 Attack Chip PIC16C622A Software
Attack Chip PIC16C622A Software
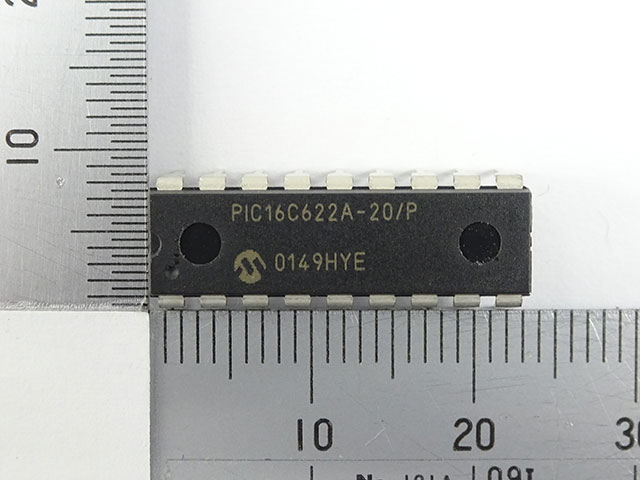
The Microchip PIC16C622A remains a widely deployed 8-bit MCU across consumer electronics, industrial automation, automotive interfaces, security devices, sensor modules, and legacy embedded systems. Its reliability, compact architecture, and stable flash and eeprom handling make it a long-lasting favorite among engineers. However, once development archives or source code are lost, the internal software becomes extremely difficult to access—especially when the chip is in a protected, encrypted, or fully locked configuration. Our specialized service under the topic Attack Chip PIC16C622A Software is designed to help legitimate product owners safely retrieve, clone, or duplicate the MCU’s original firmware, without revealing or disclosing any sensitive technical methods.

Industrial Importance of the PIC16C622A
The PIC16C622A delivers a balance of low cost, low power usage, and versatile I/O features. This makes it a common choice in:
- Portable electronic products
- Access control, authentication, and smart security hardware
- Motor controllers and instrumentation devices
- Home appliances and small embedded consumer systems
- Customized OEM modules with long production cycles
In many of these applications, the internal binary, heximal, and configuration memory contain unique logic, calibration routines, and tailored program structures essential for stable system performance.

The high performance of the PIC16C62X family can be attributed to a number of architectural features commonly found in RISC microprocessors which is critical feature for Attack Chip PIC16C622A Software. To begin with, the PIC16C62X uses a Harvard architecture, in which, program and data are accessed from separate memories using separate busses. This improves bandwidth over traditional von Neumann architecture where program and data are fetched from the same memory. Separating program and data memory further allows instructions to be sized differently than 8-bit wide data word. Instruction opcodes are 14-bits wide making it possible to have all single word instructions.
A 14-bit wide program memory access bus fetches a 14-bit instruction in a single cycle. A two-stage pipeline overlaps fetch and execution of instructions.
Consequently, all instructions (35) execute in a single-cycle (200 ns @ 20 MHz) except for program branches. The PIC16C620A and PIC16CR620A address 512 x 14 on-chip program memory. The PIC16C621(A) addresses 1K x 14 program memory. The PIC16C622(A) addresses 2K x 14 program memory. All program memory is internal.
The PIC16C62X can directly or indirectly address its register files or data memory. All special function registers including the program counter are mapped in the data memory. The PIC16C62X have an orthogonal (symmetrical) instruction set that makes it possible to carry out any operation on any register using any addressing mode in order to Attack Chip PIC16C622A Software. This symmetrical nature and lack of ‘special optimal situations’ make programming with the PIC16C62X simple yet efficient. In addition, the learning curve is reduced significantly.
The PIC16C62X devices contain an 8-bit ALU and working register. The ALU is a general purpose arithmetic unit. It performs arithmetic and Boolean functions between data in the working register and any register file.
The ALU is 8-bit wide and capable of addition, subtraction, shift and logical operations. Unless otherwise mentioned, arithmetic operations are two’s complement in nature. In two-operand instructions, typically one operand is the working register (W register). The other operand is a file register or an immediate constant when Unlock Microcontroller. In single operand instructions, the operand is either the W register or a file register.

The W register is an 8-bit working register used for ALU operations. It is not an addressable register Depending on the instruction executed, the ALU may affect the values of the Carry (C), Digit Carry (DC), and Zero (Z) bits in the STATUS register. The C and DC bits operate as a Borrow and Digit Borrow out bit, respectively, bit in subtraction. See the SUBLW and SUBWF instructions for examples.
Our Service: Safe and Controlled Recovery of Embedded Software
We help businesses and engineers who need to break through inaccessible or obsolete MCU barriers to recover their own program files. Our objective is not unauthorized hacking but legitimate data restoration for owners who have lost the original design file or development archive.
Our service includes:
- Chip evaluation to confirm feasibility
- High-level security assessment before any attack or decode operation
- Optional non-destructive techniques or advanced decapsulation, depending on chip condition
- Secure extraction of internal firmware, calibration data, or eeprom contents
- Output of a clean, validated binary or heximal program ready for production or system repair
All internal procedures remain confidential, and we do not share technical details of how protections are unlocked.
General Concept of the Recovery Process (Non-Technical Overview)
Recovering embedded software from a secured PIC16C622A involves precisely controlled steps that may include reading device states, analyzing memory integrity, and applying specialized methods to decode or retrieve protected data. The goal is always to preserve the original program while avoiding any physical damage to the chip.
Why End-Users Choose This Service
Customers depend on this recovery solution for several business-critical reasons:
- Reviving production lines when development source code is lost
- Eliminating high redesign costs for legacy devices
- Ensuring long-term serviceability for field-deployed equipment
- Restoring intellectual property already paid for and designed internally
- Maintaining competitive advantage by controlling system logic
The ability to clone or duplicate the recovered firmware ensures product continuity without forced redesign.
Technical Challenges You Might Encounter
Some PIC16C622A units exhibit difficulties such as worn flash, degraded memory, heavy encrypted protections, or complex protective configurations. These conditions require precise handling to avoid partial or corrupted data output. Our team is experienced in processing such cases with the highest reliability.