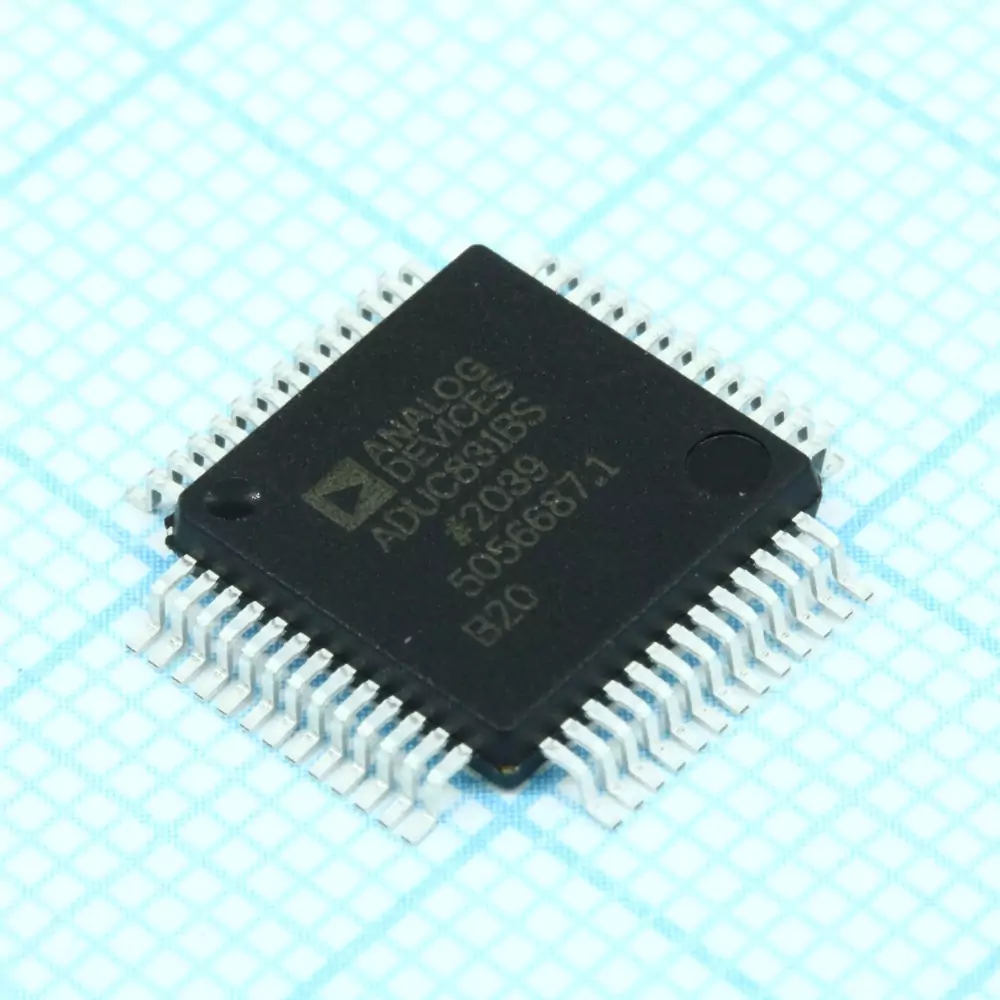
Attack IC ADUC831BSZ Firmware
Attack IC ADUC831BSZ Firmware
The Analog Devices ADUC831BSZ is a powerful single-chip microcontroller that integrates a high-performance 8051 core with precision analog-to-digital converters and flash memory. Widely adopted in industrial automation, instrumentation, automotive electronics, and consumer devices, this chip is often deployed in environments where reliability and accuracy are paramount. To protect proprietary intellectual property, manufacturers frequently enable protective fuse bits and implement locked or encrypted firmware. This creates challenges when users need to access, restore, or modify the binary, heximal, or source code stored in its flash memory or EEPROM.

The Need for Firmware Recovery
There are many scenarios where end users require access to the firmware program of the ADUC831BSZ. For example:
- Recovering lost or corrupted data archives.
- Migrating existing systems to new hardware platforms.
- Conducting security audits or patching vulnerabilities.
- Cloning or duplicating a system for production scaling.
In such cases, the demand arises for a professional service to attack IC ADUC831BSZ firmware in order to crack, hack, decode, or decrypt the locked system and extract the protected program file.
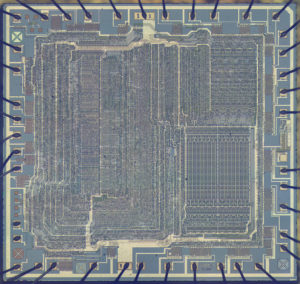
General Steps of Unlocking and Extraction
Breaking the secured firmware of the ADUC831BSZ involves carefully engineered procedures. The most general steps include:
- Chip Identification – Recognizing the exact microcontroller variant and analyzing its fuse bit configuration.
- Protection Analysis – Studying the enabled security features, whether it involves simple code-lock mechanisms or encrypted flash memory.
- Fuse Bit Disablement – Using advanced techniques to bypass or disable protective bits without damaging the device.
- Firmware Dumping – Extracting the heximal file or binary program from the flash and EEPROM memory.
- Disassembly and Decryption – Decoding the low-level instructions, restoring the firmware to a usable format, and if required, reconstructing C/C++ source code.
These steps demand a combination of deep expertise in embedded systems and custom-engineered hardware interfaces to ensure successful recovery.
Unique Features of ADUC831BSZ

The ADUC831BSZ stands out due to:
- Integrated high-precision ADC/DAC for mixed-signal processing.
- On-chip flash memory with programmable protection levels.
- Low-power consumption, making it suitable for battery-powered devices.
- Enhanced embedded security, designed to safeguard proprietary program data.
While these features benefit developers, they also increase the difficulty of unlocking or copying the firmware once security measures are enabled.
Applications of Firmware Extraction
By successfully attacking and unlocking the firmware, end users gain the ability to:
- Restore original program files from damaged devices.
- Copy and clone embedded systems for legacy support.
- Duplicate memory archives for large-scale deployment.
- Perform reverse engineering for debugging, compatibility testing, or academic research.

Such capabilities are especially valuable in industrial control systems, medical instrumentation, automotive modules, and consumer electronics, where firmware access is often the key to extending the lifecycle of equipment or ensuring continued support.
Conclusion
The process to attack IC ADUC831BSZ firmware is not trivial, given the device’s protected and secured architecture. However, with advanced methods, it is possible to unlock, open, crack, and decode the embedded binary program stored inside its memory. The recovered heximal data can then be restored into functional form, enabling duplication, modification, or further development. This service provides clients with the essential access required to keep their embedded systems functional, optimized, and future-ready.