 Attack MCU ATmega162 Flash
Attack MCU ATmega162 Flash
Microchip’s ATmega162 is a powerful 8-bit microcontroller often chosen for industrial, automotive, and security-critical applications due to its reliability, performance, and flexible communication features. Designed with a dual-port SRAM interface, advanced interrupt structure, and multiple USARTs, this MCU is ideal for complex embedded systems where stability and efficiency are crucial. However, its protected memory structure often presents a serious barrier for engineers, developers, or analysts who need access to the original firmware, flash, or EEPROM contents.

At [Your Company Name], we offer professional services to attack MCU ATmega162 flash and recover its internal heximal or binary content. Whether the target system is locked, encrypted, or has active security fuses, our experienced team applies advanced hardware and software techniques to unlock, crack, and clone the internal program data for legitimate recovery, analysis, or duplication purposes.
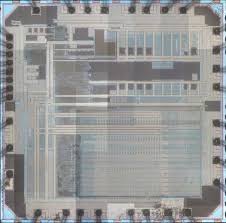
Attack MCU ATmega162 can help engineer to find out the location of security fuse bit then use laser cutting to remove it, and reset the status of Microcontroller from locked to unlocked;
Features
· High-performance, Low-power AVR® 8-bit Microcontroller
· Advanced RISC Architecture
– 131 Powerful Instructions – Most Single-clock Cycle Execution
– 32 x 8 General Purpose Working Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
Non-volatile Program and Data Memories
– 16K Bytes of In-System Self-programmable Flash Endurance: 10,000 Write/Erase Cycles
– Optional Boot Code Section with Independent Lock Bits

In-System Programming by On-chip Boot Program
True Read-While-Write Operation
– 512 Bytes EEPROM
Endurance: 100,000 Write/Erase Cycles
– 1K Bytes Internal SRAM
– Up to 64K Bytes Optional External Memory Space
8-bit
Microcontroller
with 16K Bytes
In-System
– Programming Lock for Software Security
JTAG (IEEE std. 1149.1 Compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– Two 16-bit Timer/Counters with Separate Prescalers, Compare Modes, and
Capture Modes
– Real Time Counter with Separate Oscillator
– Six PWM Channels
– Dual Programmable Serial USARTs
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with Separate On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Five Sleep Modes: Idle, Power-save, Power-down, Standby, and Extended Standby
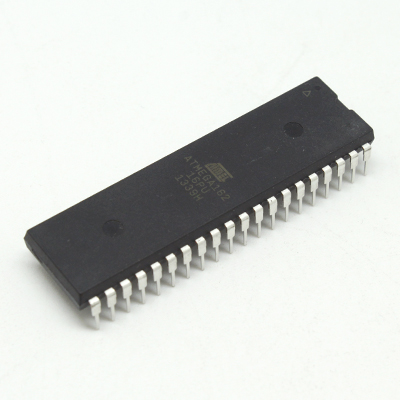
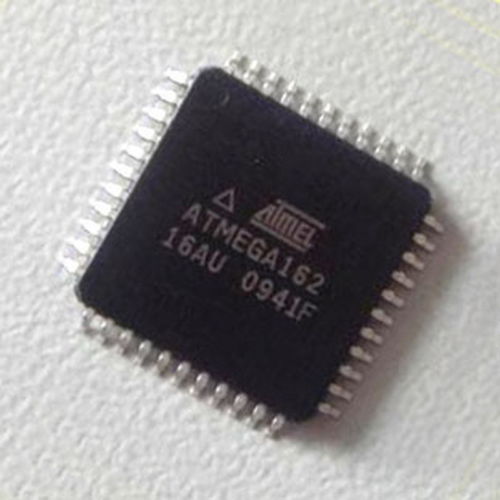
I/O and Packages
– 35 Programmable I/O Lines
– 40-pin PDIP, 44-lead TQFP, and 44-pad MLF
Operating Voltages
– 1.8 – 5.5V for ATmega162V
– 2.7 – 5.5V for ATmega162
Speed Grades
Programmable Flash
– 0 – 8 MHz for ATmega162V (see Figure 113 on page 265)
– 0 – 16 MHz for ATmega162 (see Figure 114 on page 265)
There are many situations where access to the firmware is essential:
- Lost original source code
- System reproduction or duplicate hardware development
- Reverse engineering for legacy support
- Decoding undocumented communication protocols
- Analyzing vulnerabilities for cybersecurity testing
The ATmega162 MCU stores its program in a flash memory block that can be fused for readout protection. Once this secured protection is activated, normal methods won’t allow developers to retrieve the original data or files. However, with our specialized capability, we can break these protective mechanisms and retrieve the internal code safely.
Our services are tailored for cases where the internal memory must be accessed due to necessity—such as system upgrades, part replacement, or system migration. We use non-invasive and semi-invasive hardware-assisted analysis to copy or clone the firmware from the embedded device.
We support:
- Full binary and hex extraction
- EEPROM and flash dump separation
- Custom bootloader readout bypass techniques
- Memory structure mapping and source code reconstruction (in C or ASM)
Once extracted, the firmware can be analyzed, decompiled, or ported to compatible systems. We also provide complete documentation of the process, allowing your engineering team to integrate or redeploy the program efficiently.
The ATmega162 is widely used in:
- Industrial controllers and HMI interfaces
- Consumer electronics with legacy serial protocols
- Secure automotive modules
- Robotics and intelligent I/O boards
- Customized smart devices using USART/SPI/I2C communication
Its dual UARTs, internal oscillator, watchdog, and flexible interrupt system make it uniquely suited for complex serial processing. Unfortunately, this also means that when firmware becomes inaccessible, the entire system may be rendered unusable—unless the memory can be restored or duplicated.
All our work is performed under strict confidentiality and aligned with legal compliance. We only provide our services for legitimate purposes such as recovery, maintenance, migration, and research—with client authorization or ownership proof required.
Conclusion
If you’re working with a locked or protected ATmega162 microcontroller and need to attack its flash to recover valuable data, CIRCUIT ENGINEERING CO., LTD is your trusted partner. Our deep expertise in reverse engineering and secure memory extraction ensures reliable access to otherwise unreachable firmware and files.
Contact us today to discuss your project and regain control over your embedded systems.