrial automation (motion controllers, PLC peripherals).
- Advanced instrumentation and measurement systems requiring fast DSP math.
Because these applications often incorporate calibration tables, control algorithms, and safety logic, the flash/EEPROM contents are frequently treated as protected or secured assets.
What we provide (high level, non-actionable)
Our engagement is built around safe, authorized firmware recovery and analysis. Typical services include:
- Verified extraction of raw binary/heximal images from on-chip memory where permitted.
- Non-destructive validation and checksum checks of extracted archives.
- High-level disassembly and annotated summaries that convert raw dumps into readable assembly-level views and contextual commentary (not step-by-step bypass instructions).
- Support to restore devices to operation using recovered firmware, and assistance preparing migration packages for replacement hardware.
- Confidential handling and delivery of recovered program files and documented reports.

We do not provide step-by-step guidance for illegally circumventing manufacturer protections, nor do we assist unauthorized copying or distribution of copyrighted or safety-critical code.
General idea of the workflow (conceptual)
A responsible recovery project typically begins with device and chip identification, verification of ownership/authorization, and a risk assessment. Engineers then attempt non-destructive readout and validate the integrity of the extracted memory image. Once a stable dump is obtained, analysis and decoding transform the raw data into an intelligible program representation and recovery artifacts that customers can use for testing, repair, or redeployment.
Benefits and expected outcomes
Clients gain reduced downtime, secure backups of previously inaccessible firmware, and the ability to maintain and support legacy systems. Recovered heximal or binary files enable replication, authorized cloning, and safer migration strategies — all under controlled, legal terms.
Difficulties you may encounter
Challenges include layered manufacturer protections, partial data corruption, device variants with different memory maps, and the presence of proprietary encryption or integrity checks. Not all recoveries yield full source-level clarity; in many cases, only the binary/heximal archives and assembly-level annotations are recoverable.
Ethics, authorization & confidentiality
All projects require proof of ownership or explicit authorization. Work is performed under strict confidentiality and legal agreements; our goal is to unlock and restore embedded systems for legitimate, constructive purposes only.
If you need to Attack MCU TMS320F241PG Heximal for lawful recovery, migration, or audit, our team provides secure, professional support to retrieve and document embedded firmware while protecting your IP and operational continuity.