 Attack MCU PIC16F887 Program
Attack MCU PIC16F887 Program
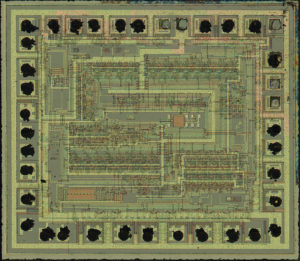
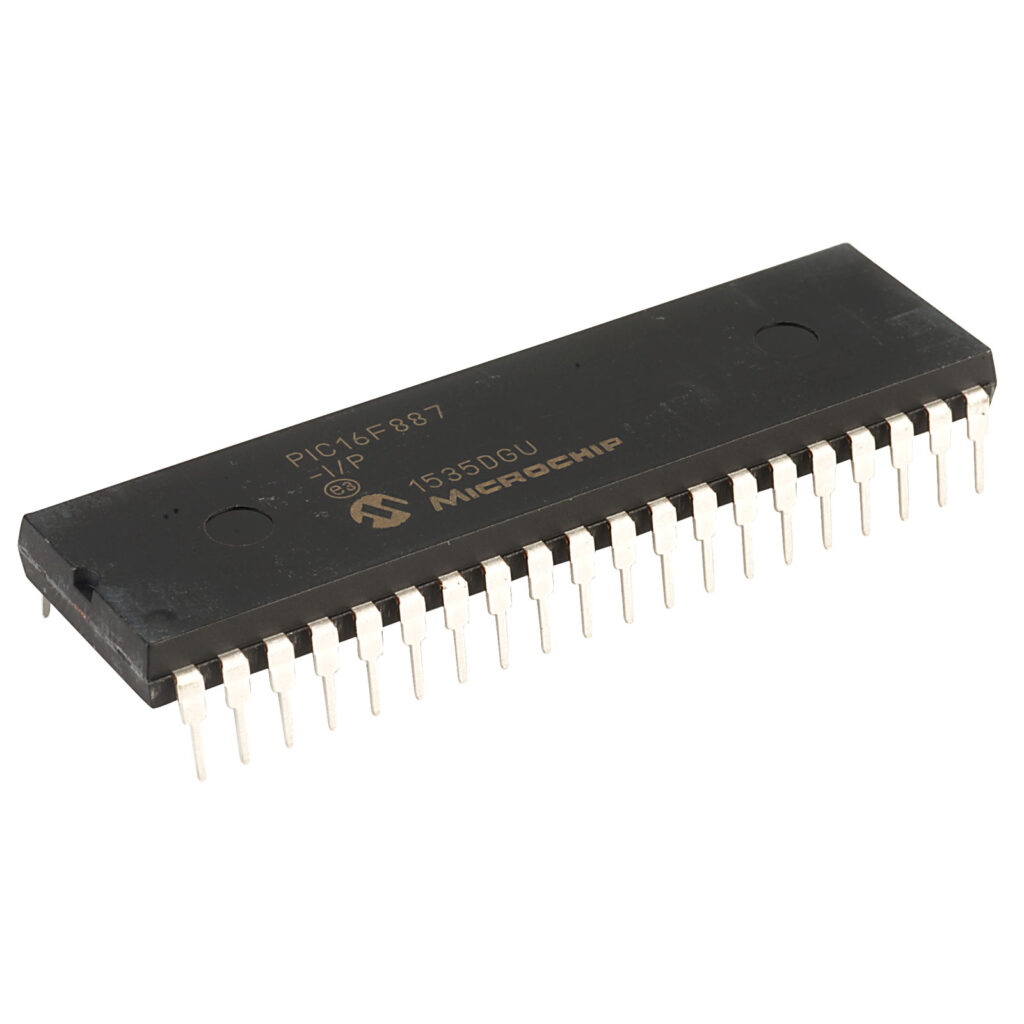
The Microchip PIC16F887 microcontroller is widely used in embedded systems for industrial, automotive, and consumer applications. Known for its versatility, low power consumption, and built-in peripherals, this 8-bit MCU features flash memory, EEPROM, and an internal oscillator, making it a popular choice for compact and cost-effective designs. However, its widespread use in protected and secured systems also means that its internal program and data are often locked or encrypted to prevent tampering or duplication.

