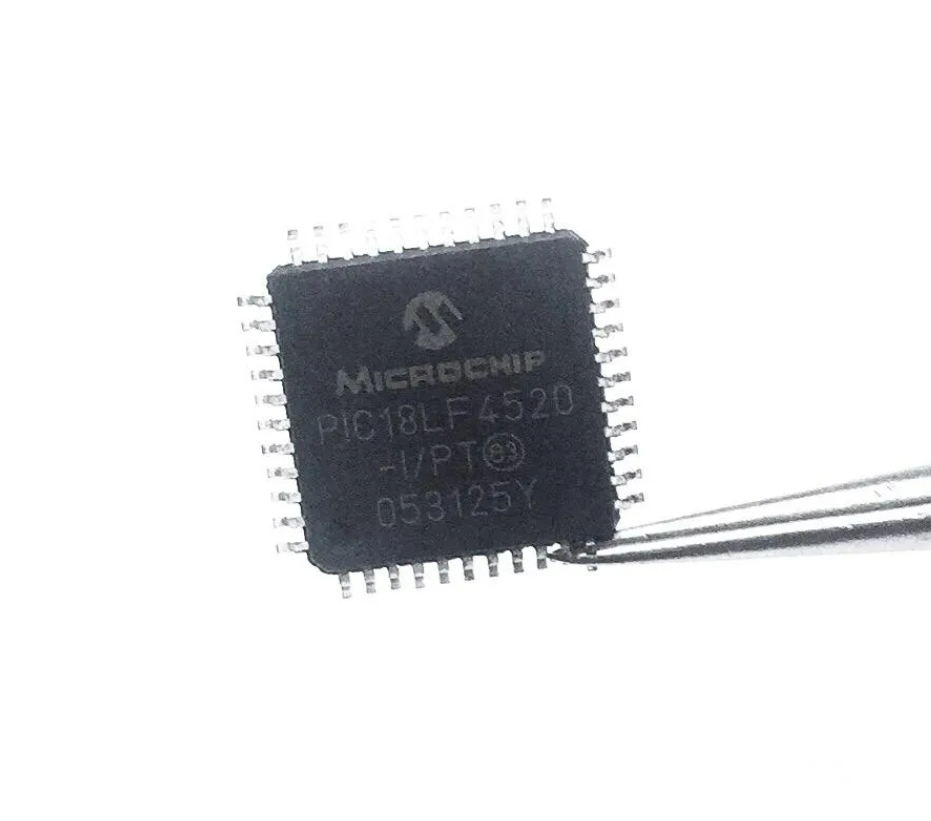
 Attack IC PIC18LF4520 Program
Attack IC PIC18LF4520 Program
The MICROCHIP PIC18LF4520 is a powerful 8-bit microcontroller widely used in industrial, automotive, and consumer electronics applications. Known for its rich peripheral set, low power consumption, and high-performance features, this embedded chip is commonly implemented in critical systems requiring reliable and long-lasting control logic. However, when firmware becomes protected, encrypted, or locked, recovering the underlying program, binary, or source code can be a daunting task—especially for system integrators, engineers, or developers dealing with legacy systems, code loss, or product redesign.

At Circuit Engineering CO., LTD, we specialize in professional services to attack IC PIC18LF4520 program and help clients restore, crack, hack, or decrypt the hidden firmware from the chip’s internal memory. Whether it is the main flash, EEPROM, or data archive, our expert techniques allow us to safely open, unlock, and retrieve the essential heximal file needed for modification, backup, or duplication.
Attack IC PIC18LF4520 protective memory, cut off the security fuse of the memory and extract Program and data from the flash and eeprom, Clone the content to other new Microcontroller PIC18LF4520 for the same functions;
Power Management Features:
Peripheral Highlights (Continued):
Run: CPU on, Peripherals on
Idle: CPU off, Peripherals on
Sleep: CPU off, Peripherals off
Ultra Low 50nA Input Leakage
Run mode Currents Down to 11 ìA Typical
Idle mode Currents Down to 2.5 ìA Typical
Sleep mode Current Down to 100 nA Typical
Timer1 Oscillator: 900 nA, 32 kHz, 2V
Watchdog Timer: 1.4 ìA, 2V Typical
Two-Speed Oscillator Start-up
Unlike basic read-out attempts, our approach to attacking the PIC18LF4520 program involves a combination of low-level hardware analysis, voltage glitching, and advanced microprobing when necessary. These techniques are designed to bypass the chip’s security fuses and read-protection mechanisms that usually prevent access to secured firmware. Once the heximal binary is extracted, we can decode and disassemble it, converting the firmware into readable formats for debugging or porting.

