 Attack IC PIC16F57 Program
Attack IC PIC16F57 Program
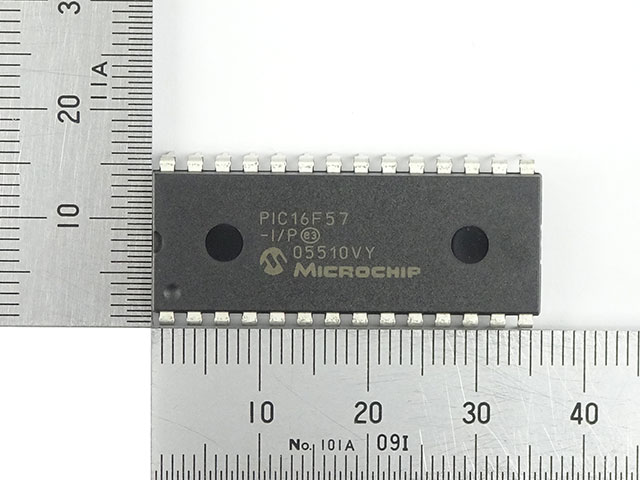
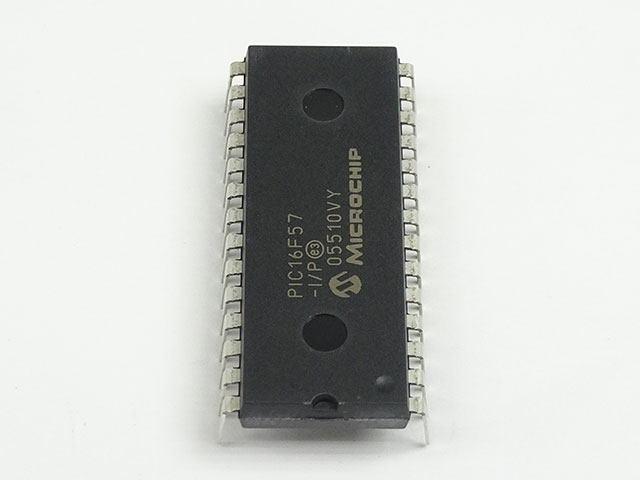
The Microchip PIC16F57 is a robust 8-bit microcontroller widely used in consumer electronics, industrial controllers, automotive modules, and various embedded systems. With its compact architecture, onboard I/O, and reliable performance, it is a preferred solution in many secured or proprietary control units. However, the firmware, binary, or heximal files stored within these chips are often protected or encrypted, making them inaccessible without expert intervention.
At Circuit Engineering Co., LTD, we provide professional services to attack IC PIC16F57 program protection mechanisms, enabling clients to recover, copy, or restore the original program data. Whether the chip is locked, secured, or obfuscated, our team is equipped with the latest tools and methodologies to crack and decrypt the internal memory, including flash and EEPROM sections.
The PIC16F5X from Microchip Technology is a family of low-cost, high-performance, 8-bit, fully static, Flash based CMOS microcontrollers. It employs a RISC architecture with only 33 single-word/single-cycle instructions. All instructions are single cycle except for program branches which take two cycles by Attack IC PIC16F57 Program. The PIC16F5X delivers performance an order of magnitude higher than its competitors in the same price category.
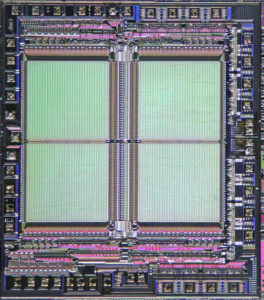
The 12-bit wide instructions are highly symmetrical resulting in 2:1 code compression over other 8-bit microcontrollers in its class. The easy-to-use and easy-to-remember instruction set reduces development time significantly.
The PIC16F5X products are equipped with special features that reduce system cost and power requirements. The Power-on Reset (POR) and Device Reset Timer (DRT) eliminate the need for external Reset circuitry.