At circuit engineering co.,ltd, we offer advanced services to attack MCU PIC16F887 program protections and help clients restore, crack, or copy the original heximal firmware and binary contents. Whether you’ve lost the original source, need to clone a locked device, or require a duplicate for maintenance or migration, our reverse engineering solutions provide access to the flash, EEPROM, and program memory of secured PIC16F887 microcontrollers.
Attack MCU PIC16F887 tamper resistance system and readout the Program and data from its flash memory and eeprom memory, clone firmware to new IC which will provide the same functions as original Microcontroller PIC16F887;
Module: Analog-To-Digital Converter (ADC) Module
Selecting the VP6 reference as the analog input source (CHS<3:0> = 1111) for the ADC conversion after sampling another analog channel with input voltages approximately greater than 3.6V can temporarily disturb the HFINTOSC oscillator.
4. Module: MSSP (SPI Master Mode)
With MSSP in SPI Master mode, FOSC/64 or Timer2/2 clock rate and CKE = 0, a write collision may occur if SSPBUF is loaded immediately after the transfer is complete after Attack MCU. A delay may be required after the MSSP Interrupt Flag bit, SSPIF, is set or the Buffer Full bit, BF, is set and before writing SSPBUF. If the delay is insufficiently short, a write register and NOT during the start of an actual ADC conversion using the GO/DONE bit in the ADCON0 register.
Microchip has integrated multiple protection mechanisms into the PIC16F887 to prevent unauthorized access. From code protection bits to memory locking, these security features are designed to make decrypting or decoding the firmware difficult for the average user. However, with years of hands-on experience and access to proprietary techniques and tools, our engineering team can hack these barriers and retrieve the original data, even from obfuscated or heavily encrypted firmware images.
We don’t simply dump raw memory—we provide complete, structured hex files or even human-readable source code where possible. Our process may involve full-chip readout, flash memory analysis, EEPROM data extraction, and program reconstruction, ensuring nothing critical is left behind.
This only occurs when selecting the VP6 reference ADC channel using the CHS<3:0> bits in the ADCON0 collision may occur as indicated by the WCOL bit being set.
Select an ADC channel with input voltages lower than 3.6V prior to selecting the VP6 reference voltage input. Any analog channel can be used, even if that channel is configured as a digital I/O (configured as an output) that is driving the output pin low when Attack MCU. An alternative is to configure the CVREF module to output a voltage less than 3.6V and then selecting that analog channel CHS<3:0> = 1110 as the analog input source.
Add a software delay of one SCK period after detecting the completed transfer and prior to updating the SSPBUF contents. Verify the WCOL bit is clear after writing SSPBUF. If the WCOL is set, clear the bit in software and rewrite the SSPBUF register.
Date Codes that pertain to this issue:
All engineering and production devices.
Affected Silicon Revisions
The PIC16F887 is widely appreciated for:
- 14-bit instruction set with 368 bytes of RAM and 256 bytes of EEPROM
- 8K x 14 words of Flash program memory
- 35 flexible I/O pins and support for multiple communication protocols (USART, SPI, I2C)
- Integrated ADCs, comparators, and timers
- Low power sleep modes for energy-sensitive applications
This embedded chip is commonly found in:
- Industrial sensor systems
- Smart home controllers
- HVAC controllers
- Educational development boards
- Low-cost automation devices
Due to its versatility, it’s often reused across multiple projects—making it especially frustrating when firmware is locked or when original source code is lost.
Our clients come from diverse industries—repair technicians, industrial OEMs, system integrators, and even researchers. We offer personalized consultation and confidential service to ensure that your objectives are met, whether you need to open a firmware file, clone a working board, or duplicate a system before a hardware refresh.
Our full service includes:
- Decryption and decoding of protected PIC16F887 firmware
- Memory dump and recovery of hex/binary files
- Reverse engineering of flash and EEPROM contents
- Optional conversion to partial or full C-like source code
If you need to attack MCU PIC16F887 program security for legitimate repair, recovery, or development purposes, our service delivers reliable, efficient, and professional support. We understand the complexity of protected embedded systems and are ready to help you regain control of your devices by unlocking valuable program archives and firmware data.
Contact Circuit Engineering CO., LTD today to learn more or schedule a consultation.