We understand that many clients may have lost their only copy of a program or inherited a product without source code access. That’s why we provide tailored solutions that go beyond basic data retrieval. Our services are designed to help:
- Recover lost firmware from damaged or legacy devices.
- Clone or duplicate a protected controller for scaling or prototyping.
- Reverse-engineer encrypted binaries to re-develop systems when documentation is missing.
- Unlock access to EEPROM data that may contain important system calibration or runtime parameters.
· Master Synchronous Serial Port (MSSP) module
Supporting 3-Wire SPI (all 4 modes) and I2C™ Master and Slave modes
· Enhanced Addressable USART module:
– Supports RS-485, RS-232 and LIN/J2602
– RS-232 operation using internal oscillator
block (no external crystal required)
– Auto-wake-up on Start bit
– Auto-Baud Detect
· 10-Bit, up to 13-Channel Analog-to-Digital (A/D)
Flexible Oscillator Structure:
· Four Crystal modes, up to 40 MHz
· 4x Phase Lock Loop (PLL) – Available for Crystal and Internal Oscillators
· Two External RC modes, up to 4 MHz
· Two External Clock modes, up to 40 MHz
· Internal Oscillator Block:
– Fast wake from Sleep and Idle, 1 ìs typical
– 8 use-selectable frequencies, from 31 kHz to 8 MHz
– Provides a complete range of clock speeds from 31 kHz to 32 MHz when used with PLL
– User-tunable to compensate for frequency drift
· Secondary Oscillator using Timer1 @ 32 kHz
· Fail-Safe Clock Monitor:
– Allows for safe shutdown if peripheral clock stops
Peripheral Highlights:
Converter module:
– Auto-acquisition capability
– Conversion available during Sleep
· Dual Analog Comparators with Input Multiplexing
· Programmable 16-Level High/Low-Voltage Detection (HLVD) module:
– Supports interrupt on High/Low-Voltage Detection
Special Microcontroller Features:
· C Compiler Optimized Architecture:
– Optional extended instruction set designed to optimize re-entrant code
· 100,000 Erase/Write Cycle Enhanced Flash
Program Memory Typical
· 1,000,000 Erase/Write Cycle Data EEPROM
Memory Typical
· Flash/Data EEPROM Retention: 100 Years Typical
· Self-Programmable under Software Control
High-Current Sink/Source 25 mA/25 mA
Three Programmable External Interrupts
Four Input Change Interrupts
Up to 2 Capture/Compare/PWM (CCP) modules,

· Priority Levels for Interrupts
· 8 x 8 Single-Cycle Hardware Multiplier
· Extended Watchdog Timer (WDT):
– Programmable period from 4 ms to 131s one with Auto-Shutdown (28-pin devices)
· Enhanced Capture/Compare/PWM (ECCP) module (40/44-pin devices only):
– One, two or four PWM outputs
– Selectable polarity
– Programmable dead time
– Auto-shutdown and auto-restart
· Single-Supply 5V In-Circuit Serial
Programming™ (ICSP™) via Two Pins
· In-Circuit Debug (ICD) via Two Pins
· Wide Operating Voltage Range: 2.0V to 5.5V
· Programmable Brown-out Reset (BOR) with Software Enable Option
The PIC18LF4520 stands out with features like nanoWatt technology, 10-bit ADC, 32 KB program memory, and dual USARTs—making it suitable for low-power and battery-powered applications. It is often deployed in secured embedded systems such as medical devices, motor controllers, industrial sensors, and power monitoring units. When these systems become inaccessible due to locked or encrypted firmware, downtime or redevelopment costs can escalate quickly.
That’s where our expertise provides immense value. Our ability to crack and extract locked firmware files from the PIC18LF4520 saves time, preserves original design intent, and allows for safe system replication or migration. We treat every engagement with the highest level of confidentiality. Our firmware attack and recovery services are designed for legitimate owners, OEMs, and system maintainers who need access to critical firmware for lawful purposes such as repair, maintenance, or migration. We do not support or condone unauthorized duplication of intellectual property.
If you need help attacking the IC PIC18LF4520 program, whether to decrypt firmware, duplicate a chip, or retrieve locked data, our expert team is ready to assist. Let us help you restore control over your embedded systems and provide solutions to move your project forward.