There are four oscillator configurations to choose from, including the power-saving LP (Low Power) oscillator and cost saving RC oscillator. Power-saving Sleep mode, Watchdog Timer and code protection features improve system cost, power and reliability.

The PIC16F57 is a baseline 12-bit core MCU with a 2K x 12-word flash program memory, 72 bytes of RAM, and 16 I/O pins. It is notable for its simplicity and low cost, making it ideal for mass-produced applications like remote controllers, basic logic units, small motors, timers, and more. In legacy systems where documentation has been lost or when a supplier no longer provides source support, reverse engineering becomes the only solution to continue development or maintenance.
Our service is especially valuable to:
- OEMs needing to duplicate legacy designs.
- Engineers aiming to clone or migrate control logic to a modern platform.
- Security analysts looking to decode encrypted systems for vulnerability assessments.
- Researchers interested in system behavior analysis or functional replication.
The PIC16F5X products are supported by a full-featured macro assembler, a software simulator, a low-cost development programmer and a full featured programmer. All the tools are supported on IBM® PC and compatible machines.
We begin with physical or electrical-level attacks to bypass code protection bits embedded in the PIC16F57. Once access is achieved, we dump the program file—usually in heximal format—from the internal memory. After extraction, we optionally provide detailed analysis, disassembly, and conversion to assembly or even C-style source code, depending on the client’s needs.
Whether your chip is locked, masked, or fused, we have experience dealing with a wide range of protected microcontrollers and can offer customized recovery or cloning solutions.
The PIC16F5X series fits perfectly in applications ranging from high-speed automotive and appliance motor control to low-power remote transmitters/receivers, pointing devices and telecom processors. The Flash technology makes customizing application programs from Attack IC PIC16F57 Program (transmitter codes, motor speeds, receiver frequencies, etc.) extremely fast and convenient.
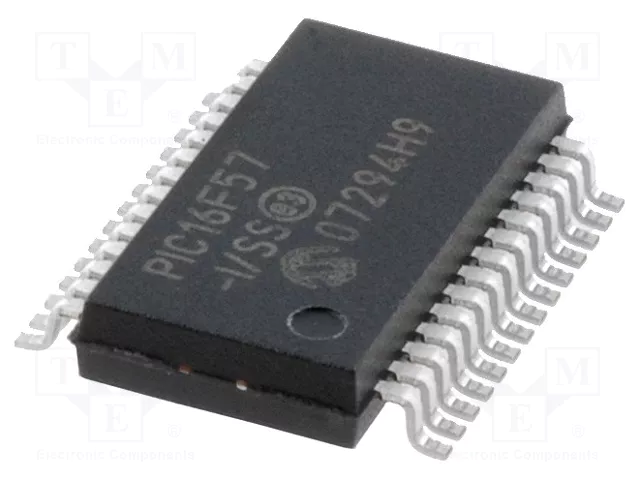
The small footprint packages, for through hole or surface mounting, make this microcontroller series perfect for applications with space limitations. Low-cost, low-power, high performance, ease of use and I/O flexibility make the PIC16F5X series very versatile, even in areas where no microcontroller use has been considered before (e.g., timer functions, replacement of “glue” logic in larger systems, co-processor applications).
It’s important to understand that our service is tailored for legitimate recovery, engineering evaluation, or system restoration purposes. Clients rely on us not only for our technical proficiency but also for our professional handling of confidential projects. All engagements are strictly private and aligned with legal and ethical standards.
If you’re facing a development halt due to inaccessible code within a PIC16F57, or if you’re looking to unlock archived data or restore a functional system from a non-functional unit, we’re here to help. With our “Attack IC PIC16F57 Program” service, we help you regain control of your systems by retrieving the irreplaceable firmware buried deep inside secured embedded chips.
Let us help you bring the hidden logic back to light. Contact us today to discuss your project in confidence.